Int'l J. of Communications, Network and System Sciences
Vol.2 No.2(2009), Article ID:425,8 pages DOI:10.4236/ijcns.2009.22014
Energy Aware Clustered Based Multipath Routing inMobile Ad Hoc Networks
1Dept. of Computer Science and Engineering J.N.T University, Hyderabad, India
2Dept. of Computer Science and Engineering, S.V.U College of Engineering, Tirupati, India
3Dept. of Electronics and Communication Engineering, J.N.T University, Hyderabad, India
Email: saibheem2008@gmail.com, mmnaidu@yahoo.com, dsraoece@yahoo.co.uk
Received January 10, 2009; revised February 21, 2009; accepted February 23, 2009
Keywords: Clustering, CONID, MANET, Mutlipath, AODVM
Abstract
With the advance of wireless communication technologies, small-size and high-performance computing and communication devices are increasingly used in daily life. After the success of second generation mobile system, more interest was started in wireless communications. A Mobile Ad hoc Network (MANET) is a wireless network without any fixed infrastructure or centralized control; it contains mobile nodes that are connected dynamically in an arbitrary manner. The Mobile Ad hoc Networks are essentially suitable when infrastructure is not present or difficult or costly to setup or when network setup is to be done quickly within a short period, they are very attractive for tactical communication in the military and rescue missions. They are also expected to play an important role in the civilian for as convention centers, conferences, and electronic classrooms. The clustering is an important research area in mobile ad hoc networks because it improves the performance of flexibility and scalability when network size is huge with high mobility. All mobile nodes operate on battery power; hence, the power consumption becomes an important issue in Mobile Ad hoc Network. In this article we proposed an Energy Aware Clustered-Based Multipath Routing (EACMR), which forms several clusters, finds energy aware node-disjoint multiple routes from a source to destination and increases the network life time by using optimal routes.
1. Introduction
The history of wireless networks started in the 1970s and the interest has been growing ever since. Based on infrastructure, the wireless networks broadly classified into two types, first type infrastructure networks contains base-stations; an example of this wireless network is the cellular-phone network where a phone connects to the base-station with the best signal quality. When the phone moves out of range of a base-station, it does a “hand-off” and switches to a new base-station within reach, the second type is called as Mobile Ad hoc Network without any fixed infrastructure or centralized control; it contains mobile nodes that are connected in an arbitrary manner. It enables the users to communicate without any physical infrastructure regardless of their geographical location. All nodes in the Mobile Ad hoc Network (MANET) are mobile and can be connected dynamically in an arbitrary manner. Each node behaves as a router, takes part in discovery and maintains the routes to other nodes. The nodes are the main components of the network; these nodes can move freely at any time and can leave or join the network so the network structure changes dynamically due to mobility [1].
1.1. Clustering and Multipath Routing
In a clustering scheme the mobile nodes in a MANET are divided into different virtual groups based on certain rules. The mobile nodes may be assigned a different status such as clusterhead, clustergateway or clustermember. A clusterhead normally serves as a local coordinator for its cluster, performing intra-cluster transmission arrangement, data forwarding, and so on. A clustergateway is a non-clusterhead node with inter-cluster links, so it can access neighboring clusters and forward information between clusters. A clustermember is usually called an ordinary node [2].
A fundamental problem in the MANET is how to deliver data packets among nodes efficiently without predetermined topology or centralized control, which is the main objective of ad hoc routing protocols. Because of the dynamic nature of the network, ad hoc routing faces many unique problems not present in wired networks. Particularly in MANETs where routes become obsolete frequently because of mobility and poor wireless link quality. The Multipath routing addresses these problems by providing more than one route to a destination node. Multipath routing appears to be a promising technique for ad hoc routing protocols, the multiple paths can be useful in improving the effective bandwidth of communication, responding to congestion and heavy traffic, increasing delivery reliability and security. The traffic can be distributed among multiple routes to enhance transmission reliability, provide load balancing, and secure data transmission [3].
Most existing routing protocols for MANET build and utilize only one single route for each pair of source and destination nodes. Due to node mobility, node failures, and the dynamic characteristics of the radio channel, links in a route may become temporarily unavailable and making the route invalid. The overhead of finding alternative routes may be high and extra delay in packet delivery may be introduced. Multipath routing addresses this problem by providing more than one route to a destination node. Source and intermediate nodes can use these routes as primary and backup routes. Alternatively, source node can distribute traffic among multiple routes to enhance transmission reliability, provide load balancing, and secure data transmission.
2. Related Work
This work falls under three areas in the MANET: clustering algorithms, multipath routing protocols and energy aware routing protocols, this section reviews these areas focusing on their relationship to the proposed protocol.
