Open Access Library Journal
Vol.03 No.10(2016), Article ID:71402,16 pages
10.4236/oalib.1103033
Tightly-Secure Authenticated Key Exchange without NAXOS’ Approach Based on Decision Linear Problem
Mojahed Mohamed1,2, Xiaofen Wang1, Xiaosong Zhang1
1School of Computer Science and Engineering, University of Electronic Science and Technology of China, Chengdu, China
2Department of Electronic Engineering, Karary University, Omdurman, Sudan

Copyright © 2016 by authors and Open Access Library Inc.
This work is licensed under the Creative Commons Attribution International License (CC BY 4.0).
http://creativecommons.org/licenses/by/4.0/



Received: September 4, 2016; Accepted: October 6, 2016; Published: October 11, 2016
ABSTRACT
Design Secure Authenticated Key Exchange (AKE) protocol without NAXOS approach is remaining as an open problem. NAXOS approach [4] is used to hide the ephemeral secret key from an adversary even if the adversary in somehow may obtain the ephemeral secret key. Using NAXOS approach will cause two main drawbacks: (i) leaking of the static secret key which will be utilized in computing the exponent of the ephemeral public key; (ii) maximization of using random oracle when applying to the exponent of the ephemeral public key and session key derivation. In this paper, we present another AKE-secure without NAXOS approach based on decision linear assumption in the random oracle model. We fasten our security using games sequences tool which gives tight security for our protocol.
Subject Areas:
Information and Communication: Security, Privacy and Trust
Keywords:
AKE, eCK Model, NAXOS’ Approach, Decision Linear Assumption

