American Journal of Operations Research
Vol. 2 No. 3 (2012) , Article ID: 22435 , 9 pages DOI:10.4236/ajor.2012.23046
Admission and Traffic Control Schemes Suitable for QoS Applications in WLAN Systems
1Nippon Institute of Technology, Saitama, Japan
2Doctoral Program in Graduate School of Electrical Engineering, Nippon Institute of Technology, Saitama, Japan
3NTT Access Network Service Systems Laboratories, Yokosuka, Japan
4Graduate School of Science & Technology, Niigata University, Niigata, Japan
Email: hira@nit.ac.jp
Received July 23, 2012; revised August 27, 2012; accepted September 7, 2012
Keywords: QoS; IEEE 802.11; Admission Control; Traffic Control; EDCA
ABSTRACT
This paper proposes the use of admission and traffic control schemes for real-time applications. The admission control scheme determines the admission of high-priority real-time applications such as voice and video streams in terms of their bandwidth utilization time (medium time), whereas the traffic control scheme maintains the communication quality of applications permitted admission by restricting other traffic. Owing to the use of contention-based access, a conventional scheme without admission control will degrade the communication quality when the number of terminals using high-priority applications increases. Moreover, only the capabilities (i.e., frame and sequence procedures) of admission control are defined in the IEEE 802.11e standard; the detailed usage in terms of the application characteristics is not specified, and it may be difficult to achieve a sufficient level of quality of service (QoS). The proposed schemes achieve the optimum QoS for actual services. The software used in the proposed schemes was implemented into hardware at the access point, and was evaluated experimentally. Based on the evaluation results, excellent performances with high QoS applications were obtained.
1. Introduction
Wireless local area network (WLAN) services providing Internet access have recently become ubiquitously available, such as in the home or office, on moving trains, and at transportation platforms and airports. In these types of environments, a variety of applications demanding realtime communication capability, such as voice and video streaming, have emerged for WLANs, in addition to traditional best-effort applications such as Web access and email, as shown in Figure 1. Therefore, WLAN services need to support both real-time and best-effort traffic with limited wireless bandwidth. For such a wide variety of applications, a wireless access control called an Enhanced Distributed Channel Access (EDCA) mechanism, as specified in the IEEE 802.11e standard [1], can prioritize and differentiate the quality of service (QoS) between real-time and best-effort traffic. For real-time traffic, it is desirable to ensure a stable QoS during the entire communication process. However, the quality of realtime traffic when using EDCA may be not ensured when the number of high-priority flows increases, as EDCA is based on contention access [2]. Therefore, even when using EDCA, when the bandwidth utilization is saturated, the quality of the communication will degrade if new flows start making connections. Hence, an admission control function is provided in the IEEE 802.11e standard. This admission control function decides whether to accept or reject a connection. If the QoS of a previously
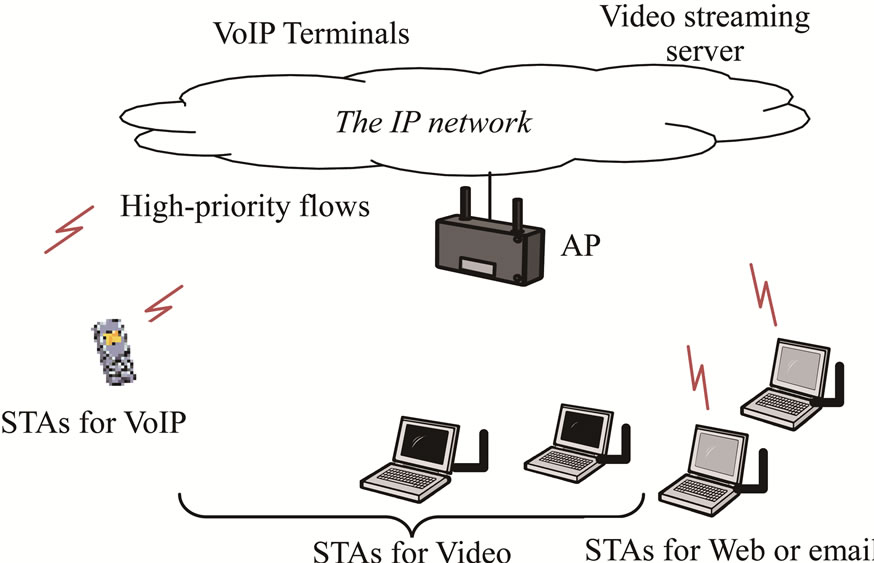
Figure 1. WLAN network scenarios.
established flow is degraded, it is reasonable to deny the flow and avoid further deterioration. Accordingly, an admission control that can determine whether the QoS of a flow is adequate before communication begins will be an effective means of guaranteeing the QoS for real-time traffic in EDCA. As another method for achieving a high QoS, a concentration control mechanism for contention-free access, called HCCA (HCF (Hybrid Coordinator function) controlled channel access), has been employed. HCCA enables a parameterized QoS using schedulingbased access control schemes based on a negotiated QoS policy. Using HCCA mechanisms, WLANs provide a link within an end-to-end QoS environment, as this mechanism completely controls the wireless bandwidth by scheduling the most suitable application, unlike priority control using EDCA. In recent years, research on the use of the HCCA mechanism has been intense ([4-8] etc.). However, since only EDCA is recognized in Wi-Fi WMM, commercially available WLAN devices support only the EDCA mechanism. Furthermore, millions of legacy WLAN devices with no EDCA mechanism remain in use. Considering the service requirements of WLAN systems, it is important to provide an assured level of communication quality to common WLAN devices. Therefore, this study focuses on admission control using EDCA.
In a conventional admission control scheme, a TSPEC (Traffic Specification) negotiation, the sequence procedure and frame information of which are defined in the IEEE 802.11e standard, is prepared to negotiate the QoS policy between the Access Point (AP) and the Stations (STAs). The AP checks the information regarding the communication quality from the STAs using the TSPEC procedure, and then makes an admission determination before beginning a high-priority communication. This procedure allows the AP to determine whether a communication will meet the quality guarantee before the communication begins, which should be effective for maintaining the communication quality of real-time applications. Nevertheless, the method for generating an admission decision at the AP is dependent on the implementation; however, there is no clear index on how to decide on such an admission. Therefore, only frame information items and the sequence procedure are defined in the standard. In addition, if the STAs generate heavy traffic beyond what is permitted by the AP, thus occupying the wireless bandwidth, the QoS of a high-priority flow that has already been accepted may deteriorate. For this reason, in addition to an admission decision method, to maintain the communication quality, a traffic control method that takes into account the promised amount based on a TSPEC negotiation is required at the AP. These detailed issues are described in the next chapter.