Jane Y. et al. [2] surveyed the different clustering mechanisms and described the advantages and disadvantages of each clustering scheme. The clustering schemes broadly classified into six categories Dominating Set based clustering schemes, Low maintenance clustering schemes, Mobility aware clustering schemes, Energy efficient clustering schemes, Load balancing clustering schemes and Combined-metrics based clustering schemes. The Energy efficient clustering avoids unnecessary energy consumption or balancing energy consumption for mobile nodes in order to prolong the lifetime of mobile nodes and the network.
The on-demand routing is the most popular approach in the MANET. Instead of periodically exchanging route messages to maintain a permanent route table of the full topology, the on-demand routing protocols build routes only when a node needs to send the data packets to a destination. The standard protocols of this type are Dynamic Source Routing (DSR) [4] and the Ad hoc Ondemand Distance Vector (AODV) routing [5]. However, these protocols do not support multipath.
The several multipath on-demand routing protocols were proposed, some of the standard protocols are, the Ad hoc On-demand Multipath Distance Vector (AOMDV) [6] is an extension to the AODV protocol for computing multiple loop-free and link-disjoint paths. The Split Multipath Routing (SMR) [7] is an on-demand Multipath source routing protocol can find an alternative route that is maximally disjoint from the source to the destination. The Multipath Source Routing (MSR) [8] is an extension of the DSR protocol to distribute traffic among multiple routes in a network. The Ad hoc Ondemand Distance Vector Multipath Routing (AODVM) [9] is an extension to the AODV for finding multiple node disjoint paths. These protocols build multiple routes based on demand but they did not consider energy.
Several energy aware multipath on-demand routing protocols have been proposed [10-14], but these protocols are not based on clustering. The Cluster Based Multipath Dynamic Source Routing CMDSR) [15] was designed to be adaptive according to network dynamics. It uses the hierarchy to perform route discovery and distributes traffic among diverse multiple paths, but it does not consider energy in the route selection.
The Grid-Based Energy Aware Node-Disjoint Multipath Routing Algorithm (GEANDMRA) [16] considers energy aware and node-disjoint multipath, it uses grid head election algorithm to select the grid-head which is responsible for forwarding routing information and transmitting data packets. The routing is performed in a grid-by-grid manner, the network area is partitioned into non-overlapping square zones with the same size, each zone is named with a unique ID(x,y) as the conventional coordinate. At any time each node can obtain its location information from Global Position System (GPS) to know in which zone it is located. But the disadvantages of GPS are as follows [17].
•There are several factors that introduce error to GPS position calculations. A major source of error arises from the fact that radio signal speed is constant only in a vacuum. it means that distance measurements may vary as the values of the signal speed vary in the atmosphere. Water vapor and other particles in the atmosphere can slow signals down, resulting in propagation delay.
•Another source of errors due to multipathfading, which occurs when a signal bounces off a building or terrain before reaching the receiver’s antenna, also can reduce accuracy.
•Another factor affecting the precision is satellite geometry.
•The largest source of potential error is selective availability, an intentional degradation of L1, the civilian GPS signal. SA was originally intended to prevent a hostile force or terrorist group from exploiting the technology.
•An location fix can only be identified if a ‘fix’ from at least 3 satellites are available.
•In addition, distance measurements are less reliable when the receiver of satellite locks on to or closely oriented with respect to each other. Atomic clock discrepancies, receiver noise, and interruptions to ephemeris monitoring can result in minor errors.
•GPS does not work effectively if the ‘line of sight’ between a device and the satellites is obscured. Not only does this render GPS ineffective indoors but also if any material gets in the way of this ‘line of sight’. It is fair to assume therefore that a worker in a vehicle or in a station or operating in a dense urban area with tall buildings may struggle to get a location fix from GPS.
•The device needs a dedicated GPS antenna, chipset and software, so there is a additional cost for this hardware and software.
•Power consumption in the device is significant for using GPS.
We proposed novel approach without using GPS; this approach is very suitable and applicable for the cluster based mobile ad hoc networks.
3. Energy Aware Clustered-Based Multi-path Routing (EACMR)
The HELLO messages are already in usage in on demand routing, each node maintains only the status of its neighbors. Periodically, each node broadcasts a hello message to all its neighbors to indicate its active status. Each node receives the hello messages from its neighbors and updates its neighbor information table. In the EACMR, the clusters are formed by using hello messages, this result in less overhead. The EACMR finds node-disjoint multiple routes from a source to destination and increases the network life time by using optimal routes.