1. Introduction
An Authenticated Key Exchange protocol (AKE) allows two parties to end up with a shared secret key in secure and authenticated manner. The authentication problem deals with restraining adversary that actively controls the communication links used by legitimated parties. They may modify and delete messages in transit, and even inject false one or may control the delays of messages.
In 1993, Bellare and Rogaway [1] provided the first formal treatment of entity authentication and authenticated key distribution appropriate to the distributed environment. In 1998, Bellare, Canetti, Mihir and Krawczyk [2] provided a model for studying session-oriented security protocols. They also introduce the “authenticator” techniques that allow for greatly simplifying the analysis of protocols. Also, they proposed a definition of security of KE protocols rooted in the simulatability approach used to define the security of multiparty computation. In 2002 Canetti and Krawczyk [3] presented their security model which had extended by LaMacchia, Lauter, and Mityagin [4] design and proposed NAXOS protocol which is secure under their model. That model capture attacks resulting from leakage of ephemeral and long-term secret keys, defined by an experiment in which the adversary is given many corruption power for various key exchange sessions and most solve a challenge on a test session. This model doesn’t give an adversary capability to trivially break an AKE protocol.
To acquire eCK security, NAXOS needs that the ephemeral public key X be computed from an exponent result from hashing an ephemeral private key x and the static private key a, more precisely  instead of
instead of . In this paper generating ephemeral public key as
. In this paper generating ephemeral public key as  is called NAXOS’s approach. In NAXOS’s approach no one is capable of querying the discrete logarithm of an ephemeral public key X without the pair (
is called NAXOS’s approach. In NAXOS’s approach no one is capable of querying the discrete logarithm of an ephemeral public key X without the pair ( ); thus, the discrete logarithm of X is hidden via an additional random oracle. Using NAXOS' approach many protocols, [5] - [8] were claimed secure in the eCK model under the random oracle assumption. In the standard model, eCK-secure protocols were declared to be secured in the eCK model as Okamoto [9] ; they use pseudo-random functions instead of hash functions.
); thus, the discrete logarithm of X is hidden via an additional random oracle. Using NAXOS' approach many protocols, [5] - [8] were claimed secure in the eCK model under the random oracle assumption. In the standard model, eCK-secure protocols were declared to be secured in the eCK model as Okamoto [9] ; they use pseudo-random functions instead of hash functions.
Motivating Problem. (1) Design AKE-secure protocol without NAXOS trick to achieve two goals: (i) To reduce the risk of leaking the static private key, since the derivation of the ephemeral public key is independent of the static private key. This method is in contrast to protocols that use the NAXOS' approach. (ii) Minimize the utilization of the random oracle, by applying it only to the session key derivation. Kim, Minkyu, Atsushi Fujioka, and Berkant Ustaolu [10] proposed a two strongly secure authenticated key exchange protocols without NAXOS approach, one of their protocol supposed to be secure under the GDH assumption and the other under the CDH assumption in random oracle model. Mohamed et al. [19] designed a protocol without NAXOS approach but secure in RO model, they rely the security of their protocol upon security reduction, and we use in this paper the game sequences tools to fasten the security and give tightly secure security proof. (2) Design AKE-secure protocol secure under Decision Linear Assumption. Boneh, Boyen, and Shacham [11] introduced a decisional assumption, called Linear, intended to take the place of DDH in groups―in particular, bilinear groups [12] ―where DDH is easy. For this setting, the Linear problem has desirable properties, as Boneh, Boyen and Shacham show: it is hard if DDH is hard, but, at least in general groups [13] , remains hard even if DDH is easy.
Contributions. We present a concrete and practical AKE protocol that is eCK secure under Decisional Linear assumption in the random oracle model. Our protocol does not rely on any NAXOS trick that yields a more efficient solution when it is implement- ed with secure device. We give tight proof reducing eCK security of our protocol to break the used cryptographic primitives under random oracle. In our protocol, the ephemeral public key is containing each peers generator, which results in two different discrete logarithm problems with two different generators, which increase hardness for DL’s solver.
In the derivation of the session key, each party will compete shared secret from ephemeral keys and static keys. We fasten the security of this protocol using games sequences tool which gives tight security.
Organization. Section 2 reviews security definitions and states the hard problem. Section 3 gives brief for the eCK model. Section 4 proposes AKE-secure protocol with its security results. Section 5 compares our protocol with other related AKE protocols and shows its efficiency. And finally, we draw the conclusion in Section 6.
2. Preliminaries
In this section, we review security definitions we will use to construct our protocol.
2.1. The Decision Linear Diffie-Hellman Assumption
Let G be a cyclic group of prime order p and along with arbitrary generators  and h where
and h where
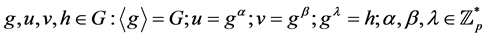 (1)
(1)
consider the following problem:
Decision Linear Problem in G [11] Given 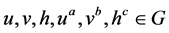 as input, output yes if
as input, output yes if  and no otherwise.
and no otherwise.
One can easily show that an algorithm for solving Decision Linear in G gives an algorithm for solving DDH in G. The converse is believed to be false. That is, it is believed that Decision Linear is a hard problem even in bilinear groups where DDH is easy. More precisely, we define the advantage of an algorithm  in deciding the Decision Linear problem in G as
in deciding the Decision Linear problem in G as
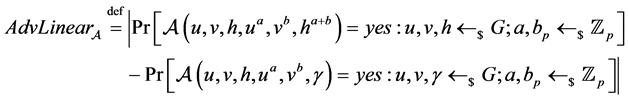 (2)
(2)
The probability is over the uniform random choice of the parameters to , and over the coin tosses of
, and over the coin tosses of . We say that an algorithm
. We say that an algorithm  -decides Decision Linear in G if
-decides Decision Linear in G if  runs in time at most t, and
runs in time at most t, and 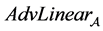 is at least
is at least .
.
Definition 2.1. We say that the  -Decision Linear Assumption (DLIN) holds in G if no t-time algorithm has advantage at least
-Decision Linear Assumption (DLIN) holds in G if no t-time algorithm has advantage at least  in solving the Decision Linear problem in G.
in solving the Decision Linear problem in G.
2.2. Linear Diffie-Hellman
Let 










or in input 

3. Security Model
In this section, eCK model is outlined [18] . An n different parties 






Sessions: A party is activated by an outside call or an incoming message to execute the protocol
























Adversaries: The adversary 


Establish Party (






Send (




Ephemeral Key Reveal (sid): 
Static Key Reveal (



Session Key Reveal (sid): 

Experiment 






Definition 3.1 (Fresh session). Let sid be a complete session, owned by honest 


1. 


