Journal of Power and Energy Engineering
Vol.05 No.04(2017), Article ID:75629,10 pages
10.4236/jpee.2017.54003
System Vulnerability Analysis Using Graph Pathfinding Strategies in Partitioned Networks
Milad Ghiasi Rad1, Pedram Gharghabi2*, Mohiyeddin Rahmani3, Bamdad Falahati4
1Computer Science and Engineering Department, University of Nebraska-Lincoln, Lincoln, United States
2Department of Computer and Electrical Engineering, Mississippi State University, Mississippi, United States
3Department of Electrical Engineering, Amirkabir University of Technology, Tehran, Iran
4Engineering Services, Schweitzer Engineering Laboratories, Inc., Pullman, WA, United States

Copyright © 2017 by authors and Scientific Research Publishing Inc.
This work is licensed under the Creative Commons Attribution International License (CC BY 4.0).
http://creativecommons.org/licenses/by/4.0/



Received: March 30, 2017; Accepted: April 23, 2017; Published: April 26, 2017
ABSTRACT
In this paper, a new method has been introduced to find the most vulnerable lines in the system dynamically in an interconnected power system to help with the security and load flow analysis in these networks. Using the localization of power networks, the power grid can be divided into several divisions of sub-networks in which, the connection of the elements is stronger than the elements outside of that division. By using our proposed method, the probable important lines in the network can be identified to do the placement of the protection apparatus and planning for the extra extensions in the system. In this paper, we have studied the pathfinding strategies in most vulnerable line detection in a partitioned network. The method has been tested on IEEE39- bus system which is partitioned using hierarchical spectral clustering to show the feasibility of the proposed method.
Keywords:
Power Systems Network, Graph Partitioning, Path Finding, Vulnerability Analysis

1. Introduction
In the past few years, the power systems analysis has been evolved and improved from the traditional method of analysis, like Kirchhoff’s, law into new methods that have better coverage on the more competitive problems. These methods do not look at the network as a whole identity but as a set of discrete or more independent fragmented partitions that each can be studied with more independence compared to the other sub-networks.
Several methods have been introduced to perform the partitioning in power networks. Schaeffer [1] reviewed some methods and definitions on graph clustering including the hierarchical and divisive global clustering. Raak et al. [2] used Koopman mode analysis (KMA) to partition the network using voltage of the buses. Although this method classifies the network based on the load flow properties of the bus, it lacks the ability to consider the network as a physical entity while doing the partitioning. Spectral clustering is more preferable because of its ability to consider the physical properties of the network in clustering [3] [4] [5] . Eigenvectors of the network matrix are also proper measures in finding the groups of vertices in which the edge density is higher than the average [6] . It is helpful in finding the strongest connected components in the network which are the possible sub-networks. The decentralized networks can help to perform the analysis in different aspects of the power systems. For example, Chavali et al. [7] used factor graphs to find the dependencies between the neighboring areas, or Raakelt et al. [8] used KMA again for modal decomposition and network partitioning.
There have been some graph based methods to find the contribution of each generation unit in the power flow of each line, such as [9] , where AC load flow has been used to analyze the network. It is a negative aspect of this method because it cannot analyze the network without the load flow. Despite this fact, this method can help to find better solutions for the local marginal prices in the presence of harmonics in transmission level, as they can increase the prices [10] . It is also useful in placement and assignment prediction of pump storage systems for the generation units in which, the hydro storage is designed based on the contribution of the generation unit in the system [11] .
The method we are presenting in this paper is focused on finding the most vulnerable lines in a partitioned system. These lines have the most effects in increasing the connectivity of the network. The disconnection of any of these lines can affect the reliability of the system and reduce the robustness of the system. There are existing papers that have investigated this problem [12] , but not in a method that utilizes a partitioned network. This method uses the partitioned network using spectral clustering as a case study to find the lines with the highest influence and importance in the interconnection of the network.
In this paper, Chapter 2 discusses on the basics of the methods used in this paper on different levels of analysis. Chapter 3 focuses on the analysis of the results obtained using methods obtained in previous chapter. Chapter 4 studies the 39-bus system using the proposed method, and Chapter 5 summarizes the novelty and contribution in this paper.
2. Basics of Methodology
The complexity of power systems is one of the main issues that prevents the researchers to analyze large networks conveniently. The absence of localization in finding the most vulnerable line in the system can lead to missing some important points such as the physically localized networks by higher transmission level lines. Considering this, a method can be developed to translate the network graph into a more understandable network in which the analysis can be performed in different levels of connection, and the results can be joined together for further analysis.