In this paper, we propose an admission control scheme for EDCA that employs a TSPEC negotiation, and a traffic control scheme that takes into account the previously admitted flow amount for the purpose of maintaining the QoS of real-time flows. These proposed schemes will improve the issues of a conventional admission control scheme and achieve the optimum QoS for actual services. The proposed schemes are introduced in Section 3. The results of an experimental evaluation of these schemes are then reported and discussed in Sections 4. Finally, Section 5 provides some concluding remarks regarding the proposed schemes.
2. Conventional Admission Control and Issues
The conventional TSPEC negotiation procedure for admission control is shown in Figure 2. In the IEEE 802.11e standard, an AP and STAs supporting the QoS are called a QAP and QSTAs, respectively. QAP sets the ACM (Admission Control Mandatory) flag in the beacon frame according to the priority for the admission control as a means of informing all STAs that a TSPEC negotiation is supported in this QAP. The beacon frames containing an ACM flag are periodically broadcasted from the QAP. The QSTAs set the parameters of the quality policy for the TSPEC parameters required by the application (see Table 1 for an example), and then send these parameters in an ADDTS (ADD Traffic Stream) Request frame to the QAP. The QAP uses this information in the ADDTS Request to make an admission decision, and then sends the decision result to the QSTA in an ADDTS Response frame. If the decision result from the QAP is to accept the flow, the QSTA begins a high-priority communication through a data exchange. If the high-priority communication ends, a QSAT or QAP sends a DELTS (Delete Traffic Stream) frame, and the QSTA ends all sequences of the relative applications. The QSTA also sends an ADDTS Request frame to the QAP, and if the decision result from the QAP is to reject the flow, the QSTA cannot start a high-priority communication. Although a TSPEC negotiation is an admission procedure
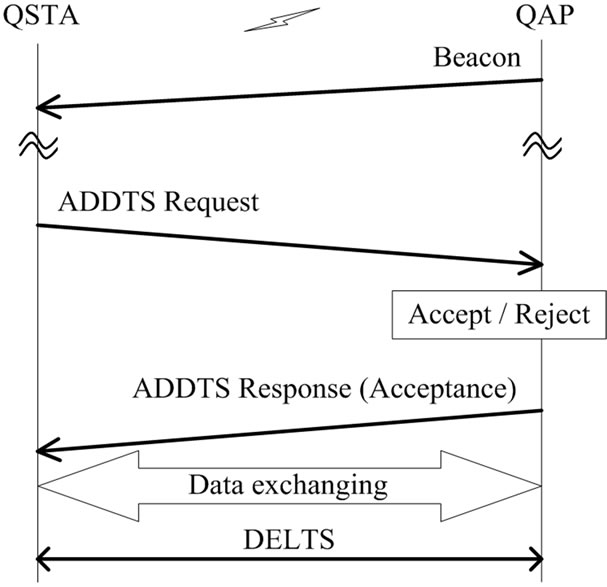
Figure 2. TSPEC negotiation.
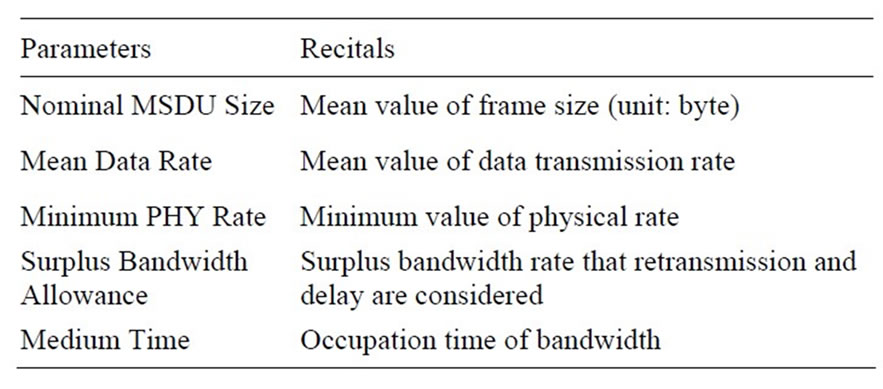
Table 1. Typical TSPEC parameters.
for high-priority communications in EDCA, a method for determining admission is dependent upon the implementation of the QAP [9-12]. Thus, a specific method to determine the admission control is needed in actual QoS services.
Another issue is that, after the QSTA acquires admission through these procedures, the admitted traffic amount may be exceeded since EDCA is based upon contention-based access. In addition, since a WLAN does not have a way to ascertain whether a terminal is trustworthy, a QSTA may exceed the promised traffic amount if the QSTA sending the ADDTS request frame is an untrustworthy terminal or a malevolent user. Moreover, since low-priority traffic, such as best-effort traffic, remains outside the admission control, such traffic is not managed and the wireless bandwidth may be saturated. Consequently, some such flows occupying the wireless bandwidth may degrade the QoS of other high-priority flows that have already been admitted [13-16]. To address these issues and maintain the quality of the communication, in addition to a concrete admission decision method, a traffic control method that takes into account the promised traffic amount based on a TSPEC negotiation will be a significant technique for use at an AP.
3. Proposed Scheme for Addition Control and Traffic Control
In this chapter, we describe the two proposed schemes in greater detail. As the first proposal, specific admission control based on a conventional scheme is introduced in Section 3.1. This scheme may achieve a proper admission decision for high-priority applications when considering the bandwidth utilization time. Next, the traffic control scheme is introduced in Section 3.2. This scheme can maintain the communication quality for previously permitted admissions by restricting other traffic. This traffic control scheme is performed in conjunction with the admission control scheme.
3.1. Proposed Admission Control Scheme
A flow chart of the proposed admission control is shown in Figure 3. The QAP compares the occupancy bandwidth (time) requested from an initiated application flow
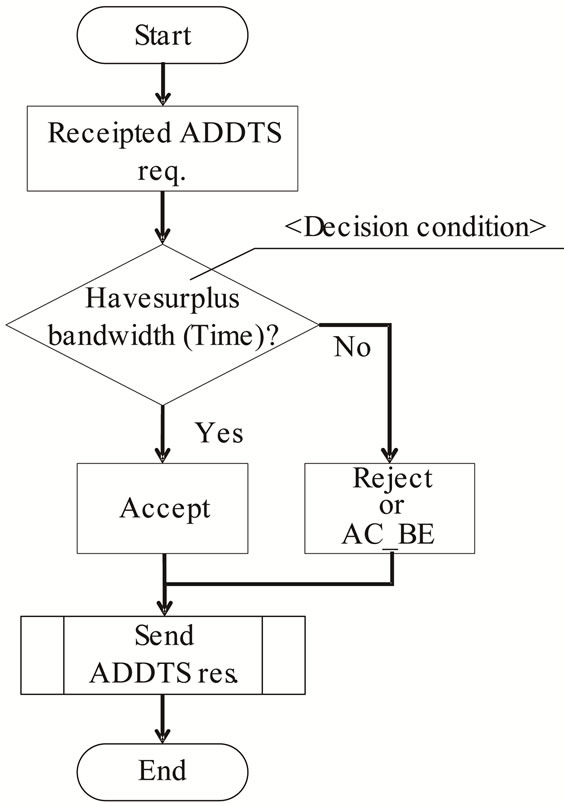
Figure 3. Flow chart of proposed admission decision in AP.
in the ADDTS Request with the surplus time calculated from the summation of the occupancy times of the previous flows that were already admitted. The QAP decides to admit the initiated application flow if the occupancy time of this flow is less than the surplus time. When the QAP decides to reject the admission request, it can choose to either deny the request altogether or switch it to a low-priority communication. In this paper, we choose the latter option owing to an efficient use of bandwidth and to respect the discretion of the user. Moreover, the user is able to abandon the communication if dissatisfied with the low priority.
