International Journal of Communications, Network and System Sciences
Vol.10 No.08(2017), Article ID:78889,15 pages
10.4236/ijcns.2017.108B035
Leveraging 3D Benefits for Authentication
Jonathan Gurary1, Ye Zhu1, Huirong Fu2
1Department of Electrical and Computer Engineering, Cleveland, OH, USA
2Department of Computer Science, Oakland University, Oakland, MI, USA




Received: August 22, 2017; Accepted: September 1, 2017; Published: September 4, 2017
ABSTRACT
Devices with 3D capabilities are quickly gaining in popularity. In this paper, we propose to bring authentication into the third dimension. We define the concept of a 3D authentication scheme based on physical and psychological advantages of 3D. We implement an example of 3D authentication: 3DPass, to demonstrate the superiority of the 3D approach. Our security analysis of 3DPass demonstrates that 3DPass can exceed the password space of an 8 character alphanumeric password with just 6 choices. Our user study finds that 3DPass has superior memorability versus traditional alphanumeric passwords: 98% vs 83% recall rates after one week. We find that passwords in our scheme can be entered in 21 seconds on average when used with the Oculus Rift. We find that using the Oculus Rift improves entry time compared to a traditional 2D display, despite having no impact on presence (the feeling of “being there”) or user preference.
Keywords:
Authentication, Virtual Reality, 3D

1. Introduction
Virtual Reality (VR) and other 3D technologies are a burgeoning market that is rapidly expanding to applications in medicine, entertainment, education, and many other fields. This paper seeks to apply 3D technology to device authentication, both as a method for replacing traditional approaches such as the alphanumeric password on existing systems and for securing virtual reality resources in the future.
Authentication is the process of determining if a user should be allowed to access a device or resource, a central problem in computer security. Authentication schemes should be secured, that is, able to generate a large number of passwords which are not easy to guess or predict. Passwords generated by the scheme must be usable, that is, the user can input passwords with minimal time and effort. Passwords must also be memorable, even over long periods of time or when multiple passwords are used at the same time. The inadequacy of traditional passwords to meet these criteria is well documented [1] [2].
The 3D authentication scheme presents a new paradigm for authentication. To date, passwords have been based on the user’s knowledge of facts, information, or secrets. A traditional password asks users: what do you know? A 3D authentication scheme asks users to reproduce an experience inside a 3D environment. We call a password generated by a 3D authentication scheme a 3D password. If a traditional password is based on what you know, a 3D password is based on what you experienced.
The 3D authentication scheme is designed to leverage 3D advantages to achieve superior security, memorability, and usability. Any 3D display capable device, even a simple display like a mobile phone or monitor screen, can support a 3D authentication scheme. However, we anticipate that 3D authentication will perform better when used with 3D technologies such as HMDs and naked eye 3D, especially as users grow familiar with these devices.
We envision several potential applications for 3D Authentication:
1) Protecting virtual resources in a virtual environment. For example, some portion of an environment is restricted until authentication is finished, or a file is protected by a 3D password. The user is already on a 3D capable device, and is probably already familiar with the input mechanism.
2) As a high security option for traditional PC authentication. 3D Authentication can yield a massive password space, allowing users to create very secure and simultaneously memorable passwords.
3) As a mobile authentication method. The soft keyboard available on most mobile devices is slow and typo-prone, rendering alphanumeric passwords impractical. Most recently released mobile phones are already capable of basic 3D rendering and some devices feature enhanced 3D options like naked-eye 3D and support for Google Cardboard. Mobile devices have various input methods built in, such as the touchscreen and gyroscope, and many manufacturers also sell portable controllers for mobile devices similar to the controller used in this paper.
In this paper, we define the physical and psychological advantages of 3D authentication. We introduce a 3D authentication scheme, dubbed 3DPass, which utilizes these advantages, and present several design considerations to further improve memorability and usability. Our security analysis finds that 3DPass is more secure than alphanumeric passwords in terms of password space. We conduct a user study to explore 3DPass in terms of usability, memorability, user preference, presence, hotspots, and the impact of HMD technology on some of these factors.
