Journal of Signal and Information Processing
Vol.5 No.3(2014), Article
ID:48308,6
pages
DOI:10.4236/jsip.2014.53011
Mobile Data Mining-Based Services on the Base of Mobile Device Management (MDM) System
Mazin Omar Khairo
Management of Information Technology Department, Umm Al-Qura University, Mecca, KSA
Email: mazin1390@gmail.com
Copyright © 2014 by author and Scientific Research Publishing Inc.
This work is licensed under the Creative Commons Attribution International License (CC BY).
http://creativecommons.org/licenses/by/4.0/



Another approach is to define the position of a mobile device based on signal strength (the Received Signal Strength-RSS) access points from the Wi-Fi modules for mobile devices. Methods of data processing RSS (radio DNA fingerprinting).
ABSTRACT
Client software on mobile devices that can cause the remote control perform data mining tasks and show production results is significantly added the value for the nomadic users and organizations that need to perform data analysis stored in the repository, far away from the site, where users work, allowing them to generate knowledge regardless of their physical location. This paper presents new data analysis methods and new ways to detect people work location via mobile computing technology. The growing number of applications, content, and data can be accessed from a wide range of devices. It becomes necessary to introduce a centralized mobile device management. MDM is a KDE software package working with enterprise systems using mobile devices. The paper discussed the design system in detail.
Keywords:Data Mining, Mobile Device Management, User Recommendation, KDE Software Package

1. Introduction
1.1. Mobile Data Mining
Data analysis is a complex process that often needs remote resources (i.e. computers, software, databases, files, etc.) and people (i.e. analysts, experts, end users). Recent data mining techniques are used to analyze disparate data sets.
A mobile data mining may include several application scenarios in which Mobile device can play the role of manufacturer’s data, Data Analyzer, remote client data miners, or a combination of them. More specifically, we can imagine three main scenarios for mobile data mining [1] [2] :
• Mobile device is used as a terminal for ubiquitous access to a remote server that provides some data mining services. In this scenario, the server parses the data and stores it in a local or a distributed database, then sends the results to the data mining task of the mobile device for rendering.
• Data obtained in the mobile context are going to mobile, and sent in a stream to a remote server where they stored in the local database. Data shall be periodically assessed using specific data mining algorithms and the results will be used to make decisions for a specific goal.
• Mobile devices are used to perform data mining. But because of limited storage space and computing power of modern mobile devices, right now it is not realistic to perform the entire data mining tasks on a small device. However, portable devices can run some steps of data mining tasks (i.e., the choice of data and preprocessing is shown in Figure 1).
1.2. Mobile Device Management
Analysis the trends of mobile technologies uses shows the relevance of their application was in educational activities for solving pedagogical tasks and for remote access to the network and specialized resources and services of the institution.
Many universities in the world actively implement different sets of services, Management of the proliferation of applications, policy, security, services [3] . MDM system functions are protection and management for data and applications, as well as central-oriented system information functions [3] .
MDM system results in streamlined user devices out of the concept of “Bring Your Own Device (BYOD)”, to access corporate event-based information resources and services of the organization. MDM, together with the BYOD, are one of the most promising approaches in insert the mobile services in education [4] and allows you to use its own E-hammer devices students and Cove for new forms of training, new options for the use of educational space of the University Committee, dealing with contemporary artistic, pedagogical and methodological challenges.
General scheme of the decision on the provision of services based on, were using the MDM, is shown in Figure 2. Identification of each user-designated by MDM, that each mobile device communicates information wereMDM server. Location-based Services (LBS), use the information in accordance with its functionality.
The location of the user’s first mobile device can be obtained through the following approaches [5] :
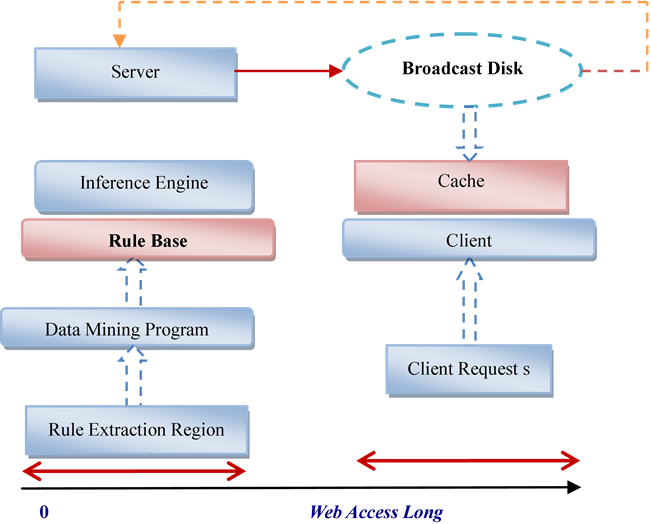
Figure 1. Working of location Based services using data mining.