3.1. Network Model
A MANET is represented by undirected graph, G=(V,E) where V is the set of nodes and E is the set of bidirectional links. It is assumed that, at any time, nodes are situated randomly throughout the network area in accordance with a two-dimensional uniform random variable distribution. Each node is equipped with a single network interface card (NIC) and has a transmission radius of r. Each node has mobility, the speed is uniformly chosen between the minimum and maximum speeds. When the node reaches to its destination, it stays there for a certain pause time, after which it chooses another random destination point and repeats the process, the mobility is defined as the distance moved per unit time by a node in the network. Suppose at time t1 the node ni is at (x1, y1) and by time t2 the node ni has moved to (x2, y2), then the mobility of the node ni denoted by

All mobile node relay on battery, the energy consumption varies from 240mA at receiving mode and 280mA in the transmitting mode using 0.5V energy. Thus,when calculating the energy consumed to transmit a packet p is Etx(p)=I×V×tp. Joules are needed [18], here, I is the current, V is the voltage and tp is the time taken to transmit the packet p.
The energy required to transmit a packet p is given by Etx(p)=280mA×V×tp .The energy is required to receive a packet p is given by Erx(p)=240mA×V×tp. The energy consumption of overhearing the data transmission may be assumed as equivalent to energy consumption of receiving of the packet. When a packet is transmitted by ni at time t then it updates its residual battery capacity by using the following formula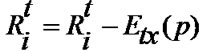 .when packet is received by ni at time t then it updates its residual battery capacity by using the following formula
.when packet is received by ni at time t then it updates its residual battery capacity by using the following formula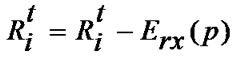 .
.
3.2. Cluster Formation and Maintenance
The Combined Higher Connectivity Lower ID (CONID) clustering algorithm [19] is used generates the clusters in the network. It is an extension of the lowest ID algorithm; the lowest ID algorithm does not take into account the connectivity (degree) of nodes, and therefore may produce more number of clusters than necessary. The pure connectivity based clustering algorithm modified version the lowest ID algorithm, in which ID is replaced by node degree, but it does not work properly because of numerous ties between nodes. The CONID uses node degree as the primary key and ID as the secondary key in cluster decisions. It is generalized the connectivity to count all k-hop neighbors of the given node. For k=1, the connectivity is equivalent to node degree, whenever the connectivities are the same, IDs are compared to make the decision.The clustering algorithm, refereed to as the k-CONID (k-hop connectivity ID) algorithm, works as follows. Each node is assigned with clusterhead priority. A pair is denoted by did=(d,ID), where d is its connectivity and ID is its IP address.
Let did’= (d’, ID’) and did”= (d”, ID”). Then did’>did’ if d’> d” or d’=d” and ID’ < ID”. That is, a node has clusterhead priority over the other node if it has higher connectivity or in case of equal connectivity and has lower ID. The cluster formation and cluster maintenance are clearly explained in [19], after applying clustering algorithm the network is shown Figure 1. After running CONID, each clusterhead finds its all neighbor clusterheads, for example, clusterheads 18 and 10 are the neighbor clusterheads of clusterhead 2 in Figure 1.
3.3. Route Selection
The route selection is based on cost function; the main objective is to give more weight (or) cost to node with less energy to prolong its life time. Let Rit be the battery capacity of a node ni at time t. Let fi(Rit) be the cost function of node ni, it is also considered as node’s cost or weight of node ni at time t, the cost of node ni at time t is inversely propositional to its residual energy i.e. fi(Rit))= 1/Rit). As the battery capacity decreases, the value of cost for node ni will increase. The main objective of route selection is to select an optimal path based on costs of clusterheads, because clusterhead normally serves as a local coordinator for its cluster, performing intra-cluster transmission arrangement, data forwarding. So clusterhead is important node within cluster and spends its energy for other nodes.
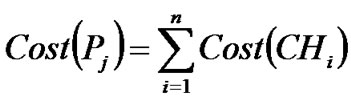
We define the following cost function to a clusterhead. Let Ci be ith cluster whose clusterhead at time t is denoted by CHi. The Cost of CHi at time t as follows
where
ρi: Transmit power of CHi
Fi: Full-charge capacity of CHi
Rit: Remaining battery capacity of CHi at time t.
wi: weight factor of CHi, which depends upon various factors, like battery’s quality, battery’s capacity, life time, battery’s back up, price.
N(Ci):the size of cluster Ci, it is the total number of all the nodes(clustermembers, gateways and clusterhead) in Ci, it is directly proportional to the cost of the node.