The details of the QAP admission decision algorithm are given below. When the QAP receives an ADDTS Request, the AP calculates the Medium Time (MT) [17] to estimate the occupancy bandwidth time of the initiated flow, TMT_init, in the following way,
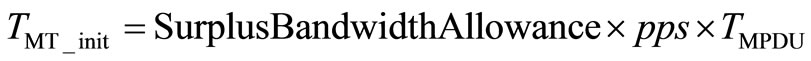 , (1)
, (1)
 ,(2)
,(2)
 . (3)
. (3)
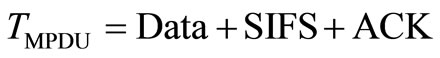
In Equation (1), “pps” and “TMPDU” are derived from Equations (2)-(3), respectively. “pps” is the number of packets per sec, and “TMPDU” is the exchange time of the data and ACK (Acknowledgment) frames including the frame header. Surplus Bandwidth Allowance, Mean Data Rate, and Nominal MSDU Size are found in the TSPEC parameters (See Table 1). The QAP continuously manages the total bandwidth occupancy time used by the previously admitted flow, Tused. When the number of admitted flows consists of N and M in AC_VO and AC_VI, respectively, the total occupancy time, Tused, is given by Equation (4) below. AC_VO and AC_VI indicate the types of voice and video applications (high priority applications) [18,19],
 . (4)
. (4)
 , (5)
, (5)
or
 . (6)
. (6)
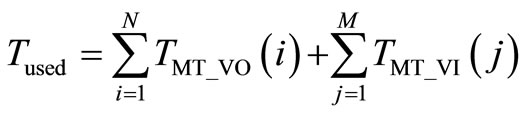
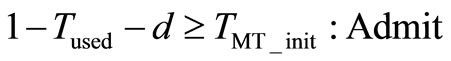
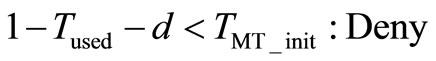
Here, the i and j indexes are the previous flow numbers admitted in AC_VO and AC_VI by the admission control, and TMT_VO(i) and TMT_VI(j) represent the bandwidth occupancy time of flow (i, j) from Equation (1), respectively. In this case, the surplus bandwidth is “1-Tused,” and the QAP compares the flow occupancy time of Equation (1), TMT_init, with that in Equation (5) or (6) to make an admission decision. d is the margin in consideration of the traffic fluctuation. The AC_VO and AC_VI flow retransmissions, as well as the bandwidth allocated to the AC_BE and AC_BK flows (for best-effort applications with low priority), are taken into account. Accordingly, from (5) and (6), the decision can be expressed as follows:
 , (7)
, (7)
or
 , (8)
, (8)
Equations (7) and (8) show that the QAP admits an initiated flow if the summation of the occupancy time of the new flow (TMT_init) and the occupancy time of the previously admitted flow (Tused) is within the upper limit as expressed by (1 – d). If not, the admission is denied.
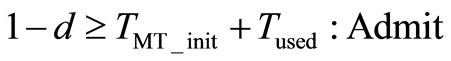
A model diagram of the proposed admission control scheme is shown in Figure 4, where the solid line indicates the maximum occupancy time allowed for both AC_VO and AC_VI flows. The proposed scheme rejects an admission in the region above the straight line (1 – d), which represents the maximum values of the summation of the occupancy time of the initiated flow (TMT_initi) and
Figure 4. Diagram of proposed admission control scheme.
the total occupancy time given to the existing flow (Tused), as expressed by Equations (7)-(8). In the scheme proposed above, a QAP admission decision is based on a comparison of the occupancy time calculated from the TSPEC parameters with the surplus bandwidth. If an admission is rejected, the communication quality of the existing flow may be maintained by changing the initiated flow from high priority to low priority.
3.2. Proposed Traffic Control Schemes
For a high-priority communication, it is desirable that a stable communication quality be maintained from beginning to end. To achieve a stable communication quality for previously admitted flows by the QAP, two traffic control schemes with specific purposes are proposed. For the first purpose, a high-priority traffic control scheme prevents high-priority traffic accepted by the admission control from exceeding its permitted amount. For the second purpose, a low-priority traffic control scheme will prevent low-priority traffic from degrading the communication quality of high-priority traffic by occupying the bandwidth. An example of a three-step high-priority traffic control scheme is shown in Figure 5. As the first step, the QAP observes high-priority traffic flows. Next, when an excessive amount of traffic is continuously passed to the QAP over a certain period of time, Texcess, high-priority traffic flows are restricted based on the excess amount by discarding packets. Finally, if an excessive amount of traffic continues for a certain period of time, Tdiscard, a disassociation message is sent to the STA to force a disconnection. If the amount of observed traffic is restored to the permitted level, the QAP state switches back to the observation phase in the first step. This control method can prevent high-priority traffic from exceeding the permissible amount and occupying the wireless media, degrading the communication quality.
