Reversible Di gital Image Wate rmarking Scheme Using Bit Replacement and Majority Algorithm Technique
Copyright © 2012 SciRes. JILSA
206
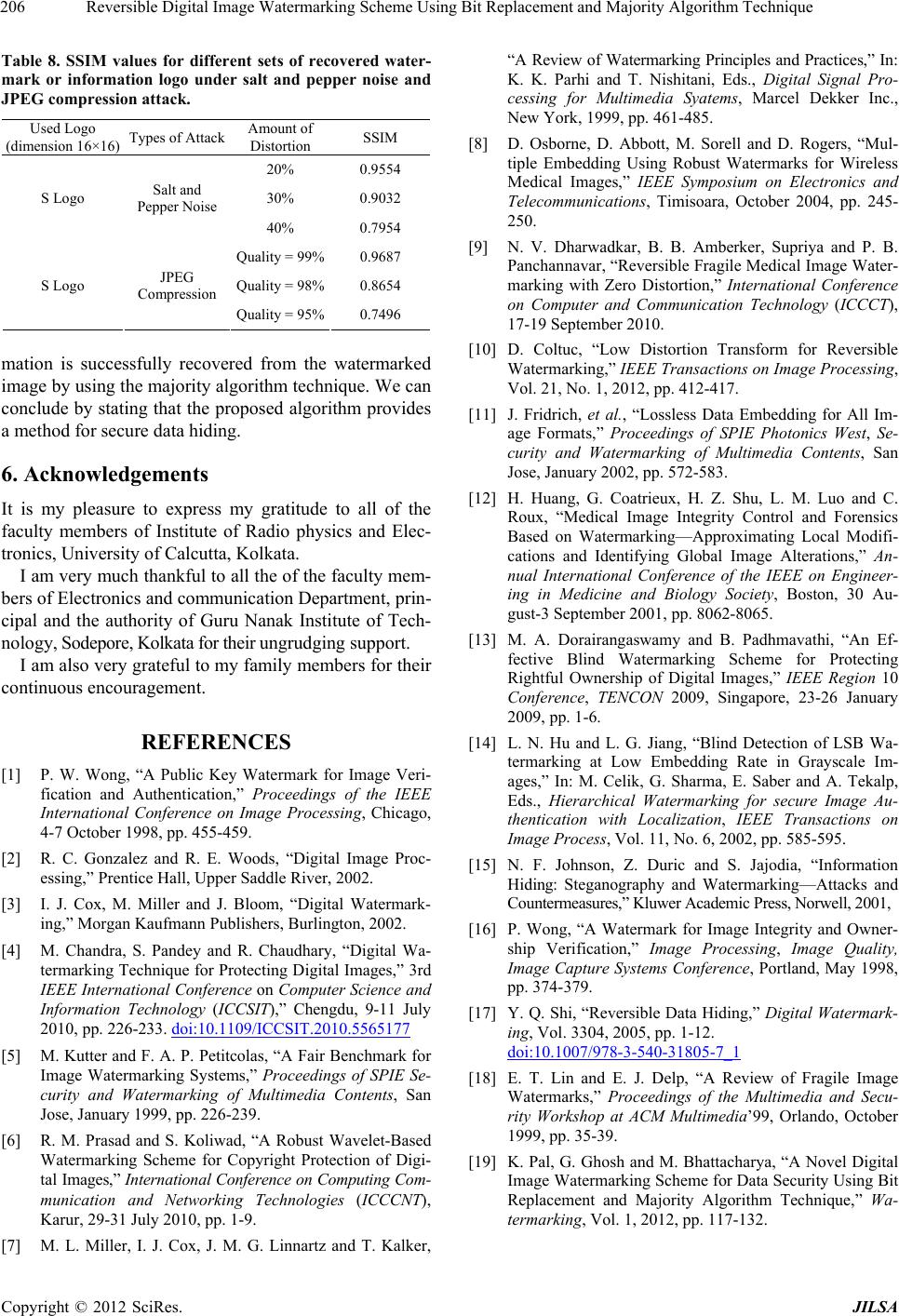
Table 8. SSIM values for different sets of recovered water-
mark or information logo under salt and pepper noise and
JPEG compression attack.
Used Logo
(dimension 16×16) Types of AttackAmount of
Distortion SSIM
20% 0.9554
30% 0.9032
S Logo Salt and
Pepper Noise
40% 0.7954
Quality = 99% 0.9687
Quality = 98% 0.8654 S Logo JPEG
Compression
Quality = 95% 0.7496
mation is successfully recovered from the watermarked
image by using the majority algorithm technique. We can
conclude by stating that the proposed algorithm provides
a method for secure data hiding.
6. Acknowledgements
It is my pleasure to express my gratitude to all of the
faculty members of Institute of Radio physics and Elec-
tronics, University of Calcutta, Kolkata.
I am very much thankful to all the of the facu lty mem-
bers of Electronics and communication Department, prin-
cipal and the authority of Guru Nanak Institute of Tech-
nology, S o d e po r e , K o lk a t a f o r t h e i r un grudgi ng support.