Let Pj be the path from source node S to destination node D via clusterheads CH1, CH2,CH3 …………..CHn at time t, it is denoted by
On the above path, in between two clusterheads, either gateway or clustermember (non-clusterhead nodes) may exist, however they are not consider in the evaluation of

Figure 1. Network with clusters.
cost of the path. Because main intension is to consider the total cost of path through clusterheads only, we define the cost of path Pj at time t via clusterheads is the sum of the costs of all the clusterheads on Pj, it is denoted by
3.3.1 Optimal Path Selection
Let k be number of node disjoint paths from source S to destination D, an optimal path is a path whose cost is least among k paths.
The optimal path is also called primary path. Initially it is used for data transmission, if it fails, then the secondary path (whose cost is least among k-1 paths) is used for data transmission. For example in figure 2,there are three node disjoint paths from source S to destination D via clusterheads; the paths are 1-2-3-4-5, 1-7-6-5 and 1-8-9-10-5.
If source node S belongs to ith cluster whose clusterhead is CHi then it is called as source clusterhead. Similarly, If destination D belongs to jth cluster whose clusterhead is CHj then it is called as destination clusterhead in Figure 2. Clusterhead 1 is called as source clusterhead and clusterhead 5 is called as destination clusterhead. If

Figure 2. Node-disjoint paths through Clusterheads.
two clusterheads are neighbors then they are called as 1-hop neighbor clusterheads.In Figure 2, the clusterheads 3, 7, 8 are neighbors of the clusterhead 1.
3.4. Route Discovery
The route selection is based on the route discovery. In order to facilitate the computation of multiple node disjoint paths from the source to destination, We choose the Ad hoc On-Demand Distance Vector Multipath (AODVM) [9] protocol as a candidate protocol and make modifications to it to enable the discovery of node disjoint paths via clusterheads. The AODVM is the extension of AODV [6] to provide multiple nodes disjoint paths.
3.4.1. The Proposed Modifications
The proposed modifications are explained briefly as follows. Only clusterheads maintain routing tables and run this protocol to find nod-disjoint paths. The other nodes (Gatewaynodes and Clustermembers) don’t maintain the routing tables, simply they forward the packets according to specified path.
3.4.2. Modification of Control Packets
The RREQ packet of AODVM is same as RREQ packet of EACMR. The RREP packet of AODVM is extended as RREP packet of EACMR by adding with Cost field, this field carries cumulative costs of clusterheads through which it passes. The initial value of this field is zero.
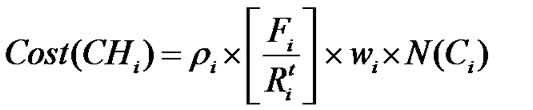
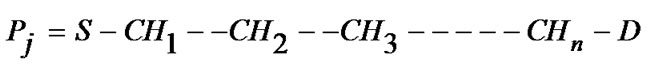
3.4.3. Modification of Tables
In the AODVM, each node maintains two tables, the routing table is used to forward the data packets from source to destination where as the RREQ table is used to form the route from source to destination, the fields of both tables are shown in Figure 3 and Figure 4.
In the EACMR, the routing table is extended to include the cost field. But RREQ table is same. These two tables are maintained by clusterheads only.
3.4.4. The Proposed Modifications in Node Functioning
In the AODVM, when the source node wants to send packets to a destination, it looks up its route cache to determine if it already contains a route to the destination. If it finds that an unexpired route to the destination exists, then it uses this route to send the packet. But if the node

Figure 3. Fields of routing table.
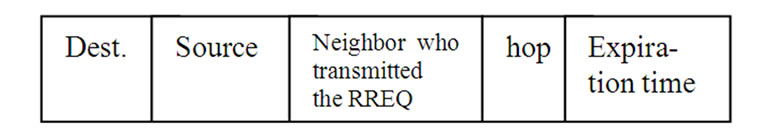
Figure 4. Fields of RREQ table.
does not have such a route, then it initiates the route discovery process by broadcasting a RREQ packet.
It is modified that when the source node wants to send packets to a destination, it sends the RREQ to its clusterhead; clusterhead looks up its route cache (routing table) to determine if it already contains a route to the destination. If it finds that an unexpired route exists to the destination, then it sends the reply to the source and uses this route to forward the packets from the source node, else then it initiates the route discovery process by forwarding a RREQ packet to its all neighbor clusterheads.
In the EACMR, the propagation of RREQ packet at intermediate clusterhead follows the same rules as at intermediate node in AODVM. When RREQ packet arrives at intermediate clusterhead, The RREQ is inspected and the following two cases it is dropped.
1) If this RREQ packet was already processed by the intermediate clusterhead or 2) If TTL value of the RREQ packet becomes zero.