Also for the second purpose described above, a lowpriority traffic control scheme will prevent previously admitted high-priority flows from being suppressed by heavy low-priority traffic. An example of low-priority
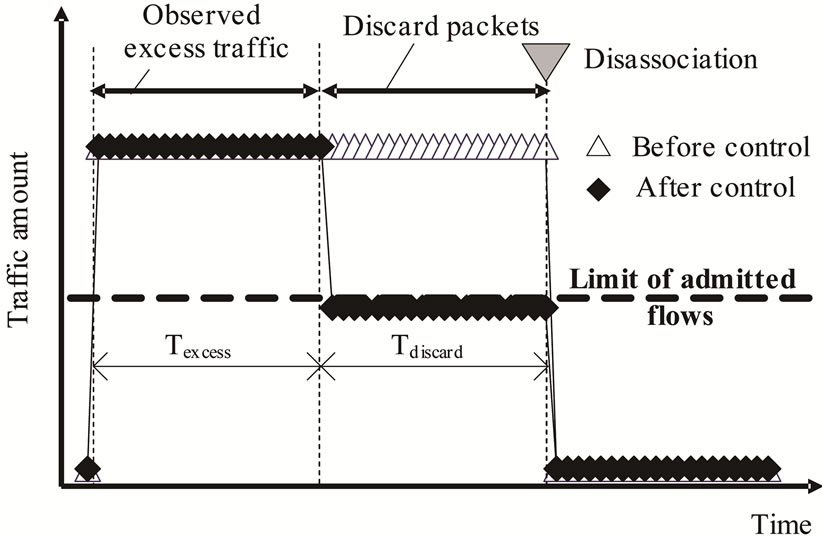
Figure 5. High-Priority traffic control.
traffic behavior monitored by an AP is shown in Figure 6. Without the control shown on the left side of Figure 6, the high-priority traffic is suppressed by low-priority traffic when using the admission control scheme, regardless of the admitted amount, if the amount of low-priority traffic, such as best-effort traffic, is heavy. The results of the proposed control scheme are shown on the right side of Figure 6. The QAP discards packets from low-priority traffic, if such traffic uses up the permitted amount of bandwidth. This scheme suppresses the amount of lowpriority traffic to within a range that allows the highpriority traffic to be transmitted up to the permitted amount, thus maintaining the communication quality of the high-priority traffic.
4. Experimental Evaluation
In this section, an AP implemented using the proposed admission and traffic control schemes is evaluated based on experimental results. First, Section 4.1 describes the results of the admission control. Next, Section 4.2 describes the results from the traffic control. Each sub-section explains the experimental configurations and traffic conditions for each scheme. We also present the quality of the targets. The evaluation results are also shown.
4.1. Evaluation of Admission Control Scheme
The experimental configuration used for the admission control scheme is shown in Figure 7. Table 2 lists the traffic conditions used in this configuration. The link rate of the WLAN was fixed to 11 Mbps (IEEE 802.11b std.) to simplify the experiment. Using five active voice QSTAs, the average delay time and packet loss were measured for
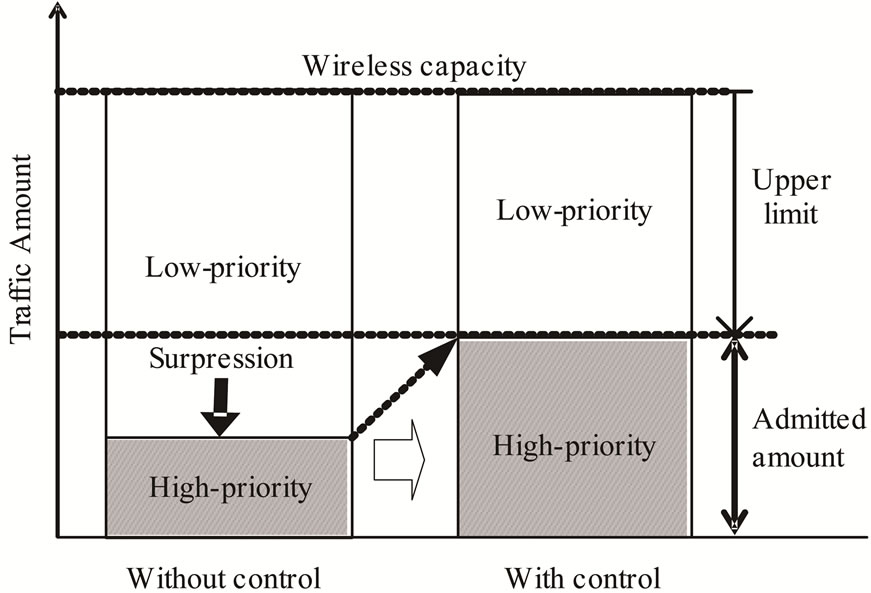
Figure 6. Low-priority traffic control.
each voice and video QSTA when increasing the number of video QSTAs. The voice traffic was bidirectional (uplink and downlink), and the video traffic was one-way (downlink). To recreate the network congestion during the experiment, one QSTA generated a bidirectional traffic load (uplink and downlink) by best-effort (AC_BE). Therefore, a load QSTA occupied wireless media owing to the existence of best-effort traffic. When the proposed admission control was used, the video priority was set to AC_BE (best-effort), and when the video flows above the admission volume were denied admission, the QAP sent an ADDTS res. to the QSTA.
As quality performance targets, we set the upper limit of the quality performance to a delay of 50 ms for voice and 400 ms for video, with a packet loss of 1 × 10−3 for both voice and video by referring to [3]. These conditions were confirmed to achieve good communication quality.
In an uplink (UL) and downlink (DL), the average delay time and packet loss for the voice and video QSTAs for five active voice QSTAs are shown in Figures 8 and 9. Both figures show the results with and without the use of the proposed admission control scheme.
Without admission control (w/o AC), the downlink delay of the voice QSTA exceeds the upper limit when three video QSTAs are connected, as shown in Figure 8. The downlink packet loss for the voice QSTA also exceeds the upper limit when three video QSTAs are connected, with a value of 10–3, as shown in Figure 9. Furthermore, although Figure 8 shows that the video QSTA delay is within the target performance range with three video QSTAs connected, the packet loss under the
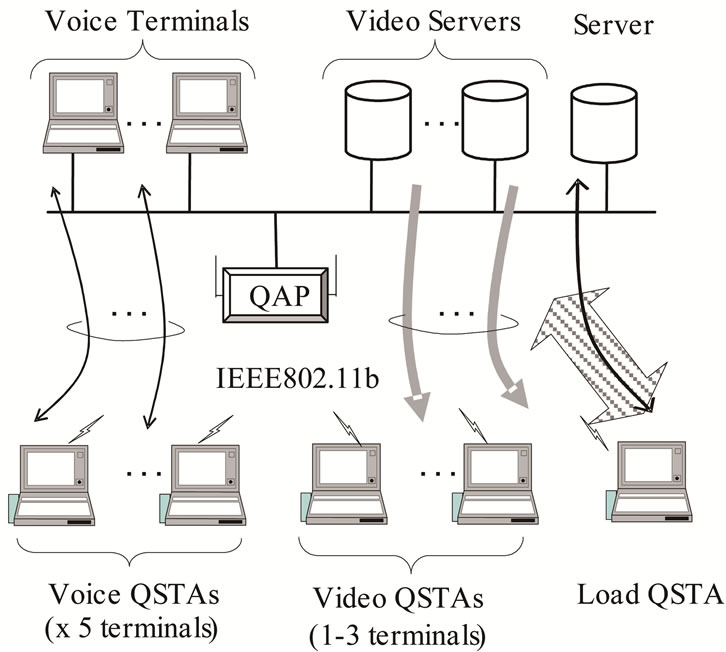
Figure 7. Experimental configuration for admission control scheme.