2. If 

(a) Both Static Key Reveal (
(b) Both Static Key Reveal (

3. If 

(a) Both Static Key Reveal (
(b) Static Key Reveal (
The eCK security notion can be described now.
Definition 3.2 (eCK security). The advantage of the adversary 



The protocol 
1) If two honest parties complete matching sessions, then they will both compute the same session key, except with a negligible probability.
2) The advantage 
4. Protocol
Parameters. Let k be the security parameter and G be a cyclic group with generator g and order a k-bit prime p. Let user’s public key is a triple of generators








4.1. Protocol Description
As following description, 

1) 




2) Upon receiving










3) Upon receiving








Both parties compute the shared secret


Figure 1. Tightly-Secure Authenticated Key Exchange without NAXOS’ approach based on Decision Linear Problem.
4.2. Protocol Security
Theorem 4.1. If the DLIN assumption holds in G and H is a random oracle, then the Protocol 
Let 





is the peer. Let 





this proof. Let 

-case 1: Existence of a matching session 

-case 2: No existence of a matching session for the target session
Case 1. To analyze this event, Adversary 


-
Claim. let 



Proof. It’s easy to derive the proof from definition 3.2
-




Claim. let 




Proof. In this game, it obvious that this game is similar to game 





In another hand, the adversary should success in guessing target session and its matching session. Let 
thus
From these two probabilities, we can derive the whole probability that adversary success in guessing parties 

-



where
Claim. let 



Proof. We transform game 


where




-


Claim. let 



which 

Proof. We will prove here using the same idea in the previous game. In this game we transformed from 


Moreover, as h act as a one-time pad in game

Combining (8), (9), (10), (11) and (12), we obtain

Case 2. To analyze this event, Adversary 


-

Claim. let 



Proof. That proof can be derived from
-




Claim. let 



Proof. In this game, it is obvious that this game is similar to game 





In another hand, the adversary should success in guessing target session and its matching session. Let Pr[sidA;B], denote the probability that adversary successfully guess the target session from 
From these two probabilities, we can derive the whole probability that adversary success in guessing parties and with target session and its matching session with the form:
-





Claim. let 



Proof. We transform game 













There for, we obtain:
-




Claim. let 





which 

Proof. We will prove here using the same idea in the previous game. In this game we transformed from 