2.1. A Proposed Weighting Strategy
A very large power systems network is difficult to understand if it is not analyzed using graph analysis methods. The problem of finding the most vulnerable line in the system is one of the most flexible problems that can be looked at it from a different perspective. The main stream in the methodology of finding the most vulnerable line in the system using the graph partitioning is to identify the line most involved in network connection. Based on this approach, the assigned weight of a line is highly proportionate to the number of paths it is involved in the system. Figure 1 shows this idea in which i, j, and k represents three distinct nodes and the weights on each edge (which will be referred as lines) are integer values.
The weights assigned to each line is represented as the number of paths in which line is presented to connect the two nodes i and j. By referring to this weighting system, it can be found that the line i-k has the highest weight. This implies that, this line has the highest importance in at least i to j connection. This weighting system is a good impression for a system that aims to find the most sensitive line in the system represented in (1) for the general line m-n.
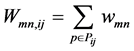 (1)
(1)
where, Wmn,ij is the total weight of the line between the two nodes m and n considering all the paths between the nodes i and j, wmn is the assigned weight for the existing paths p in the set of all the possible paths Pij between the nodes i and j that goes through the line m-n where it is defined in (2) where l is defined as a loop.
 (2)
(2)
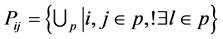
By expanding this method into other nodes of the graph, new weights can be calculated to add up to the current weights. As an example, for the three nodes system, the total of three different pairs of the nodes i, j, and k can be found to be used in the method. In this case, the weight for each line is the sum of the
Figure 1. Line weighting example applied to a simple network of three nodes and three lines for the paths between the nodes i and j.
numbers they appear in the paths between all the pairs, which is shown in Figure 2. Based on (2), the weight for the line i-k will be equal to 3 which is higher than the value for the other two lines. This shows the level of importance for this line in the network. Using this weighting method, a ranking can be made to differentiate between different lines. The two lines connecting k to j have the same weights, which makes them to be in the same level of importance after i-k line. This method can be extended into more complex problems.
 (3)
(3)
where, Wmn is the total weight of the line between the two nodes m and n, V is the set of the nodes, wmn is the assigned weight for the existing paths p in the set of all the possible paths Pij between the nodes i and j if goes through the line m-n. If the line from m-n is not present in any path from the node i to j, wmn will be considered zero.
2.2. Higher Level Analysis
In a more complex graph which has more nodes and edges, implementing a simple weighting strategy can be misleading due to reducing the depth of analysis in the network. Partitioning the network graph is a very useful method in examining the vulnerability analysis in big networks. Using this idea, the analysis can take place in a specific partition independent to the rest of the network. In the higher level, the network can be analyzed based on the previous level output. Figure 3 shows a schema of the idea to be used in the pathfinding method. In this model, the network is a two-level graph.
The first level analysis is the level with the highest resolution. This analysis is conducted to find the weights of a more compact network like the sub-networks. In the sub-networks, the nodes can be classified into two main classes of terminal and non-terminal nodes. Terminal nodes are the nodes directly connected to one or more other sub-networks. Terminal nodes can represent the sub-net- works in the outside network.
The second level analysis is conducted in the network with a lower resolution compared to the first level analysis. This network consists of the network of the sub-networks terminal nodes and the edges connecting them. The sub-networks
Figure 2. Line weighting example applied on a simple network of three nodes and three lines for all the possible paths between the pairs of the nodes.
Figure 3. The example model of three clustered networks. The terminal nodes of i, p, r, n, l, and j are at the end of the bold lines that connect the sub networks.
play the role of the new nodes in the higher-level network, and the paths between them can be summarized into all the possible paths between them. In this case, the sub-networks (a), (b), and (c) are the new super-nodes of the second level network which are connected by the lines between the terminal nodes of i, p, r, n, l, and j. Therefore, the second-level network has three super-nodes and three edges. This topology can be more complicated for different problems.
The second level analysis can be applied to any other number of higher levels with lower resolutions. However in this paper, two level analyses are considered more favorable in terms of computational complications.
3. Two Level Analyses
The vulnerability analysis of the power systems can use the foretold method to find the most sensitive line in the network. To justify the results of the first and second-level analysis together, the path finding methods should be enhanced to find the lines that appear in the most paths. Depth first search (DFS) method is a reliable method to find all the possible paths between two nodes. Since DFS satisfies the constraint of including only distinct nodes in any path, it has been used in this paper. After partitioning the network, the method will try to find all the path between any two nodes in the network to assign the weights to the lines.
The first step is to find all the possible paths between any pair in each of the sub-networks. The paths will be stored in a database. Then, between all the stored paths, the lines passing through other paths will be discovered. For example, in Figure 2, the upper path of i to j, interacts with the upper path from k to j. Thus, it can be implied that the total number of paths between i and j is the multiplication of the number of path from i to k and k to j presented in (4). Another interesting case is a loop that exists in the path finding method. In this case, the loop can be modeled as a super node and the effect of the loop will be ignored.