Otherwise, the intermediate clusterhead broadcasts the RREQ to all its neighbor clusterheads by recoding the information about the clusterhead through which RREQ was received and corresponding hop-count back to the source clusterhead into its RREQ table, in this way the RREQ is forwarded by a intermediate clusterheads. Finally several RREQs will reach to destination clusterhead through different paths from the source clusterhead.
When a RREQ packet is received to a destination clusterhead, it generates a RREP packet and sent back to its neighbor clusterhead (last hop) from which the RREQ packet has been received. When an intermediate clustehead receives the RREP packet, it checks its RREQ table to find its neighbor clusterhead (next hop in reverse path) through which shortest path back to the source clusterhead and sends the RREP packet to it by deleting corresponding entry in the RREQ table.
In order to ensure that a clusterhead does not participate in multiple paths, If it receives another RREP packet from different neighbor clusterhead, it is dropped (i.e., RREQ table is already empty), it generates a Route Discovery Error (RDER) packet and sends it back to the neighbor clusterhead through which another the RREP packet has been received. The neighbor clustered upon receiving the Route Discovery Error (RDER) packet will try to forward the RREP packet to another neighbor clusterhead through which shortest path back to the source clusterhead and sends the RREP packet to it by deleting corresponding entries in the RREQ table.
Finally several RREP packets will be received by the source clusterhead, this information is recorded into its cache based on arriving order and it sends the reply to the source .The path with minimum cost is selected as an optimal path for transmission of source’s data. If clusterhead wants to transmit the data, it follows above procedure to find node disjoint paths.
3.5. Route Maintenance
The EACMR handles route maintenance in a manner similar to the AODVM. Whenever a link breakage happens in a route due to a node moving away, the previous hop node of the moved away node is responsible for sending a Route Error (RERR) message back to the source clusterhead to inform the breakage. It chooses alternative routes to maintain the connection. If there are no more redundant routes left, then it will start a new route discovery.
3.6. Congestion Control and Increasing Network Lifetime
When a congestion state occurs in a routing path, congested clusterhead sends choke packet to the source clusterhead, it distributes the incoming data packets to the other node-disjoint routing paths to avoid the congestion.
During the transmission of data packets, if battery energy of clusterhead is reached to threshold energy, then it selects a clustermember as new clusterhead whose energy is high among its clustermembers, then it sends information about cluster and it will act as clustermember.
4. Simulation
In this section, it describes the simulation, various chosen parameters for simulation and the various performance metrics. With reference to simulation model in [20], we have designed own simulator with the following modules.
Network Formation Module: This module is used to generate a random network, inputs of this module are simulation area (length x breadth), number of nodes, cell radius of each node, initial position of each node and initial energy of each node. The output of this module is a random network.
Node Mobility Module: This module sets the speed, direction and pause time of each node and allows each node to move in random direction. All the nodes in an ad hoc network are mobile. In this simulation, Random waypoint mobility model is used with pause time of each node is 10 sec and speed of each mobile node is 0 to 2m/sec.
Route Requests Event Generator Module: This module accepts the number of route requests from user, and then selects source and destination pairs randomly. Each route request follows the poison distribution process and each call duration time follows exponential distribution.
EACMR module: This is core module that incorporates several functions like Cluster formation, cluster maintenance, route discovery, route selection, route maintenance and congestion control.
Computation module: This module estimates various performance metrics like number of clusters, number of border nodes, the power consumption, residual energy, number of nodes expired (reached to threshold), overhead, throughput, end-to-end delay and other parameters.
Considering fifty nodes randomly distributed in an area of 1000m x 1000 m. It is assumed that the channel bandwidth is 2Mbps, a free space radio propagation model in which the signal power attenuates is 1/r2, where r is the distance between the nodes. Each node is equipped with a single network interface card and has a transmission radius of r=14m. The distributed coordination function of IEEE 802.11 is assumed at MAC layer.
All nodes operate in promiscuous mode, so it can overhear packets destined for others. It is assumed that the transmission power, receiving power are fixed for all the nodes and two nodes can hear each other if their distance is in the transmission range. The speeds are uniformly chosen between the minimum and maximum speeds and are set to 0m/s and 2m/s, respectively. When the node reaches its destination, it stays there for a certain pause time, after which it chooses another random destination point and repeats the process. The simulation ends after 100s. It is assumed that transmission ranges of all the nodes are equal. All nodes are assumed to have the same amount of battery capacity with full energy at the beginning of the simulation. Initial energy of each node is set to 100 Joules. The equal weight factor is chosen for all clusterheads. For the mobile scenarios, the random waypoint model is used to node mobility. In this model, a node chooses a random point in the network, and moves towards that point at a constant speed.