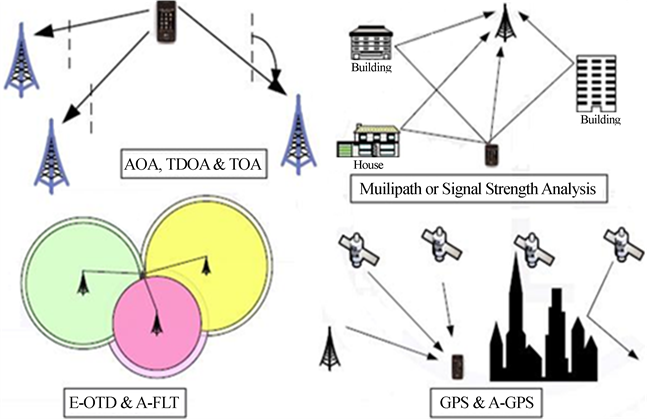
Figure 2. General scheme of the decision on the provision of services.
• Using integrated mobile platform.
• On the basis of data received from external equipment.
The architecture consists of three types of components:
• Data providers: applications that create the data to be mined.
• Mobile clients: applications that require data mining Computing on remote data.
• production servers: server nodes that are used for data storage, data generated providers and to perform data mining tasks presented to mobile clients
1.3. Geo-Tagging Using the Built-in Means of Mobile Platforms
The major producers of operating systems (OS) for mobile devices offer built-in Geolocation features. To determine the location of a mobile device is a special agent for the acquisition of data from the mobile OS and transfer them to the server MDM.
Usually, data on mobile devices is only possible if the programs agent on your mobile device is active or is automatically activated, periodically raises do not need running in the background [4] .
The three most common operating systems for mobile platforms Apple iOS, Google Android, and Microsoft Windows Phone support the ability to run background software agents, Dawn on your mobile device as a geo-location service client.
Operating system transfers control to this programmed under any of the following conditions [6] [7] :
• Expiration of the specified time inter-shaft.
• Changing the geographical position of the mobile device by the specified threshold.
2. Geo-Reference a Mobile Device to a Single Access Point
This approach provides data analysis with wireless access points Wi-Fi networks and geo-mobile device to the access point to which it is connected.
Most of the modern access points allow you to:
• Know information about the Wi-Fi connected devices using the built-in operating system.
• A server component running on a corporate data network.
• This component on the schedule that establishes a connection to the access point and sends the information about the connected mobile.
If the configuration deployed in the Organization’s Wi-Fi network, wireless access Controllers, contains information about the connected mobile devices can be obtained directly from the controller as shown in Figure 3.
The third way is linked to the deployment of a centralized solution that provides the ability to define locations, connected mobile devices using wireless network infrastructure [8] .
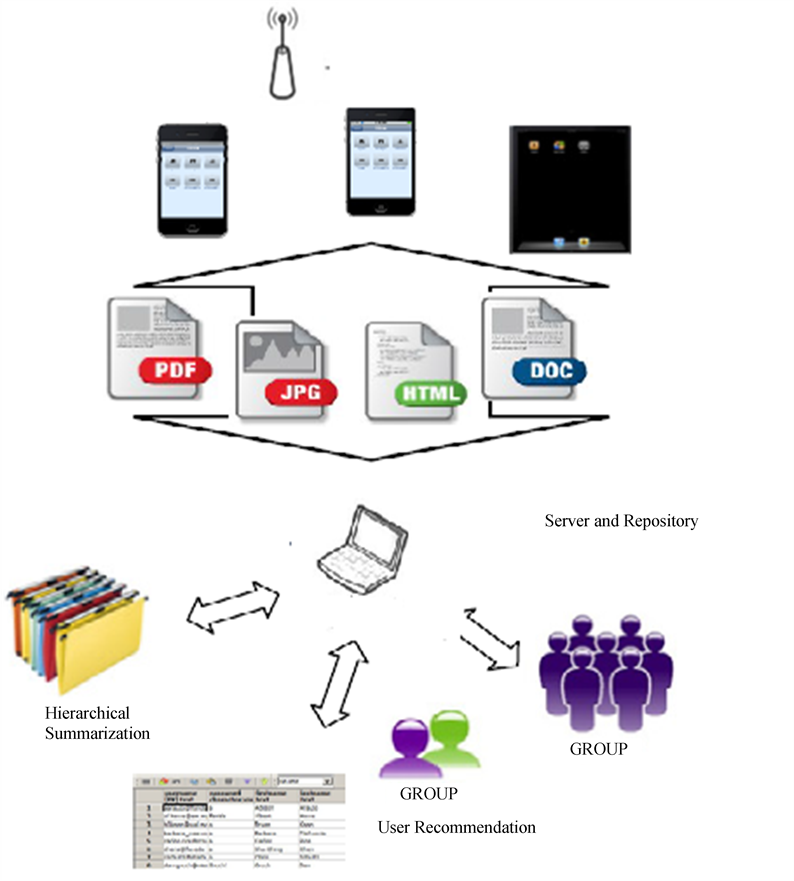
Figure 3. Geo-location mobile device data with wireless controller.
