C.-M. Wu, ET AL. 105
The above two detection steps can achieve good per-
formance for most types of tampering. But, for collage
attack, additional detection steps below are required.
Setp 3. Inter-block restoration watermark section
comparison: As demonstrated in Figure 3, there are at
most six valid pairs of inter-block comparison. Assume N
denotes the number of valid inter-block comparison pairs.
The detection index in step 3 is:
2
3
2
1,= 0
=
,
ifmandthe numberof
minconsistentpairs ismore thanN
mothers
/2
1
3
(2)
Setp 4. Improvement based on block-neighborhood
tampering characteristics: In tampered region, the prob-
ability of false accept is high for large tamper ratio, espe-
cially. To reduce this undesired property, the tamper de-
tection index needs to be corrected by:
3=1
3
4
3
1,= 0= 3
=,
m
ifmand N
mmothers
(3)
Setp 5. Improvement based on block-neighborhood
tampering characteristics: In addition to the detection
index correction for tampered region in step 4, the prob-
ability of false reject in the non-tampered region can also
be reduced according to block-neighborhood tampering
characteristics. The modification of tamper detection index
is:
42
5=12
4
4
0, =11
==
,
m
ifmand mand
mN
mothers
(4)
Note, 1
and 2
are determined by simulation such
that the probability of false detection is minimized.
4. Image Recovery
All blocks in the test image are marked as either valid or
invalid after tamper detectio n. The invalid block n eeds to
be recovered using the restorstion watermark section that
is embedded in the other block. In the proposed scheme,
since two copies of restorstion watermark section are
embedded, the invalid block can be recovered if any one
of the two blocks that the restorstion watermark section
embedded into is valid. In this case, by padding the ex-
tracted 6-bit restoration watermark section with two 0s to
the end, the image recovery process is just replacing the
intensity of each pixel within the invalid block with this
new 8-bit intensity. To further improve the recovered
image quality, the invalid blocks without valid restor-
stion watermark section can be recovered by the average
intensity of the n eighboring valid pixels.
5. Experimental Results
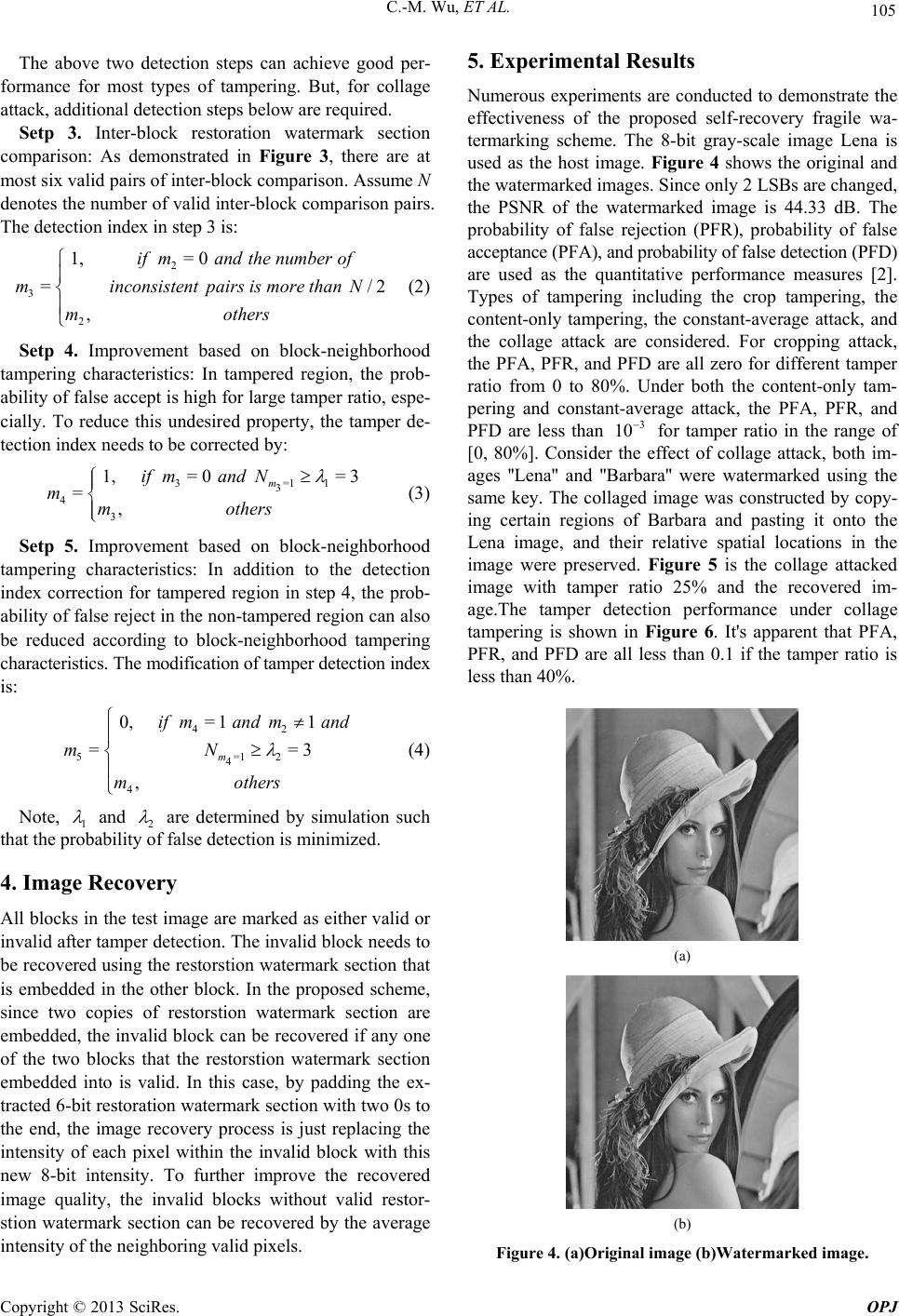
Numerous experiments are conducted to demonstrate the
effectiveness of the proposed self-recovery fragile wa-
termarking scheme. The 8-bit gray-scale image Lena is
used as the host image. Figure 4 shows the original and
the watermarked images. Since only 2 LSBs are changed,
the PSNR of the watermarked image is 44.33 dB. The
probability of false rejection (PFR), probability of false
acceptance (PFA), and probability of false detection (PFD)
are used as the quantitative performance measures [2].
Types of tampering including the crop tampering, the
content-only tampering, the constant-average attack, and
the collage attack are considered. For cropping attack,
the PFA, PFR, and PFD are all zero for different tamper
ratio from 0 to 80%. Under both the content-only tam-
pering and constant-average attack, the PFA, PFR, and
PFD are less than 3
10
for tamper ratio in the range of
[0, 80%]. Consider the effect of collage attack, both im-
ages ''Lena'' and ''Barbara'' were watermarked using the
same key. The collaged image was constructed by copy-
ing certain regions of Barbara and pasting it onto the
Lena image, and their relative spatial locations in the
image were preserved. Figure 5 is the collage attacked
image with tamper ratio 25% and the recovered im-
age.The tamper detection performance under collage
tampering is shown in Figure 6. It's apparent that PFA,
PFR, and PFD are all less than 0.1 if the tamper ratio is
less than 40%.
(a)
(b)
Figure 4. (a)Original image (b)Watermarked image.
Copyright © 2013 SciRes. OPJ