2. Related Work
Graphical passwords, originally introduced by Blonder [3] leverage the picture superiority effect [4]―the concept that visual data is easier to remember and recognize than letters or words―for superior memorability and usability.
Many recent works in graphical authentication, such as SwiPIN [5], The Phone Lock [6], and ColorPIN [7] seek to reduce the risk of shoulder-surfing attacks, in which the attacker steals a user’s password by observing the device as the user enters the password. A 3Dpassword entered using an HMD is natively immune to shoulder-surfing observers, since the display is completely hidden inside the HMD.
To the best of our knowledge, the first prior work regarding 3D authentication is the work by Alsulaiman and Saddik [8]. Alsulaiman and Saddik define 3D authentication as a series of interactions with the virtual world, for example typing a password at a virtual terminal, entering a graphical password (as in [9]), presenting a biometric token within the virtual world, or moving a book from one place to another. This work makes several additional enhancements and contributions: 1) Our design is uniquely based on psychological and physical advantages available to 3D technologies. We describe these advantages and demonstrate how a scheme based in a 3d world can leverage these elements to its advantage; 2) Our design directly integrates moving and navigation as a part of the authentication process. Using navigation increases the size of the password space and allows for a unique opportunity to utilize spatial memory for authentication; and 3) Our design is memorability and usability focused, designed for broad application and not only security-critical systems. We build our implementation while keeping in mind potential future applications such as mobile authentication.
3. Background of the 3D Authentication Scheme
Memorability and usability advantages of the 3D authentication scheme are founded in various physical and psychological phenomena, described below:
Presence: Presence is considered the psychological sense of “being in” a virtual environment [10]. It is often considered the key of virtual reality [11]. Slater et al. [12] conclude that while there is no reason to expect presence to improve performance on its own, “presence is concerned with how well a person’s behavior in the virtual environment matches their behaviors in similar circumstances in real life”. We hypothesize that users will experience improved usability, such as better entry times, with common real life tasks when presence is improved. In other words, 3D authentication can leverage presence to improve performance.
Spatial Memory: Research demonstrates that spatial memory, used to navigate the environment and remember where things are, is neurologically distinct from other types of memory like object recognition and factual recall [13]. Attree et al. [14] find that active participants in VR navigation have improved memory for the spatial layout of the environment. A 3D authentication scheme that utilizes active participation in navigation effectively taps into human spatial memory for authentication purposes.
Episodic Memory: Tulving [15] breaks memory into two categories: autobiographical memory of experiences known as episodic memory, and fact-based, cognitive reference memory known as semantic memory.
Other authentication schemes rely on semantic memory; the user must recall some knowledge that they have stored. Rather than asking the user for information, a 3D password asks users to recreate an experience that they had earlier. In other words, rather than being based on what you know, a 3D password is based on what you experienced.
Context: People remember more information when they are asked to recall the information in the same environment where they learned it [16]. A 3D authentication scheme allows users the unique opportunity to return to the same environment where they first set their passwords every time they authenticate.
The 3D Password represents a new paradigm in how users remember their passwords. The use of spatial memory for navigation, episodic memory instead of semantic memory, and context, has never before been applied to authentication.
Stereo parallax: Because human eyes are several inches apart, each eye perceives a slightly different image. In displays, true stereo vision is available only in HMDs, where each eye is shown a different image. Glasses-enabled 3D displays and naked eye 3D displays can also take some advantage of stereo vision. Ijsselsteijn et al. [17] conclude that adding stereoscopic information to a display improves reported presence.
Head Tracking and Motion Parallax: Some displays, primarily HMDs, have the ability to move the on-screen image as the user moves their head. Far away objects appear to travel less distance than nearby objects when an image is moved due to turning of the head―a depth cue known as motion parallax.
Head tracking also allows users to target objects by turning towards them.