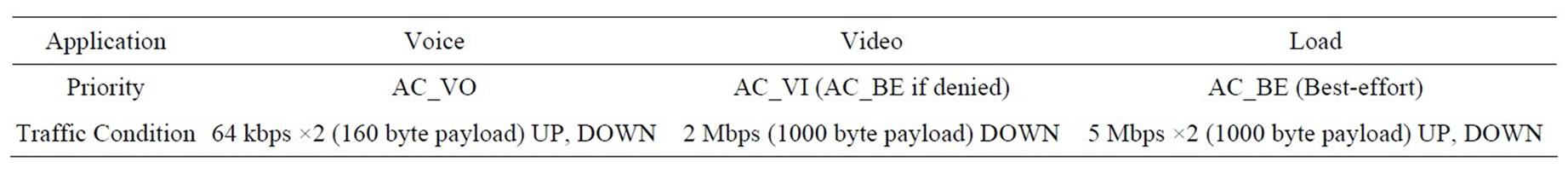
Table 2. Traffic conditions.
same conditions exceeds 10–3, as shown in Figure 9.
With admission control (w/AC), on the other hand, the voice QSTA downlink and video QSTA delay are suppressed to within the upper limit, as shown in Figure 8. In addition, the voice QSTA downlink and video QSTA packet loss are both within the target range, as shown in Figure 9. These results show that the proposed admission control can maintain the communication quality of the previously-admitted video and voice QSTAs by shifting to low-priority when the video QSTAs are denied.
The above results confirm that the communication quality of high-priority traffic can be maintained in EDCA by using the proposed schemes, which calculate the total high-priority occupancy time and shift the traffic to a low priority when admission is denied.
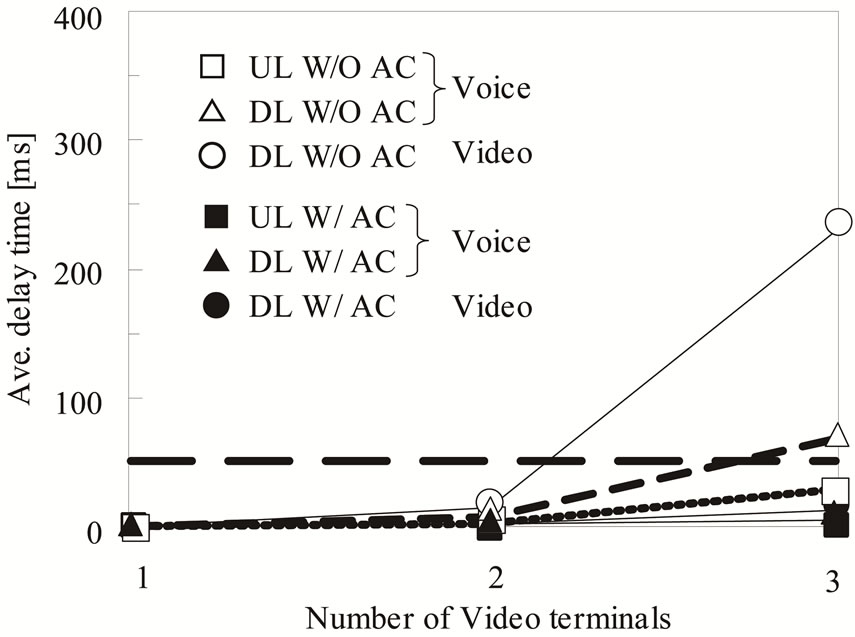
Figure 8. Average delay time w/ or w/o AC.
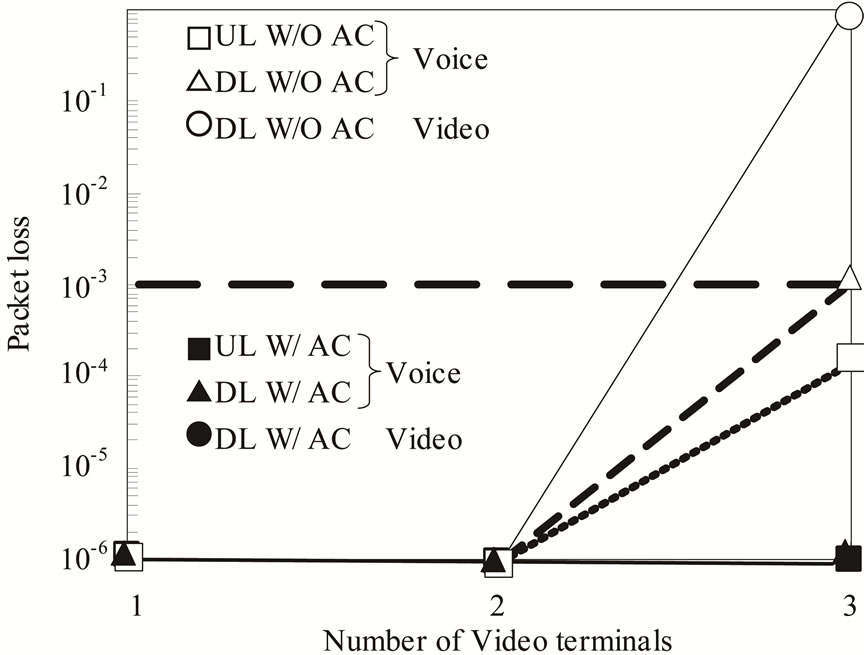
Figure 9. Packet loss w/ or w/o AC.
4.2. Evaluation of Traffic Control Scheme
The experimental configuration for high-priority traffic control is shown in Figure 10. In addition, Table 3 lists the traffic conditions of this configuration. The link rate of the WLAN was fixed to 11 Mbps (IEEE 802.11b std.) to simplify the experiment. One voice QSTA and one video QSTA were connected to a QAP. Bidirectional traffic (AC_VO) of the highest priority was generated by a load QSTA to occupy wireless media. We measured both the average delay time and packet loss for the voice and video QSTAs over time to test the ability of the control scheme to restore the communication quality after degradation occurs.
In the voice and video QSTAs, the delay time and packet loss in the high-priority traffic control scheme are presented as functions of time in Figures 11 and 12.