For example, Cisco proposes to use the Mobile Service Engine in conjunction with the Cisco Unified Wireless Network (CUWN) [9] [10] . This allows you to get information about the connected mobile devices within the wireless network deployed in premises on different floors of buildings to receive notification of a change in the position of a mobile device.
For more accurate determination for the location of the connected wireless device using information gathered from various elements of network infrastructure and algorithm of TDOA (Time Difference of Arrival).
Integrated Solutions That Use Data from Different Equipment
Another approach is to define the position of a mobile device based on signal strength (the Received Signal Strength-RSS) access points from the Wi-Fi modules for mobile devices. Methods of data processing RSS (radio DNA fingerprinting).
The triangulation method is based on the known position of base stations (access points), and they emitted a signal of known yield; in these circumstances, the level of attenuation from different stations allows you to calculate the position of the receiver of a mobile device. But the accuracy of this method is generally very low, and it is more suitable for operation on positive base stations of cellular communication network [11] (Figure 4).
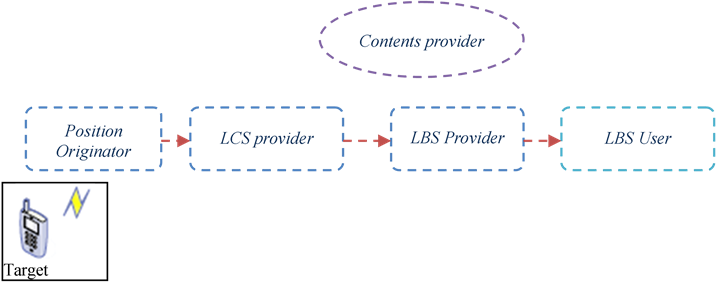
Figure 4. LBS-service Diagram.
3. Server Location
The Identify phase were of Wi-Fi mobile device module is used for the measurement of current-level signals from different access points, and on the basis of comparison of data obtained with the Radio prints is determined by the place-the position of the mobile device.
Development a methods for building Radio prints and calculation algorithms for radio positioning prints is a difficult scientific challenge, of all the mobile platform Android only forms provides external programmatic interfaces to the received signal level for available Wi-Fi networks, so this method cannot be considered as a universal solution [12] .
The most promising is the fingerprint matching algorithm. That, in the view of the need for long-term storage of calibration and calibration information, as well as static maps signal capacity, implying a lack of change in the production environment, this algorithm is not quite adequate.
In addition to approaches using existing Wi-Fi infrastructure, there are also solutions based on the installation of additional equipment, and special designed to ensure accurate positioning of mobile devices. An example of such a decision is the product of I.T.S (Indoor Triangulation System).
4. Location-Based Services
Provided by the leading universities of the world (for example: Massachusetts Institute of Technology, Stanford university, and Harvard university), to select educational institutions, the following major categories of location-based services:
Emergency services applied in emergency situations when a person cannot or unable to determine his location, Mass notification, inform users (based on their actual location).
Navigation services meet the needs of users in determining the direction of the current location: Background information on routes throughout the institution, taking into account the information on the various types of constraints, repairs, activities that impede the passage.
Information services: mobile yellow pages, messages about events near: The nearest classroom facilities, canteens, cafes. Information on conducting the next events-seminars gatherings.
