776 R. IWAI ET AL.
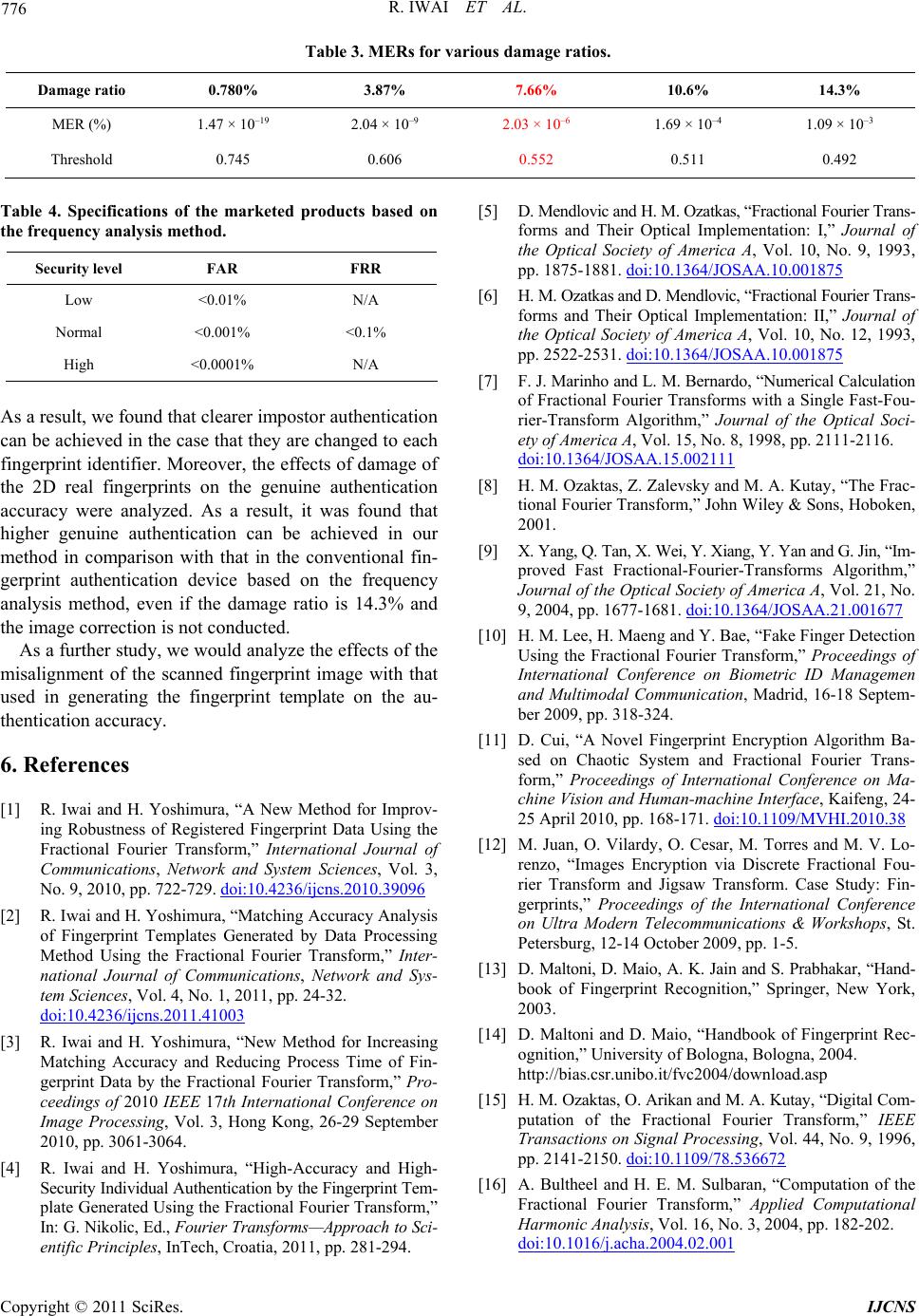
Table 3. MERs for various damage ratios.
Damage ratio 0.780% 3.87% 7.66% 10.6% 14.3%
MER (%) 1.47 × 10–19 2.04 × 10–9 2.03 × 10–6 1.69 × 10–4 1.09 × 10–3
Threshold 0.745 0.606 0.552 0.511 0.492
Table 4. Specifications of the marketed products based on
the frequency analysis method.
Security level FAR FRR
Low <0.01% N/A
Normal <0.001% <0.1%
High <0.0001% N/A
As a result, we found that clearer impostor authentication
can be achieved in the case that they are changed to each
fingerprint identifier. Moreover, the effects of damage of
the 2D real fingerprints on the genuine authentication
accuracy were analyzed. As a result, it was found that
higher genuine authentication can be achieved in our
method in comparison with that in the conventional fin-
gerprint authentication device based on the frequency
analysis method, even if the damage ratio is 14.3% and
the image correction is not conducted.