Hendrix et al. [18] find that the reported level of presence is significantly higher when stereoscopy and head tracking are provided. Barfield et al. [19] find that users performed wire-tracing tasks faster when stereo vision was added and with fewer errors when head tracking was added.
We hypothesize that physical advantages of VR will lead to increased presence ratings and better entry times vs a traditional display. Tavanti and Lind [20] found that merely adding 3D depth cues, such as shading and perspective, to an otherwise 2D scheme can improve memory performance.
4. Implementation of 3DPass
3DPass places the participant’s avatar at the entrance to a virtual home. Figure 1(a) shows a top-down view of our environment. Users can walk around the environment and interact with most objects around the house.
Small items such as books, fruit, or soap can be picked up and carried around, gently dropped, or thrown. Stationary items, such as the stove and fireplace, can be interacted with. The stove can be ignited and turned up or down, sinks and bathtubs have running water, and televisions can be turned on or off and flipped to one of four channels. Lights around the house can be turned on or off. Doors, drawers, and cabinets can be opened or closed with precision.


Figure 1. (a) Overhead view of 3DPass taken in unity (roof removed). (b) Teleporter room. Walking into a cube instantly takes the user to the corresponding area.
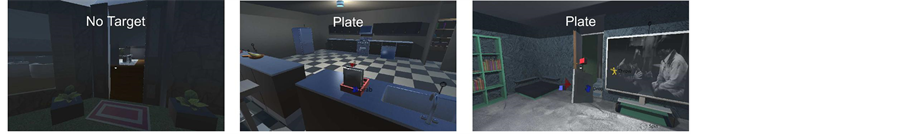
Figure 2 shows several examples of the 3DPass system. In order to keep immersion, the GUI of 3DPass is kept minimalistic. A dot in the center of the screen helps the user to target objects by aligning the dot with the object. The object must be within “arm’s reach” of the player avatar to be targeted. Small black lines with a circle on top indicate an object can be interacted with. Red triangles indicate the object is currently targeted, and the name of the currently targeted object is displayed at the top. A context menu appears when an object is targeted showing the user what actions can be taken. The colors and locations of the context menu correspond to colors and locations of buttons on the Xbox 360 controller. Held objects are carried in front of the avatar until dropped or thrown. No other objects can be targeted while an object is already held. When rotating an object, colored cubes appear to assist the user in determining what direction they are rotating in.
Users generate a 3D password by performing a set of actions and navigations. Figure 2 can be considered an example 3D password. The user enters the kitchen and turns on the lights. Next the user goes to the children’s bedroom and turns on the lights and television. The user returns to pick up a plate from the kitchen and takes it to the children’s bedroom. The user stands by the couch in
Figure 2. Screenshots of the 3DPass application. (left) The entrance to the home, where users start. (center) The kitchen. The user has turned on the lights, and is now targeting a plate to pick it up. (right) The children’s bedroom. User has turned on the television and lights and is rotating the held plate.
front of the TV and rotates the plate until it the angle looks like it matches the door to the left of the TV.
Users authenticate themselves later by repeating set actions and navigations exactly, within some tolerance for distances and angles.
4.1. Input Device
Participants interact with 3DPass using an Xbox 360 controller.
Isokoski and Martin [21] find that the controller performs on the same level as a keyboard + mouse + eye tracker combination at aiming tasks. Davidson [22] finds that the controller performs better than gesture tracking technologies such as the Kinect and on par or better than mouse and keyboard in terms of user enjoyment, mental and physical fatigue incurred, and overall ease of use. Coelho and Verbeek [23] found that the Leap Motion is slower than mouse and keyboard for various simple input tasks, so by extension technologies like the Leap Motion will likely be slower than the controller.
HMD users of 3DPass are also able to use head tracking, allowing them to aim at objects with their heads rather than using the analog sticks. We hypothesize that the combination of a controller for movement and interaction tasks and an HMD for aiming tasks will result in low entry times.
We plan to create a mobile version of 3DPass in our future work. Mobile users can potentially use their phone as the display, for example with a holding device such as Google Cardboard, while using a bluetooth-based controller for input.