Advertising services: provide advertisers’ access to a personalized target audience located in the current location: Coming to mobile advertising sponsors University near the laboratories equipped for sponsorship money, Services for tracking users.
Automatic determination of the list of persons attending the event lecture, seminar, meeting, on the basis of the social location of the participants.
Social networking: with the ability to obtain information about the location of the users may be deployed around United in virtual groups and see on their mobile device positioning of the participants in these groups; Billing services of dynamic quote for services or content depending on the user’s location [13] .
5. Open CellId Technology to Build LBS Applications
When the mobile phone is not equipped with a GPS equipment and network infrastructure does not support the positioning of the terminal or the manufacturer of particular device does not provide an API to get the coordinates for the location of the device, you can use shared technology OpenCellId, The idea is similar to OpenCellId Cell ID technology. But, unlike her, the coordinates of the Subscriber are not evaluated your mobile operator, and returns from the public database via the Internet from a mobile device. That is, to use it enough to phone had Internet access and knew the number of the closest cell cellular network.
OpenCellId—is to create a complete database cell coordinates all mobile operators worldwide. The project is located on the World Wide Web: (www.opencellid.org) and provides free access to the data and tools for supplementing and obtain information about the location of the cells. The project is a leading provider of location-based services.
The downside of technology is low fidelity OpenCellId positioning device, which can range from a few hundred meters to several kilometers. This is due to the different density of the network in different territories. Such precision can be critical for exact positioning, but in other cases it is enough. Recently, technology, thanks to the popularity gained OpenCellId transparent integration with Google Map, OpenCellId technology allows anyone to write and use mobile application for expansion of the database and get information about its location on the current cell. OpenCellId provides an API for working with the database. This is the usual REST APIS, which are two important add calls and get measure/cell and many more. Measure/add-adds the cell options in the database and is used by applications that extend the content of the database. To add data to the database, you need a registration key to OpenCellID. This key is used by the API to prevent false data into the database. Measure/add function call is as follows:
6. CellID with RSPB-UMTS
The RSPB-gives information on the loss of signal power transmitter (BS) you to define the distance to the phone on the reference signal power loss A-GPS (Assisted GPS), the method uses the global positioning system, with support from the network infrastructure. The mobile phone must be embedded GPS module, and “part of computing function is transferred to the MLC for lower power consumption and faster positioning [14] .
Coordinate calculation of proceeds as follows. GPS-signal is received on the mobile phone, then it is passed to the REF, which calculates the coordinates of the phone and sends them back. Base stations, receiving the signal, shall be equipped with radiotelephone in blocks to determine the location of the LMU. The positioning is initiated by the Subscriber, and subscriber data on transfers ends its seat. The network makes it easier to search for satellites, indicating what to look for. “The accuracy of the calculations can be from 5 to 50 meters, while the normal GPS provides from 0.1 to 30”.
Moreover, in some networks (e.g., CDMA) base stations can be equipped with your GPS antennas and receivers. They can act as a Repeater signal from satellites, it understandably raised additional error, and positioning accuracy is reduced (from 5 to 400 meters). So, is the work of the service even where there is no direct visibility of satellites or signal is weak (spaces included). The current position is from 20 to 40seconds, on average, it is still 20 seconds, Shifting part of the functions of the network equipment allows you to reduce the size of the phone, maximize their working time-today they are virtually indistinguishable from conventional cellular phones. However, this model of the higher price range, because you want to not only change the tube, but a network infrastructure [15] .
The relative accuracy of different methods of positioning obviously, the best possible accuracy gives traditional GPS and A-GPS. Show in Figure 5.
From the above review, the only positioning technology based on knowledge of coatings (CellId, etc.) do not require additions to the network infrastructure and improvements to the phone, To install the bundled software MLC. The implementation of technologies that are based on calculations of the time delays (E-OTD, TDOA, etc.)Involves the equipping of all base stations, blocks of LMU “To ensure the high accuracy involves synchronizing the work of those units within the whole network, which usually leads to the use of each block of the GPS receiver, Network software should also be subjected to serious modifications to the cell phonoreception at least three base stations [16] ”.
