S. M. NAM ET AL.
Copyright © 2011 SciRes. *******
361
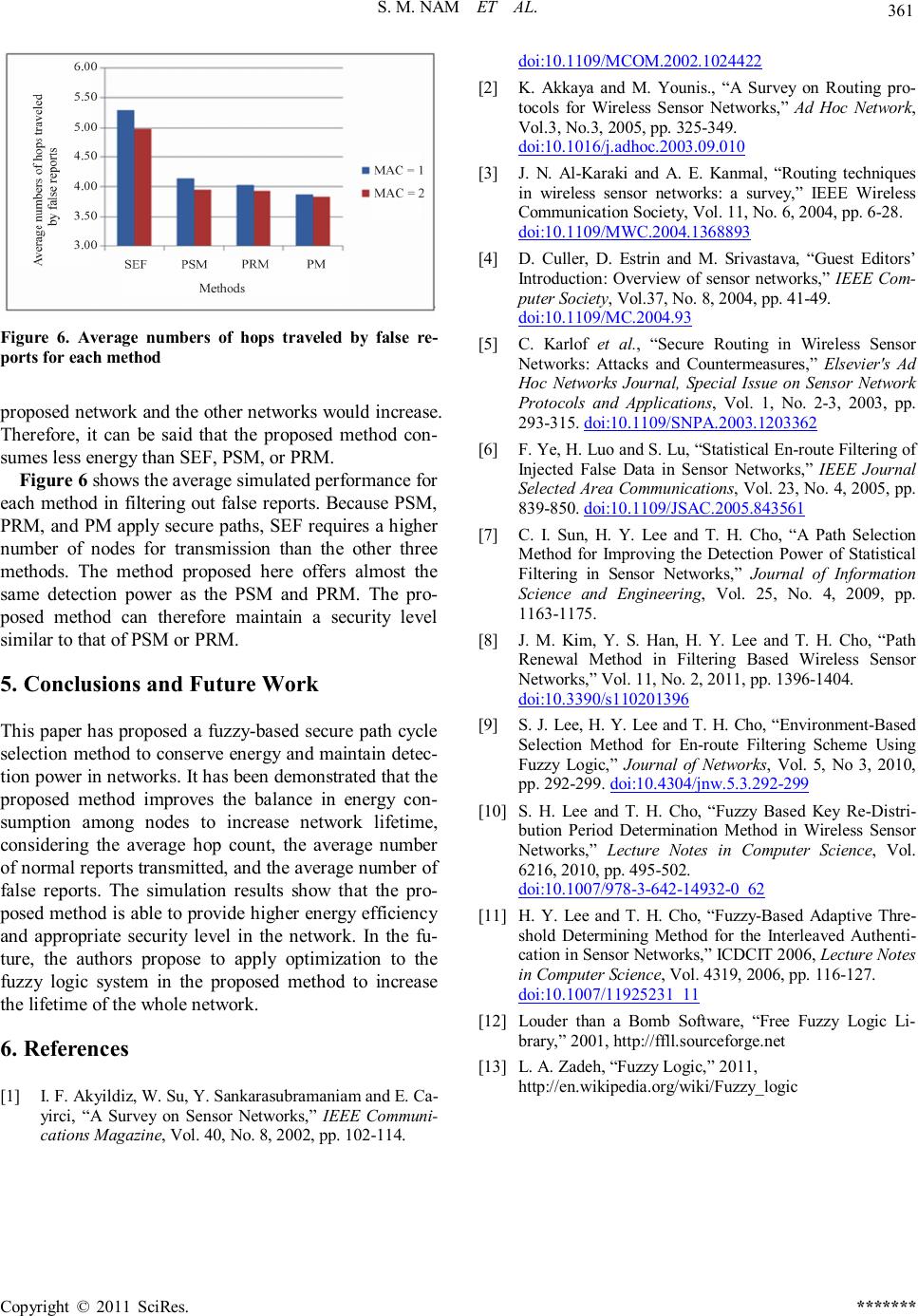
Figure 6. Average numbers of hops traveled by false re-
ports for each method
proposed network and the other networks would increase.
Therefore, it can be said that the proposed method con-
sumes less energy than SEF, PSM, or PRM.