It is assumed that the number of route requests is denoted by λ and follows the poison process where as call holding time follows exponential distribution. When a route request occurs, two nodes are randomly selected as source and destination. The data traffic is generated by Constant Bit Rate (CBR) sessions initiated between the source and destination. Each clusterhead maintains threshold value (cut-off). The table 1 shows simulation parameters and their values.
During simulation, several performance parameters were estimated, like number of clusters (NC, number of border nodes, CH%, BP%, ASP, the total energy consumption at each clusterhead and total residual energy at each clusterhead. Along the number of clusterheads reached to the threshold, the results are shown in Table 2.
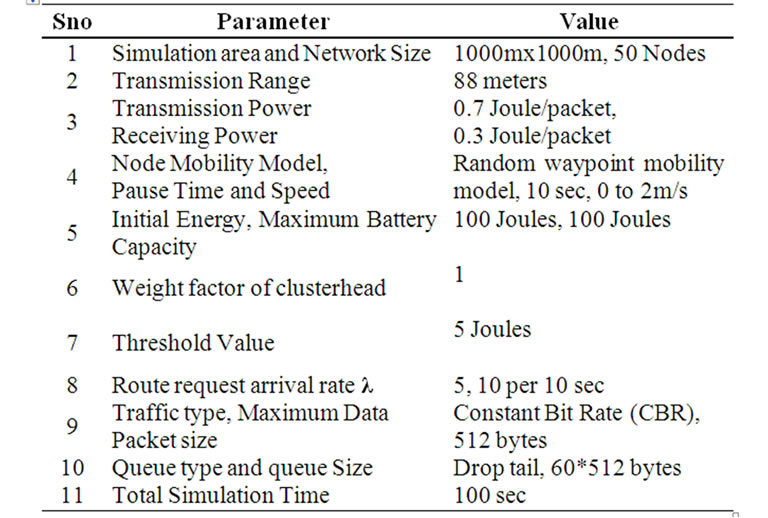
Table 1. Simulation parameters.
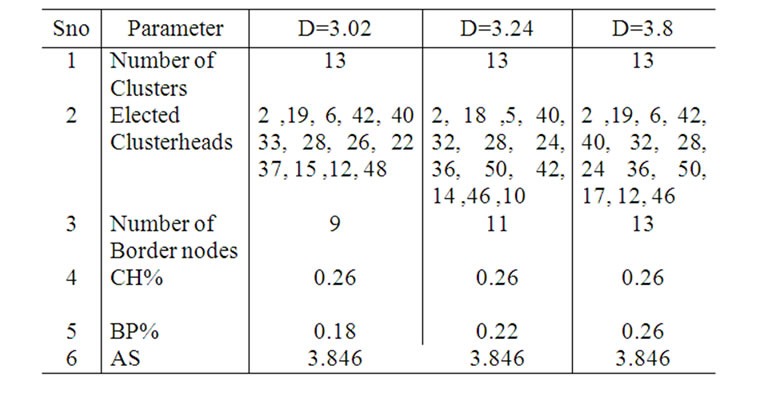
Table 2. Results.
The size and degree are denoted by N and D, respectively. CH% denotes the ratio of clusterhead nodes (that is, the number of clusters divided by the total number of nodes). Border nodes are nodes that belong to more than one cluster (that is, which are at distance at most k hops from at least two CHs), BP% denotes the ratio of border nodes, (that is, the number of border nodes divided by the total number of nodes). AS is the average size of a cluster (the average number of nodes in a cluster, that is, the number of nodes divided by the total number of clusters). Other results are shown in Figure 5 to Figure 7.
The total power consumption is directly proportional to various factors like network size, route requests arrival rate, packet arrival rate, packet size (header size and payload size), packet collision and retransmissions. Total residual energy is indirectly proportional to the power consumption. The network life depends on then node expiration which in turn depends upon energy consumption and threshold value. The node life time is indirectly proportional to the node’s energy consumption and it is also directly proportional to the threshold value of the energy of each node is denoted by γ. It is also called cut-off value; it is always greater than one. During the transmission of data, each node checks whether its energy
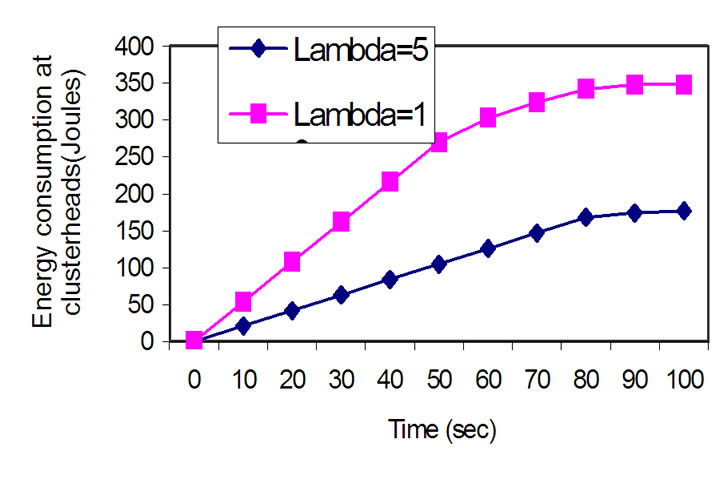
Figure 5. Energy consumption Vs time.