7. Conciliation
This paper presents new data analysis methods and new ways to detect people work location via the mobile
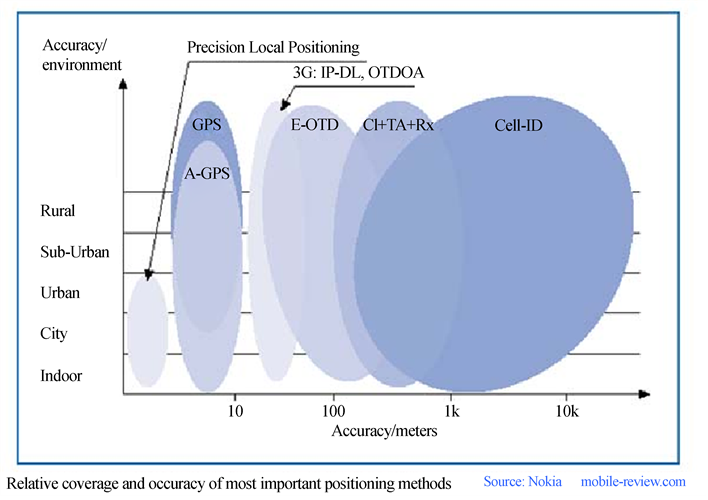
Figure 5. Comparison of different methods of positioning accuracy in cellular networks.
computing technology.
Approach to mobile software technologies makes easier the implementation of mobile application, detection of heterogeneous knowledge and common scenarios where data processing may migrate across different locations.
• Automatic registration for the lessons and activities based on real locations.
• Automatic locking and unlocking mobile sensors in accordance with the Education Act (based on location, schedule).
• Wireless connectivity to nearby devices, printers, projectors, various multimedia devices;
• Wireless connectivity for educational and research purposes to nearby measuring instruments/sensors.
The use of mobile devices for educational purposes has become a reality. Many universities in the world have already started to implement systems that allow students to use mobile devices in the learning process. One of the most promising is the introduction of services offered to students based on their location.
References
- Lennon, R.G. (2012) Bring Your Own Device (BYOD) with Cloud 4 Education. Proceedings of the 3rd Annual Conference on Systems, Programming and Applications: Software for Humanity, New York, 171-180.
- Wilson, S. and McCarthy, G. (2010) The Mobile University: From the Library to the Campus. Reference Services Review, 38, 214-225.
- Gartner IT-Glossary. http://www.gartner.com/it-glossary/mobile-device-manage-mentmdm/
- Hristidis, V., Chen, S., Li, T., Luis, S. and Deng, Y. (2010) Survey of Data Management and Analysis in Disaster Situations. The Journal of Systems and Software, 83, 1701-1714. http://dx.doi.org/10.1016/j.jss.2010.04.065
- Fielding, R.T. (2000) Architectural Styles and the Design of Network-Based Software Architectures. Doctoral Dissertation, University of California, Irvine.
- Zheng, L., Shen, C., Tang, L., Li, T., Luis, S., Chen, S. and Hristidis, V. (2010) Using Data Mining Techniques to Address Critical Information Exchange Needs in Disaster Affected Public-Private Networks. KDD’10, 125-134.
- Choudhury, M.D., Mason, W.A., Hofman, J.M. and Watts, D.J. (2010) Inferring Relevant Social Networks from Interpersonal Communication. Proceedings of the 19th International Conference on World Wide Web, Raleigh, 26-30 April 2010, 10 p.
- Kahanda, I. and Neville, J. (2009) Using Transactional Information to Predict Link Strength in Online Social Networks. Proceedings of the 3rd International Conference on Weblogs and Social Media (ICWSM), West Lafayette, June 2009, 74-81.
- Ye, Y., et al. (2009) Mining Individual Life Pattern Based on Location History. 10th International Conference on Mobile Data Management: Systems, Services and Middleware, MDM’09, Taipei, 18-20 May 2009, 1-10.
- Bao, T.F., et al. (2012) Mining Significant Places from Cell ID Trajectories: A Geo-Grid Based Approach. 2012 IEEE 13th International Conference on Mobile Data Management (MDM), Bengaluru, 23-26 July 2012, 288-293.
- Lu, J.L. and Sun, G.J. (2012) Location-Based Intelligent Services of Scenic Areas. 2012 2nd International Conference on Consumer Electronics, Communications and Networks (CECNet), Yichang, 21-23 April 2012, 1882-1885.
- Emery, S. (2012) Factors for Consideration When Developing a Bring Your Own Device (BYOD) Strategy in Higher Education. http://hdl.handle.net/1794/12254
- Apple Inc. (2014) Location Awareness Programming. http://developer.apple.com/library/ios/documentation/UserExperience/Conceptual/Location AwarenessPG/LocationAwarenessPG.pdf