Figure 6 shows the average simulated performance for
each method in filtering out false reports. Because PSM,
PRM, and PM apply secure paths, SEF requires a higher
number of nodes for transmission than the other three
methods. The method proposed here offers almost the
same detection power as the PSM and PRM. The pro-
posed method can therefore maintain a security level
similar to that of PSM or PRM.
5. Conclusions and Future Work
This paper has proposed a fuzzy-based secure path cycle
selection method to conserve energy and maintain detec-
tion power in networks. It has been demonstrated that the
proposed method improves the balance in energy con-
sumption among nodes to increase network lifetime,
considering the average hop count, the average number
of normal reports transmitted, and the average number of
false reports. The simulation results show that the pro-
posed method is able to provide higher energy efficiency
and appropriate security level in the network. In the fu-
ture, the authors propose to apply optimization to the
fuzzy logic system in the proposed method to increase
the lifetime of the whole network.
6. References
[1] I. F. Akyildiz, W. Su, Y. Sankarasubramaniam and E. Ca-
yirci, “A Survey on Sensor Networks,” IEEE Communi-
cations Magazine, Vol. 40, No. 8, 2002, pp. 102-114.
doi:10.1109/MCOM.2002.1024422
[2] K. Akkaya and M. Younis., “A Survey on Routing pro-
tocols for Wireless Sensor Networks,” Ad Hoc Network,
Vol.3, No.3, 2005, pp. 325-349.
doi:10.1016/j.adhoc.2003.09.010
[3] J. N. Al-Karaki and A. E. Kanmal, “Routing techniques
in wireless sensor networks: a survey,” IEEE Wireless
Communication Society, Vol. 11, No. 6, 2004, pp. 6-28.
doi:10.1109/MWC.2004.1368893
[4] D. Culler, D. Estrin and M. Srivastava, “Guest Editors’
Introduction: Overview of sensor networks,” IEEE Com-
puter Society, Vol.37, No. 8, 2004, pp. 41-49.
doi:10.1109/MC.2004.93
[5] C. Karlof et al., “Secure Routing in Wireless Sensor
Networks: Attacks and Countermeasures,” Elsevier's Ad
Hoc Networks Journal, Special Issue on Sensor Network
Protocols and Applications, Vol. 1, No. 2-3, 2003, pp.
293-315. doi:10.1109/SNPA.2003.1203362
[6] F. Ye, H. Luo and S. Lu, “Statistical En-route Filtering of
Injected False Data in Sensor Networks,” IEEE Journal
Selected Area Communications, Vol. 23, No. 4, 2005, pp.
839-850. doi:10.1109/JSAC.2005.843561
[7] C. I. Sun, H. Y. Lee and T. H. Cho, “A Path Selection
Method for Improving the Detection Power of Statistical
Filtering in Sensor Networks,” Journal of Information
Science and Engineering, Vol. 25, No. 4, 2009, pp.
1163-1175.
[8] J. M. Kim, Y. S. Han, H. Y. Lee and T. H. Cho, “Path
Renewal Method in Filtering Based Wireless Sensor
Networks,” Vol. 11, No. 2, 2011, pp. 1396-1404.
doi:10.3390/s110201396
[9] S. J. Lee, H. Y. Lee and T. H. Cho, “Environment-Based
Selection Method for En-route Filtering Scheme Using
Fuzzy Logic,” Journal of Networks, Vol. 5, No 3, 2010,
pp. 292-299. doi:10.4304/jnw.5.3.292-299
[10] S. H. Lee and T. H. Cho, “Fuzzy Based Key Re-Distri-
bution Period Determination Method in Wireless Sensor
Networks,” Lecture Notes in Computer Science, Vol.
6216, 2010, pp. 495-502.
doi:10.1007/978-3-642-14932-0_62
[11] H. Y. Lee and T. H. Cho, “Fuzzy-Based Adaptive Thre-
shold Determining Method for the Interleaved Authenti-
cation in Sensor Networks, ” ICDCIT 2006, Lecture Notes
in Computer Science, Vol. 4319, 2006, pp. 116-127.
doi:10.1007/11925231_11
[12] Louder than a Bomb Software, “Free Fuzzy Logic Li-
brary,” 2001, http://ffll.sourceforge.net
[13] L. A. Zadeh, “Fuzzy Logic,” 2011,
http://en.wikipedia.org/wiki/Fuzzy_logic