A solid line in the figures represents the upper limit for the voice QSTA delay shown in Figure 11. When the plot of the evaluation results is 10–3, it indicates that the packet loss is less than 10–3, as shown in Figure 12. At
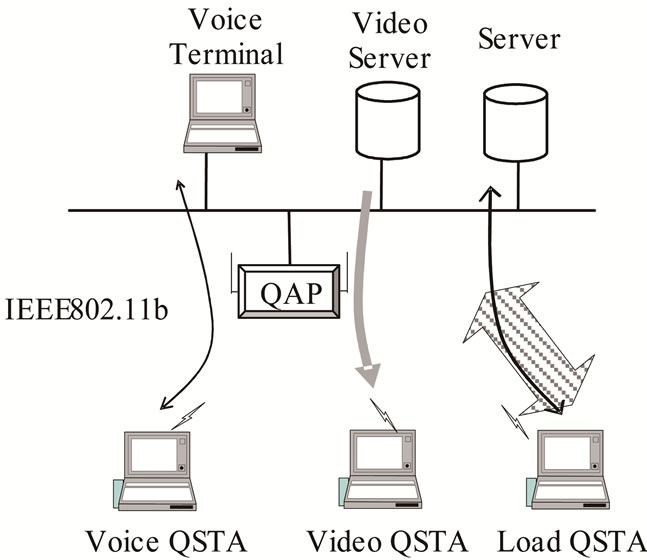
Figure 10. Experimental configuration for high-priority traffic control.
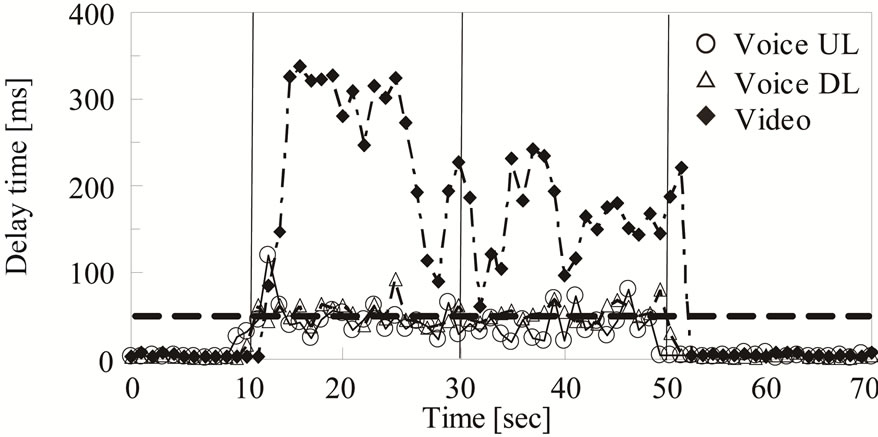
Figure 11. Delay time in high priority traffic control.
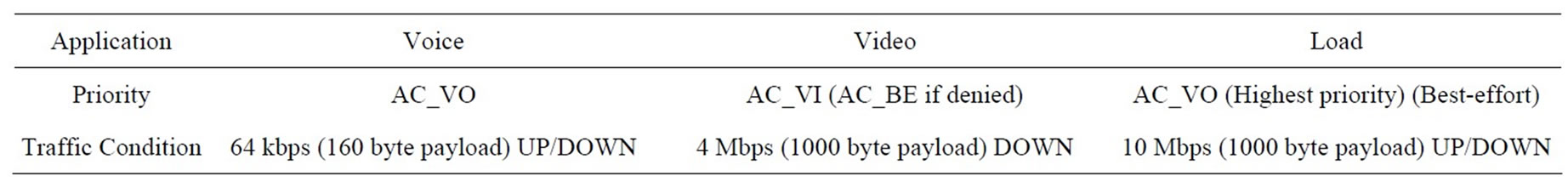
Table 3. Traffic conditions.
10 seconds after the observation began, the onset of load QSTA traffic was accompanied by an increase in the delay of the voice and video QSTAs. Furthermore, the video QSTA packet loss rose above 10–3. These results demonstrate that the excessive traffic generated by a load QSTA makes it impossible to preserve the communication quality of previously admitted voice and video QSTAs. When the QAP observes an excessive amount of traffic from a load QSTA, it discards packets from the load QSTA during a time interval of between 30 and 50 seconds after the beginning of the observation; the load QSTA is disconnected 50 seconds after beginning the monitoring. After 53 seconds, the voice and video QSTAs with the delay and packet loss are restored to their original quality.
These results show that the high-priority traffic control method can restore the communication quality of voice and video QSTAs by detecting and disconnecting excess traffic from a load QSTA. The delay and packet loss of the video QSTAs are restored to their original values two or three seconds after the 50-second mark, as shown in Figure 11, which can be attributed to the time required for the packet processing related to the load QSTA.
The results described above confirm that the high-priority traffic control scheme can preserve the communication quality of previously admitted high-priority traffic by preventing the occupation of wireless media.
The experimental configuration used for the low-priority traffic control is shown in Figure 13. In addition, Table 4 shows the traffic conditions used for this configuration. For this experiment, an IEEE 802.11g std. (link rate of 6 - 54 Mbps) WLAN is used. A video QSTA with UDP traffic is admitted with high priority (AC_VI),
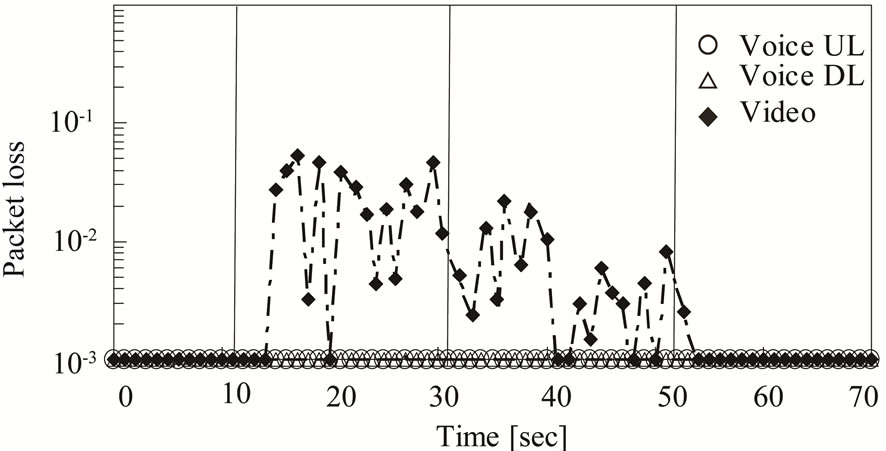
Figure 12. Packet loss in high priority traffic control.
and another load QSTA with TCP traffic for which the flow control is expected to be given low priority (AC_BE) is also admitted. To create a situation in which the lowpriority flow occupies wireless media, the wireless link rate of the load QSTA was set at 6 Mbps. Additionally, the video QSTA was set at 54 Mbps. The throughput characteristics of each QSTA were measured on the wired side as the amount of offered traffic with a video QSTA varied (2, 5 and 10 Mbps).