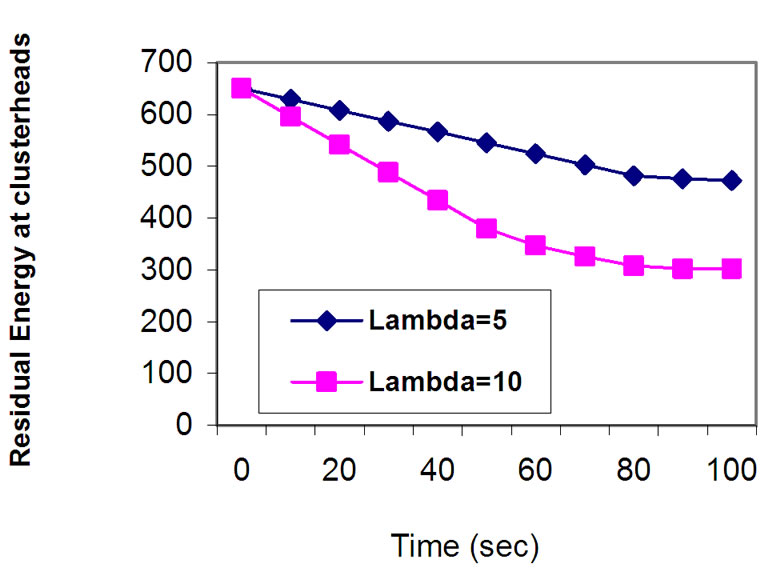
Figure 6. Residual energy Vs time.
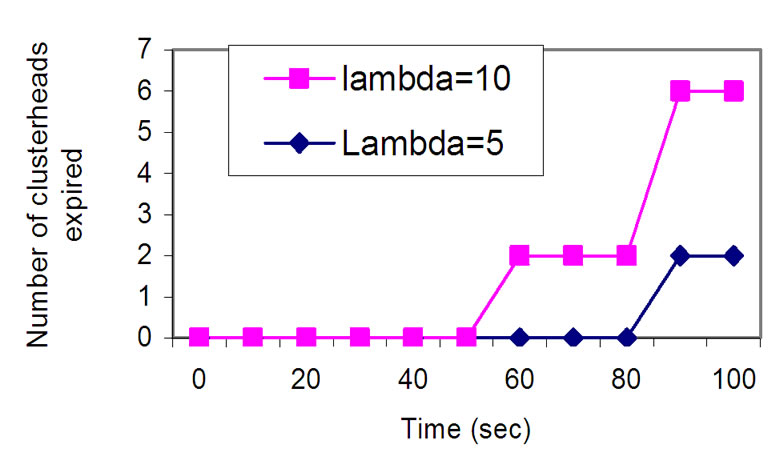
Figure 7. Number of CHs expired Vs time.
reaches to threshold or not. If its energy reaches to threshold then it will expire. The network lifetime can be defined in many ways:
•It may be defined as the time taken for K% of the nodes in a network to die
•It might be the time taken for the first node to die
•It can also be the time for all nodes in the network to die It can also be the time for all nodes in the network to die. To maximize the lifetime of network, each clustered maintains threshold.
Figure 5 depicts the variation of total energy consumption of clusterheads versus time; Figure 6 depicts the variation of total residual energy of clusterheads versus time. Figure 7 depicts number of clusterheads expired versus time.
5. Conclusions
Proposed novel approach (EACMR) is very suitable and applicable for the cluster based mobile ad hoc networks. It is not based on GPS. It can be applied to a mobile ad hoc network that is using any clustering scheme. In this work, the CONID clustering scheme is used as background to form clusters, instead of that any clustering scheme may be used to form clusters in the network.