As a further study, we would analyze the effects of the
misalignment of the scanned fingerprint image with that
used in generating the fingerprint template on the au-
thentication accuracy.
6. References
[1] R. Iwai and H. Yoshimura, “A New Method for Improv-
ing Robustness of Registered Fingerprint Data Using the
Fractional Fourier Transform,” International Journal of
Communications, Network and System Sciences, Vol. 3,
No. 9, 2010, pp. 722-729. doi:10.4236/ijcns.2010.39096
[2] R. Iwai and H. Yoshimura, “Matching Accuracy Analysis
of Fingerprint Templates Generated by Data Processing
Method Using the Fractional Fourier Transform,” Inter-
national Journal of Communications, Network and Sys-
tem Sciences, Vol. 4, No. 1, 2011, pp. 24-32.
doi:10.4236/ijcns.2011.41003
[3] R. Iwai and H. Yoshimura, “New Method for Increasing
Matching Accuracy and Reducing Process Time of Fin-
gerprint Data by the Fractional Fourier Transform,” Pro-
ceedings of 2010 IEEE 17th International Conference on
Image Processing, Vol. 3, Hong Kong, 26-29 September
2010, pp. 3061-3064.
[4] R. Iwai and H. Yoshimura, “High-Accuracy and High-
Security Individual Authentication by the Fingerprint Tem-
plate Generated Using the Fractional Fourier Transform,”
In: G. Nikolic, Ed., Fourier Transforms—Approach to Sci-
entific Principles, InTech, Croatia, 2011, pp. 281-294.
[5] D. Mendlovic and H. M. Ozatkas, “Fractional Fourier Trans-
forms and Their Optical Implementation: I,” Journal of
the Optical Society of America A, Vol. 10, No. 9, 1993,
pp. 1875-1881. doi:10.1364/JOSAA.10.001875
[6] H. M. Ozatkas and D. Mendlovic, “Fractional Fourier Trans-
forms and Their Optical Implementation: II,” Journal of
the Optical Society of America A, Vol. 10, No. 12, 1993,
pp. 2522-2531. doi:10.1364/JOSAA.10.001875
[7] F. J. Marinho and L. M. Bernardo, “Numerical Calculation
of Fractional Fourier Transforms with a Single Fast-Fou-
rier-Transform Algorithm,” Journal of the Optical Soci-
ety of America A, Vol. 15, No. 8, 1998, pp. 2111-2116.
doi:10.1364/JOSAA.15.002111
[8] H. M. Ozaktas, Z. Zalevsky and M. A. Kutay, “The Frac-
tional Fourier Transform,” John Wiley & Sons, Hoboken,
2001.
[9] X. Yang, Q. Tan, X. Wei, Y. Xiang, Y. Yan and G. Jin, “Im-
proved Fast Fractional-Fourier-Transforms Algorithm,”
Journal of the Optical Society of America A, Vol. 21, No.
9, 2004, pp. 1677-1681. doi:10.1364/JOSAA.21.001677
[10] H. M. Lee, H. Maeng and Y. Bae, “Fake Finger Detection
Using the Fractional Fourier Transform,” Proceedings of
International Conference on Biometric ID Managemen
and Multimodal Communication, Madrid, 16-18 Septem-
ber 2009, pp. 318-324.
[11] D. Cui, “A Novel Fingerprint Encryption Algorithm Ba-
sed on Chaotic System and Fractional Fourier Trans-
form,” Proceedings of International Conference on Ma-
chine Vision and Human-machine Interface, Kaifeng, 24-
25 April 2010, pp. 168-171. doi:10.1109/MVHI.2010.38
[12] M. Juan, O. Vilardy, O. Cesar, M. Torres and M. V. Lo-
renzo, “Images Encryption via Discrete Fractional Fou-
rier Transform and Jigsaw Transform. Case Study: Fin-
gerprints,” Proceedings of the International Conference
on Ultra Modern Telecommunications & Workshops, St.
Petersburg, 12-14 October 2009, pp. 1-5.
[13] D. Maltoni, D. Maio, A. K. Jain and S. Prabhakar, “Hand-
book of Fingerprint Recognition,” Springer, New York,
2003.
[14] D. Maltoni and D. Maio, “Handbook of Fingerprint Rec-
ognition,” University of Bologna, Bologna, 2004.
http://bias.csr.unibo.it/fvc2004/download.asp
[15] H. M. Ozaktas, O. Arikan and M. A. Kutay, “Digital Com-
putation of the Fractional Fourier Transform,” IEEE
Transactions on Signal Processing, Vol. 44, No. 9, 1996,
pp. 2141-2150. doi:10.1109/78.536672
[16] A. Bultheel and H. E. M. Sulbaran, “Computation of the
Fractional Fourier Transform,” Applied Computational
Harmonic Analysis, Vol. 16, No. 3, 2004, pp. 182-202.
doi:10.1016/j.acha.2004.02.001
Copyright © 2011 SciRes. IJCNS