The throughput characteristics of a load QSTA and video QSTA are shown in Figure 14. When both video and load QSTAs exist without low-priority traffic control, the throughput is suppressed to about 3 Mbps, as the video QSTA of the offered traffic increases since the low-priority load QSTA occupies the wireless media, thereby decreasing the transmission opportunities for a high-priority video QSTA. The communication quality
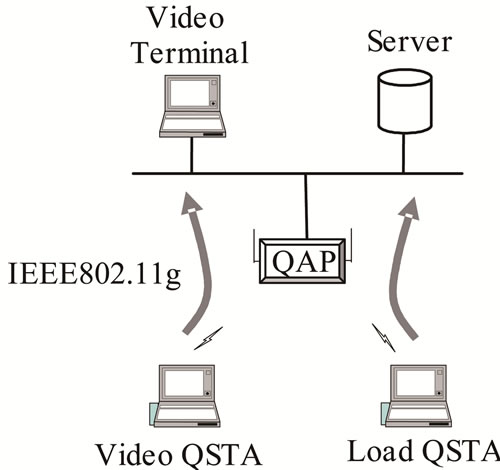
Figure 13. Experimental configuration for low-priority traffic control.
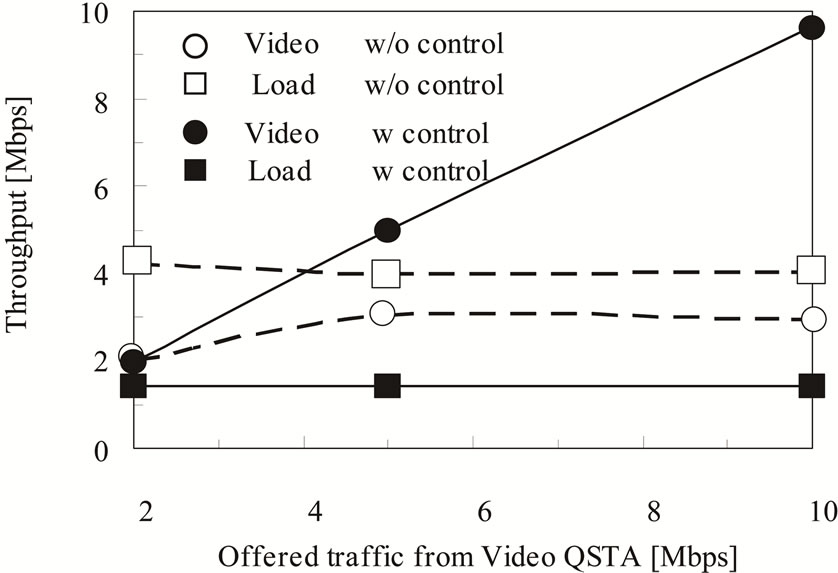
Figure 14. Throughput in low-priority traffic control.
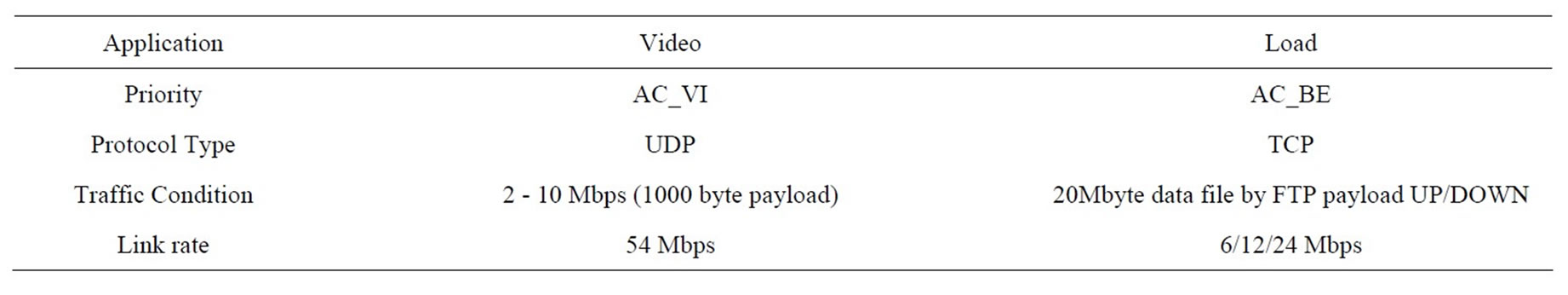
Table 4. Traffic conditions.
can therefore not be maintained despite a prior admission.
With low-priority traffic control, the video QSTA throughput increases as the offered traffic of the video QSTA increases, and thus the communication quality can be maintained. These results show that low-priority traffic control can prevent the occupation of wireless media by low-priority traffic, thus preserving the communication quality of high-priority traffic.
In addition, to clarify the effectiveness of the proposed scheme, the throughput of the video QSTA was measured for a load QSTA link rate of 6, 12 and 24 Mbps, and the video QSTA offered traffic of 2, 5 and 10 Mbps.
The throughput ratios of the video QSTA when varying the link rate of the load QSTA are shown in Figure 15. The throughput ratio is defined as the throughput without low-priority traffic control divided by the throughput with such control, where values of less than 1 indicate a greater control effect.
For an offered traffic of 2 Mbps from a video QSTA, the video QSTA throughput ratio remains at 1 even though the load QSTA link rate varies. This shows that the effect of the proposed scheme is slight since the video QSTA traffic is not affected by the load QSTA. When the amount of offered video QSTA traffic increases from 5 to 10 Mbps under various link rates of the load QSTA, the throughput ratio of the video QSTA decreases for smaller link rates and for a larger amount of offered traffic. These results show that the lower link rates of the load QSTA decrease the access opportunities for the video QSTA, and a larger amount of traffic for the video QSTA should achieve a higher throughput. Accordingly, the improvement from low-priority traffic control is evident under these conditions.
The results presented herein confirm that when the communication quality of previously admitted high-priority traffic is degraded by low-priority traffic occupying wireless media, the communication quality of the high-
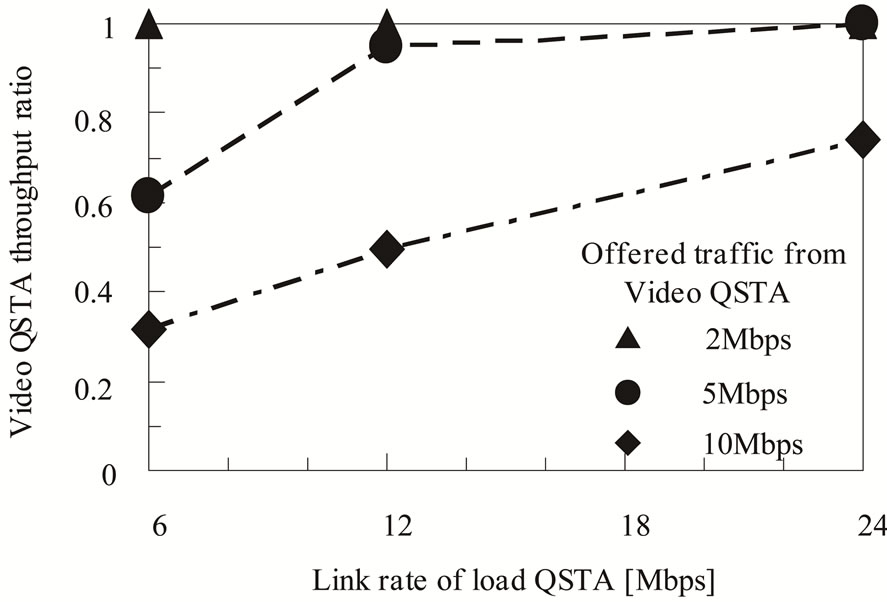
Figure 15. Throughput and link rate in low-priority traffic control.
priority traffic can be maintained by controlling the amount of low-priority traffic.