The second level analysis takes place after the first level. In this step, the super nodes and the lines between the sub-networks are considered as the new networks. The path between each of the terminal nodes will be found, and its sum with the paths in the sub-networks is considered.
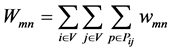
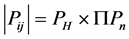 (4)
(4)
where,  is the total number of paths between the nodes i and j, PH is the number of path between the nodes in the high-network, Pn is the number pf path in the sub-network n, and S is the set of sub-networks.
is the total number of paths between the nodes i and j, PH is the number of path between the nodes in the high-network, Pn is the number pf path in the sub-network n, and S is the set of sub-networks.
Based on the Formula (4), the total number of paths is the multiplication of the number of paths in each sub-network, if that sub-network can be a distinct super node in the higher-level graph, and the number of the paths in the higher-level. Also, the same rules on the exceptions apply to the higher levels, such as a terminal in a sub-network with a single terminal does not import the lower level network into the higher-level network. This enforces the idea of the super node described earlier in other works. The other rule is that, the path between the terminal nodes of a sub-network that is participating in a higher level and participates more than once in the path cannot share an edge in the sub-network. The paths found using the foretold rules will be distinct, and the weights assigned to the lines using them are accountable.
4. Case Study
To check the feasibility of the proposed model, a case study was performed on IEEE 39-bus system. Hierarchical spectral clustering was used in order to partition the network into 4 sub-networks [5] as shown in Figure 4. This partitioning
Figure 4. Graph view of IEEE 39-bus system clustered into 4 sub-net- works. The terminal nodes are connected by the dashed lines.
shows 6 lines connecting the terminal nodes which is minimal for connecting 4 sub networks with the total of 10 terminal nodes shown in Figure 5. The resulted network is an undirected and unweighted graph which is qualified for the simulations.
The proposed method was applied to the 39-bus network. The Demand and Generation units create two different classes connected through the lines in sub-networks and the higher-level network. Totally, 21 demands and 10 generations are placed on different buses which their placement is presented in Table 1.
To better understand the effect of the proposed method, as a demo, the method was tested on the connections between the generation at the bus 39 and the demand at the bus 16 for the added weight of 1 for every time the line is in a path between these two buses. Table 2 shows the result of this analysis for the first 8 vulnerable lines. Based on the analysis, the line between the buses 3 and 4 and the line between the buses 13 and 14 have the highest scores to be the most vulnerable lines in connection between the power injected by the bus 39 and the power absorbed by the bus 16. These two lines have appeared in the paths between the buses 39 and 16 for 22 and 20 times respectively. Any disconnection of these two lines reduces the robustness of the network more than disconnection of the other lines if the buses 39 and 16 are the only buses in the system injecting or absorbing power.
A useful update to the program can be performed by considering the line inductances. The higher inductance means lower permeability for the injected power to go through the line. By using the reverse inductance values of the lines as the weight, the most vulnerable line will shift to the line between the buses 5 and 6 with the weight 5000. The next more vulnerable line is the line between
Figure 5. Simplified IEEE 39-bus system into 4 sub-networks. The dashed lines represent the connections between the terminals and the solid lines show the paths between the terminals inside the sub-networks.
Table 1. Generations and demands in IEEE 39-bus system.
the buses 7 and 8 with the weight 2826 which shows a significant difference between the first two important lines. The line 5 to 6 owes this importance to its high appearance in the paths between the buses 39 and 16. The new result is presented in Table 3 for the first 10 important lines.
By considering all the generations and demands, the complete network was tested for the constant weight of 1 and the reverse of the lines inductance values which their results are presented in Table 4 and Table 5. As it is clear, for the constant add up weight of 1, the line from the bus 6 to 11 has the most vulnerability probably due to its importance in connecting the left and right of the largest sub-network.
When the inductances are considered, the line between the buses 5 and 6 still has the highest importance. This importance stems from the low inductance of the line and its placement that supports the line between the buses 5 and 6 in a variety of paths.
By removing the most vulnerable line between the bus 5 to 6 from the network, in presence of inductance values, running the simulation shows that the line from the bus 7 to 8 is still the most vulnerable line with the total effect of 10
Table 2. Simulation results based on the proposed model between the generation at bus 39 and demand on bus 16 based on equal weighting strategy.
Table 3. Simulation results based on the proposed model between the generation at bus 39 and demand on bus 16 based on weighting influenced by inductance values.
Table 4. The lines weights based on the proposed method considering all the generations and demands in the network based on equal weighting strategy.