The EACMR is designed to find energy aware nodedisjoint multiple routes from a source to a destination through clusterheads. It increases the network life time by using optimal routes, as compare to on demand multipath routing protocols, it significantly reduces the total number of route request packets using clustering technique, this result in an increased packet delivery ratio,decreasing end-to-end delays for the data packets, lower control overhead, fewer collisions of packets , decreasing power consumption. It supports the reliability by using multiple node-disjoint paths.
6. References
[1] C. S. R. Murthy and B. S. Manoj, “Ad hoc wireless networks: Architectures and protocols,” Prentice Hall, 2004.
[2] J. Y. Yu and P. H. J. Chong, “A survey of clustering schemes for mobile ad hoc networks,” in Proceedings of IEEE Communications Surveys, Vol. 7, pp. 32-48, 2005.
[3] Y. B. Liang, “Multipath ‘fresnel zone’ routing for wireless ad hoc networks,” Virginia Polytechnic Institute and State University, March, 2004.
[4] J. Broch, D. Johnson, and D. Maltz, “The dynamic source routing protocol for mobile ad hoc networks,” IETF Internet draft, 2004.
[5] E. P. Charles, E. M. Belding-Royer, and I. Chakeres, “Ad hoc on-demand distance vector routing,” IETF Internet draft, 2003.
[6] K. M. Mahesh and R. D. Samir, “On-demand multipath distance vector routing in ad hoc networks,” in Proceedings of IEEE International Conference on Network Protocols, pp. 14-23, 2001.
[7] S. J. Lee and M. Gerla, “Split multipath routing with maximally disjoint paths in ad hoc networks,” in Proceedings of IEEE ICC, pp. 3201-3205, 2001.
[8] L. Wang, Y. Shu, Z. Zhao, L. Zhang, and O. Yang, “Load balancing of multipath source routing in ad hoc networks,” in Proceedings of IEEE ICCC, Vol. 5, pp. 3197-3201, 2002.
[9] Z. Q. Ye, S. V. Krishnamurthy, and S. K. Tripathi, “A framework for reliable routing in mobile ad hoc networks,” in Proceedings of IEEE INFOCOM, Vol. 1, pp. 270-280, 2003.
[10] P. Yuan, Y. Bai, and H. Wang, “A multipath energyefficient routing protocol for ad hoc networks,” in Proceedings of International Conference on Communications, Circuits and Systems, Vol. 3, pp. 1462-1466, 2006.
[11] L. S. Tan, L. Xie, K. T. Ko, M. Lei, and M. Zukerman, “LAMOR: Lifetime-aware multipath optimized routing algorithm for video transmission over ad hoc networks,” in Proceedings of IEEE Vehicular Technology Conference, Vol. 2, pp. 623-627, 2006.
[12] S. Y. Jin, K. Kang, Y. J. Cho, and S. Y. Chae, “Power-aware multi-path routing protocol for wireless ad hoc network,” in Proceedings of IEEE Wireless Communications and Networking Conference, pp. 2247-2252, 2008.
[13] P. S. Anand, A. J. Anto, V. Janani, and P. Narayanasamy, “Multipath power sensitive routing protocol for mobile ad hoc networks,” in Proceedings of Wireless on Demand Network Systems, Springer, Vol. 2928, pp. 84-89, 2004.
[14] D. Y. Hwang, E. H. Kwon, and J. S. Lim, “An energy aware source routing with disjoint multipath selection for energy-efficient multihop wireless ad hoc networks,” in Proceedings of International Federation for Information Processing, pp. 41-50, 2006.
[15] H. Y. An, L. Zhong, X. C. Lu, and W. Peng, “A cluster-based multipath dynamic source routing in MANET,” in Proceedings of IEEE International Conference on Wireless and Mobile Computing, Networking and Communications, Vol. 3, pp. 369-376, August 2005.
[16] Z. Y. Wu, X. J. Dong, and L. Cui, “A grid-based energy aware node-disjoint multipath routing algorithm for MANETs,” in Proceedings of International Conference on Natural Computation, Vol. 5, pp. 244-248, 2007.
[17] R. Bajaj, S. Rannweer, and D. P. Agrawal, “GPS: Location-tracking technology,” IEEE computer, Vol. 35, pp. 92-94, April 2002.
[18] J. C. Cano and D. Kim, “Investigating performance of power-aware routing protocols for mobile ad hoc networks,” in Proceedings of International Mobility and Wireless Access Workshop, pp. 80, 2002.
[19] F. G. Nocetti, J. S. Gonzalez, and I. Stojmenovic, “Connectivity based k-hop clustering in wireless networks,” in Proceedings of Telecommunication Systems, Kluwer Academic Publishers, pp. 205-220, 2003.
[20] Simulation model for Maximum Battery Life Routing, http://sarwiki.informatik.hu-berlin.de.