I am also very grateful to my fami ly memb er s fo r t he ir
continuous encouragement.
REFERENCES
[1] P. W. Wong, “A Public Key Watermark for Image Veri-
fication and Authentication,” Proceedings of the IEEE
International Conference on Image Processing, Chicago,
4-7 October 1998, pp. 455-459.
[2] R. C. Gonzalez and R. E. Woods, “Digital Image Proc-
essing,” Prentice Hall, Upper Saddle River, 2002.
[3] I. J. Cox, M. Miller and J. Bloom, “Digital Watermark-
ing,” Morgan Kaufmann Publishers, Burlington, 2002.
[4] M. Chandra, S. Pandey and R. Chaudhary, “Digital Wa-
termarking Technique for Protecting Digital Images,” 3rd
IEEE International Conference on Computer Science and
Information Technology (ICCSIT),” Chengdu, 9-11 July
2010, pp. 226-233. doi:10.1109/ICCSIT.2010.5565177
[5] M. Kutter and F. A. P. Petitcolas, “A Fair Benchmark for
Image Watermarking Systems,” Proceedings of SPIE Se-
curity and Watermarking of Multimedia Contents, San
Jose, January 1999, pp. 226-239.
[6] R. M. Prasad and S. Koliwad, “A Robust Wavelet-Based
Watermarking Scheme for Copyright Protection of Digi-
tal Images,” International Conference on Computing Com-
munication and Networking Technologies (ICCCNT),
Karur, 29-31 July 2010, pp. 1-9.
[7] M. L. Miller, I. J. Cox, J. M. G. Linnartz and T. Kalker,
“A Review of Watermarking Principles and Practices,” In:
K. K. Parhi and T. Nishitani, Eds., Digital Signal Pro-
cessing for Multimedia Syatems, Marcel Dekker Inc.,
New York, 1999, pp. 461-485.
[8] D. Osborne, D. Abbott, M. Sorell and D. Rogers, “Mul-
tiple Embedding Using Robust Watermarks for Wireless
Medical Images,” IEEE Symposium on Electronics and
Telecommunications, Timisoara, October 2004, pp. 245-
250.
[9] N. V. Dharwadkar, B. B. Amberker, Supriya and P. B.
Panchannavar, “Reversible Fragile Medical Image Water-
marking with Zero Distortion,” International Conference
on Computer and Communication Technology (ICCCT),
17-19 September 2010.
[10] D. Coltuc, “Low Distortion Transform for Reversible
Watermarking,” IEEE Transactions on Image Processing,
Vol. 21, No. 1, 2012, pp. 412-417.
[11] J. Fridrich, et al., “Lossless Data Embedding for All Im-
age Formats,” Proceedings of SPIE Photonics West, Se-
curity and Watermarking of Multimedia Contents, San
Jose, January 2002, pp. 572-583.
[12] H. Huang, G. Coatrieux, H. Z. Shu, L. M. Luo and C.
Roux, “Medical Image Integrity Control and Forensics
Based on Watermarking—Approximating Local Modifi-
cations and Identifying Global Image Alterations,” An-
nual International Conference of the IEEE on Engineer-
ing in Medicine and Biology Society, Boston, 30 Au-
gust-3 September 2001, pp. 8062-8065.
[13] M. A. Dorairangaswamy and B. Padhmavathi, “An Ef-
fective Blind Watermarking Scheme for Protecting
Rightful Ownership of Digital Images,” IEEE Region 10
Conference, TENCON 2009, Singapore, 23-26 January
2009, pp. 1-6.
[14] L. N. Hu and L. G. Jiang, “Blind Detection of LSB Wa-
termarking at Low Embedding Rate in Grayscale Im-
ages,” In: M. Celik, G. Sharma, E. Saber and A. Tekalp,
Eds., Hierarchical Watermarking for secure Image Au-
thentication with Localization, IEEE Transactions on
Image Process, Vol. 11, No. 6, 2002, pp. 585-595.
[15] N. F. Johnson, Z. Duric and S. Jajodia, “Information
Hiding: Steganography and Watermarking—Attacks and
Countermeasur es,” K luwer A cad emic Press , Norwell, 2 001,
[16] P. Wong, “A Watermark for Image Integrity and Owner-
ship Verification,” Image Processing, Image Quality,
Image Capture Systems Conference, Portland, May 1998,
pp. 374-379.
[17] Y. Q. Shi, “Reversible Data Hiding,” Digital Watermark-
ing, Vol. 3304, 2005, pp. 1-12.
doi:10.1007/978-3-540-31805-7_1
[18] E. T. Lin and E. J. Delp, “A Review of Fragile Image
Watermarks,” Proceedings of the Multimedia and Secu-
rity Workshop at ACM Multimedia’99, Orlando, October
1999, pp. 35-39.
[19] K. Pal, G. Ghosh and M. Bhattacharya, “A Novel Digital
Image Watermarking Scheme for Data Security Using Bi t
Replacement and Majority Algorithm Technique,” Wa-
termarking, Vol. 1, 2012, pp. 117-132.