Table 5. The lines weights based on the proposed method considering all the generations and demands in the network based on lines inductances.
percent which shows 3 percent increase compared to the presence of the line from 5 to 6. If the network is considered without the inductance values and constant add up weights, the most vulnerable lines will move to the lines between the buses 4 and 5 also 8 and 9 respectively, which is a huge difference. This is because of disconnection happening between left and right of the sub-network. This shows that the vulnerability analysis is a dynamic method and with removal of any line in the network, its results may change.
5. Conclusion
In this paper, the importance of path finding in clustered networks was investigated in vulnerability analysis of the power systems. A method was developed in which the terminal nodes were connecting the sub-networks and were participating in the sub-networks. The sub-networks acted as a super node in the system to simplify the low-resolution representation of the system. Assigning the weights to the lines based on their appearance in the different connections conveyed a compelling measure on the importance of the lines. At this stage, the network was tested on IEEE 39-bus system clustered by hierarchical spectral clustering into 4 sub-networks. The constant weights or the weights induced by the line inductances showed different behaviors in the simulations and showed different lines as the most vulnerable lines. Although considering the constant weight is meaningful in some problems, inductance values are more meaningful in power system networks as they reversely affect the importance of the line between its neighbors.
Cite this paper
Rad, G.M., Gharghabi, P., Rahmani, M. and Falahati, B. (2017) System Vulnerability Analysis Using Graph Pathfinding Strategies in Partitioned Networks. Journal of Power and Energy Engineering, 5, 15-24. https://doi.org/10.4236/jpee.2017.54003
References
- 1. Schaeffer, S. E. (2007) Graph Clustering. Computer Science Review, 1, 27-64.
- 2. Raak, F., Susuki, Y. and Hikihara, T. (2015) Multi-Way Partitioning of Power Networks via Koopman Mode Analysis. IFAC-Papers on Line, 48, 421-426.
- 3. Quirós-Tortós, J., Wall, P., Ding, L. and Terzija, V. (2014) Determination of Sectionalising Strategies for Parallel Power System Restoration: A Spectral Clustering-Based Methodology. Electric Power Systems Research, 116, 381-390.
- 4. Rieser, A. (2015) A Topological Approach to Spectral Clustering. arXiv Preprint arXiv:1506.02633.
- 5. Sánchez-García, R.J., Fennelly, M., Norris, S., Wright, N., Niblo, G., Brodzki, J. and Bialek, J. W. (2014) Hierarchical Spectral Clustering of Power Grids. IEEE Transactions on Power Systems, 29, 2229-2237. https://doi.org/10.1109/TPWRS.2014.2306756
- 6. Newman, M.E. (2006) Finding Community Structure in Networks Using the Eigenvectors of Matrices. Physical Review E, 74, Article ID: 036104.
https://doi.org/10.1103/PhysRevE.74.036104 - 7. Chavali, P. and Nehorai, A. (2015) Distributed Power System State Estimation Using Factor Graphs. IEEE Transactions on Signal Processing, 63, 2864-2876.
https://doi.org/10.1109/TSP.2015.2413297 - 8. Raak, F., Susuki, Y. and Hikihara, T. (2016) Data-Driven Partitioning of Power networks via Koopman Mode Analysis. IEEE Transactions on Power Systems, 31, 2799-2808.
https://doi.org/10.1109/TPWRS.2015.2464779 - 9. Wu, F.F., Ni, Y. and Wei, P. (2000) Power Transfer Allocation for Open Access Using Graph Theory-Fundamentals and Applications in Systems without Loopflow. IEEE Transactions on Power Systems, 15, 923-929. https://doi.org/10.1109/59.871714
- 10. Norouzi, H., Abedi, S., Jamalzadeh, R., Rad, M.G. and Hosseinian, S.H. (2014) Modeling and Investigation of Harmonic Losses in Optimal Power Flow and Power System Locational Marginal Pricing. Energy, 68, 140-147. https://doi.org/10.1016/j.energy.2014.02.010
- 11. Ghaisi, M., Rahmani, M., Gharghabi, P., Zoghi, A. and Hosseinian, S.H. (2017) Scheduling a Wind Hydro-Pumped-Storage Unit Considering the Economical Optimization. American Journal of Electrical and Electronic Engineering, 5, 16-22.
- 12. Wang, Z., Scaglione, A. and Thomas, R.J. (2010) Electrical Centrality Measures for Electric Power Grid Vulnerability Analysis. 49th IEEE Conference on Decision and Control (CDC), 15-17 December 2010, Atlanta, 5792-5797. https://doi.org/10.1109/CDC.2010.5717964