5. Conclusion
We proposed admission and traffic control schemes that preserve the communication quality of real-time traffic in EDCA. The admission control scheme employs a TSPEC negotiation procedure to generate an admission decision based on the total occupancy time of high-priority traffic. The traffic control scheme takes the amount of admitted traffic into consideration when controlling the amount of highand low-priority traffic to preserve the quality of high-priority traffic.
REFERENCES
- IEEE 802.11e, “Part 11: WLAN Medium Access Control (MAC) and Physical Layer (PHY) specifications: Amendment 8: Medium Access Control (MAC) Quality of Service Enhancements,” IEEE 802.11, 2005.
- A. Grilo, M. Macedo and M. Nunes, “A Scheduling Algorithm for QoS Support in IEEE 802.11e Networks,” IEEE Wireless Communications, Vol. 10, No. 3, 2003, pp. 36-43. Hdoi:10.1109/MWC.2003.1209594
- ITU-T Y.1541, “Network Performance Objectives for IP-Based Services,” May 2002.
- M. M. Rashid, E. Hossain and V. K. Bhargava, “HCCA Scheduler Design for Guaranteed QoS in IEEE 802.11e Based WLANs,” IEEE Wireless Communications and Networking Conference (WCNC 2007), 11-15 March 2007, pp. 1538-1543.
- M. M. Rashid, E. Hossain and V. K. Bhargava, “Queueing Analysis of 802.11e HCCA with Variable Bit Rate Traffic,” IEEE International Conference on Communications (ICC’06), Vol. 10, 2006, pp. 4792-4798.
- S. Hantrakoon and A. Phonphoem, “Priority Based HCCA for IEEE 802.11e,” 2010 International Conference on Communications and Mobile Computing (CMC), Vol. 3, Shenzhen, 12-14 April 2010, pp. 485-489. Hdoi:10.1109/CMC.2010.208
- D. y. Gao, J. f. Cai and C. W. Chen, “Admission Control Based on Rate-Variance Envelop for VBR Traffic Over IEEE 802.11e HCCA WLANs,” IEEE Transactions on Vehicular Technology, Vol. 57, No. 3, 2007, pp. 1778- 1788.
- D. y. Gao, J. f. Cai and K. N. Ngan, “Admission Control in IEEE 802.11e Wireless LANs,” IEEE Network, Vol. 19, No. 4, 2005, pp. 6-13. Hdoi:10.1109/MNET.2005.1470677
- C.-T. Chou, S. N. Shankar and K. G. Shin, “Achieving Per-Stream QoS with Distributed Airtime Allocation and Admission Control in IEEE 802.11e Wireless LAN,” Proceedings of IEEE 24th Annual Joint Conference of the IEEE Computer and Communications Societies (INFOCOM 2005), Vol. 3, 13-17 March 2005, pp. 1584-1595.
- C.-L. Chen, “IEEE 802.11e EDCA QoS Provisioning with Dynamic Fuzzy Control and Cross-Layer Interface,” Proceedings of 16th International Conference on Computer Communications and Networks (ICCCN 2007), Honolulu, 13-16 August 2007, pp. 766-771.
- K.-H. Lee, H.-J. Lee and J.-H. Kim, “An Active Buffer Management Based on the Virtual Transmission Delay for Video Streaming Service,” Military Communications Conference (MILCOM 2011), Baltimore, 7-10 November 2011, pp. 816-821.
- H.-J. Lee and J.-H. Kim, “An Optimal CF-Poll Piggyback Scheme in IEEE 802.11e HCCA,” The 8th International Conference on Advanced Communication Technology (ICACT 2006), Vol. 3, Phoenix Park, 20-22 February 2006, p. 1959.
- A. Andreadis, G. Benelli and R. Zambon, “An Admission Control Algorithm for QoS Provisioning in IEEE 802.11e EDCA,” 3rd International Symposium on Wireless Pervasive Computing (ISWPC 2008), Santorini, 7-9 May 2008, pp. 298-302.
- F. Cacace, G. Iannello, M. Vellucci and L. Vollero, “A Reactive Approach to QoS Provisioning in IEEE 802.11e WLANs,” Next Generation Internet Networks (NGI 2008), Krakow, 28-30 April 2008, pp. 253-260.
- B. Bensaou, Z.-N. Kong and D. H. K. Tsang, “A Measurement-Assisted, Model-Based Admission Control Algorithm for IEEE 802.11e,” International Symposium on Parallel Architectures, Algorithms, and Networks (ISPAN 2008), Sydney, 7-9 May 2008, pp. 260-265.
- I. Inan, F. Keceli and E. Ayanoglu, “Multimedia Capacity Analysis of the IEEE 802.11e Contention-Based Infrastructure Basic Service Set,” IEEE Global Telecommunications Conference (IEEE GLOBECOM 2008), New Orleans, 30 November-4 December 2008, pp. 1-6.
- Y. W. Pei, J.-J. Chen, Y.-C. Tseng and H. Weilee, “Design of QoS and Admission Control for VoIP Services Over IEEE 802.11e WLANs,” Journal of Information Science and Engineering, Vol. 24, 2008, pp. 1003-1022.
- K. A. Meerja and A. Shami, “Analysis of Enhanced Collision Avoidance Scheme Proposed for IEEE 802.11eEnhanced Distributed Channel Access Protocol,” IEEE Transactions on Mobile Computing, Vol. 8, No. 10, 2009, pp. 1353-1367. Hdoi:10.1109/TMC.2009.39
- W.-P. Lai, E.-C. Liou and W.-H. Fu, “Dispersive Video Frame Importance Driven Probabilistic Packet Mapping for 802.11e Based Video Transmission,” 2011 Third International Conference on Intelligent Networking and Collaborative Systems (INCoS), Fukuoka, 30 November-2 December 2011, pp. 424-429.