The difference between 

Moreover, as h act as a one-time pad in game

Combining (14), (15), (16), (17) and (18), we obtain

From the sequence of preceding claims, we can conclude that since the 

5. Efficiency
In this section, we compare our protocols with other related AKE protocols in terms of based assumption, computational efficiency and security model. In Table 1 number of exponentiation in G (E), a number of static public keys (SPK) and the number of ephemeral public key (EPK). Table 5 presents the naive group exponentiations count; Okamoto’s protocol is secure in the standard model, but the proof relies on an existence of pPRF family. In the security proof of HMQV and CMQV, the reduction argument is less tight since the Forking Lemma [14] is essential for the arguments. Our protocol in Table 1, has tighter security reductions and does not use the Forking Lemma and just uses one static public key in computation.
It clear that our protocol has same security model with NETS, CMQV, and KFU-P1, but it differs from them in base assumption and computation.
Table 1. Protocols comparison.
We showed that it is possible to construct eCK-secure AKE protocols without using NAXOS’ approach, so our protocol is secure even when the discrete logarithm of the ephemeral public key is revealed and decrease the risk of leaking the static private key which makes our protocol more practical.
Moreover, One of the advantages of our protocols is the use of single random oracle as opposed to two for HMQV and CMQV. The random oracle is merely needed for the session key derivation, which is typical way to attain indistinguishability in random oracle model.
Also, our protocol uses decision linear assumption with a tight security proof.
6. Conclusion
In this paper, we present AKE protocol secure in the eCK model under Decision Linear assumption(DLIN) without using NAXOS trick with a fastened reduction, which reduces the risk of leaking the static private key, that because of the derivation of the ephemeral public key is independent of the static private key. This is in contrast to protocols that use the NAXOS’ approach, and minimize the use of the random oracle, by applying it only to the session key derivation. We gave tightly security proof for our protocol based on games. In this paper, how to preserve the security of to this protocol without using random oracle remains as an open problem.
Cite this paper
Mohamed, M., Wang, X.F. and Zhang, X.S. (2016) Tightly- Secure Authenticated Key Exchange without NAXOS’ Approach Based on Decision Linear Problem. Open Access Library Journal, 3: e3033. http://dx.doi.org/10.4236/oalib.1103033
References
- 1. Bellare, M. and Rogaway, P. (1993) Entity Authentication and Key Distribution. Crypto 1993, LNCS 773, 110-125.
- 2. Bellare, M., Canetti, R. and Krawczyk, H. (1998) A Modular Approach to the Design and Analysis of Authentication and Key Exchange Protocols. Proceedings of the 30th Annual ACM Symposium on Theory of Computing, ACM, Location, pp.
- 3. Canetti, R. and Krawczyk, H. (2001) Analysis of Key-Exchange Protocols and Their Use for Building Secure Channels. Eurocrypt 2001, LNCS 2045, 453-474.
- 4. LaMacchia, B., Lauter, K. and Mityagin, A. (2007) Stronger Security of Authenticated Key Exchange. ProvSec 2007, LNCS 4784, 1-16.
- 5. Ustaoglu, B. (2008) Obtaining a Secure and Efficient Key Agreement Protocol for (H)MQV and NAXOS. Designs, Codes and Cryptography, 46, 329-342. Extended version available at http://eprint.iacr.org/2007/123
- 6. Huang, H. and Cao, Z. (2008) Strongly Secure Authenticated Key Exchange Protocol Based on Computational Diffie-Hellman Problem. Inscrypt.
- 7. Lee, J. and Park, J. (2008) Authenticated Key Exchange Secure under the Computational Diffie-Hellman Assumption.
http://eprint.iacr.org/2008/344 - 8. Lee, J. and Park, C. (2008) An Efficient Key Exchange Protocol with a Tight Security Reduction.
http://eprint.iacr.org/2008/345 - 9. Okamoto, T. (2007) Authenticated Key Exchange and Key Encapsulation in the Standard Model. Asiacrypt 2007, LNCS 4833, 474-484.
- 10. Kim, M., Fujioka, A. and Ustaoglu, B. (2009) Strongly Secure Authenticated Key Exchange without NAXOS’s Approach. In: Advances in Information and Computer Security, Springer Berlin Heidel-berg, 174-191.
- 11. Boneh, D., Boyen, X. and Shacham, H. (2004) Short Group Signatures. In: Franklin, M., Ed., Proceedings of Crypto 2004, Volume 3152 of LNCS, Springer-Verlag, , 41-55.
http://dx.doi.org/10.1007/978-3-540-28628-8_3 - 12. Joux, A. and Nguyen, K. (2003) Sepa-rating Decision Diffie-Hellman from Computational Diffie-Hellman in Cryptographic Groups. Journal of Cryptology, 16, 239-247.
http://dx.doi.org/10.1007/s00145-003-0052-4 - 13. Shoup, V. (1997) Lower Bounds for Discrete Logarithms and Related Problems. In: Fumy, W., Ed., Proceedings of Eurocrypt 1997, Volume 1233 of LNCS, Springer-Verlag, 256-266.
- 14. Pointcheval, D. and Stern, J. (2000) Security Arguments for Digital Signatures and Blind Signatures. Journal of Cryptology, 13, 361-396.
http://dx.doi.org/10.1007/s001450010003 - 15. Krawczyk, H. (2005) HMQV: A High-Performance Secure Diffie-Hellman Protocol. Crypto 2005, LNCS 3621, 546-566.
- 16. Ustaoglu, B. (2008) Obtaining a Secure and Efficient Key Agreement Protocol for (H)MQV and NAXOS. Designs, Codes and Cryptography, 46, 329-342.
http://dx.doi.org/10.1007/s10623-007-9159-1 - 17. Wu, J. and Ustaoglu, B. (2009) Efficient Key Exchange with Tight Security Reduction. IACR Cryptology ePrint Archive, 2009, 288.
- 18. Li, H. and Wu, C.K. (2012) CMQV+: An Authenticated Key Exchange Protocol from CMQV. Science China Information Sciences, 55, 1666-1674.
http://dx.doi.org/10.1007/s11432-011-4310-z - 19. Mohamed, M., Wang, X.F. and Zhang, X.S. (2015) Efficient Secure Authenticated Key Exchange without NAXOS’s Approach Based on Decision Linear Problem. Collaborative Computing: Networking, Applications, and Worksharing. Springer International Publishing, 243-256.
Appendix
A.1
A.2
A.3
A.4
A.5
A.6
A.7
A.8
Submit or recommend next manuscript to OALib Journal and we will provide best service for you:
Publication frequency: Monthly
9 subject areas of science, technology and medicine
Fair and rigorous peer-review system
Fast publication process
Article promotion in various social networking sites (LinkedIn, Facebook, Twitter, etc.)
Maximum dissemination of your research work
Submit Your Paper Online: Click Here to Submit
Or Contact service@oalib.com



