4.2. Design Considerations
3DPass utilizes the psychological and physical advantages described in Section 3 while maintaining high usability by adhering to several additional design considerations:
1) Familiar Environment: Since this scheme is targeted at the general population, a home is used as the environment. We selected the best selling building plan from a popular house plans vendor as the basis for our design. A familiar environment allows for faster learning as participants already know what can be expected inside. For example, participants know that in a house, there is a bathroom, with a sink that can be turned on and filled with water. We expect that matching user expectations can improve presence and facilitate faster learning of the environment for navigation.
2) Multiple Contexts: 3DPass is split into rooms which have distinctly colored walls, distinctly patterned floors, and other distinguishing features. 3D passwords generated in different contexts may suffer less memory interference.
3) Quickly Navigable: 3DPass accomplishes this in three ways: 1) the environment itself is relatively compact, and can be walked across in about 15 seconds. All doors are open by default; 2) Users are able to engage a “speed walk” function by holding a button as they walk, allowing them to pass through any solid object (including walls) and move extremely quickly. The environment can be crossed in about 3 seconds using this function; and 3) Users can press a button to be transported to the “teleporter room”, demonstrated in Figure 1(b), a separate area where all major rooms in the environment are available for fast access.
5. Security Strength of 3D Authentication
We denote the number of objects in the environment which can be picked up and held as N. The number of modifications that can be made to a currently held object, for example rotating it to an angle or stretching it, will be denoted as M. For simplicity we will say M is the same for every object which can be held. We will denote the number of locations a held object can be placed as L, where the size of L is the usable area of the environment divided by some tolerance value. The number of interactions the user can have with objects that does not require picking them up, for example typing a key, turning on a light, or setting a toaster, will be denoted as Ninteractable*IN, where Ninteractable is the number of interactable objects in the environment, and IN is the number of interactions for each of those objects. Some objects in Ninteractable may also be in N. Lastly, we denote that the number of locations the user’s avatar can move to as Lnavigable. The size of Lnavigable will be smaller than L, as there will be locations where objects can reach but the user’s avatar cannot travel, for example inside a drawer.
At any point, the user has the following choices: 1) Grab one of N objects; 2) If an object is held, modify the object in one of M ways; 3) If an object is held, put it in a new location in L; 4) Perform one of IN interactions on one of Ninteractable objects; 5) Navigate to a location in Lnavigable.
For simplicity, assume that if the user is already holding an object, they can still pick up another, and that the user is holding an object on startup. If T is length of the password in choices, the password space is then equal to:
(N + M + L + (Ninteractable*IN) + Lnavigable)T (1)
Equation (1) is an upper bound, as we assume that users can pick up objects even when they are already holding one, and that users can modify or relocate objects they haven’t yet picked up. If we assume that the user cannot pick up or interact with a new item while already holding one, then in practice, the user has
M + L + Lnavigable (2)
choices when holding an item. When not holding an item, the equation becomes:
N + Ninteractable*IN + Lnavigable (3)
Security Strength of 3DPass
There are 327 moveable objects (N = 327) and 115 interactable objects (Ninteractable = 115) that cannot be picked up in 3DPass. For simplicity, we say IN = 1, though many objects in 3Dpass have much more than one interaction.
3DPass simulates approximately 3000 ft2 (roughly 279 m2) of indoor living space excluding walls, doors, and other natural barriers. For simplicity, we assume a generous tolerance of 3 ft2 (roughly 1 m2) for a lower bound of (L = 300). The navigable space is slightly lower than L due to furniture which the user’s avatar cannot climb on. We estimate Lnavigable is roughly 80% of L, so Lnavigable is roughly 240 as a lower bound.
Held objects can be modified by rotating them. Rotation was used by only 16% of participants in the user study, and no other modifications for held objects are available, so we set M = 0 for fairness.
The password space of 3DPass, according to Equations (1) and (3), is plotted in Figure 3. Equation (1) represents an upper bound for 3D authentication schemes, while Equation (3) is a lower bound for 3DPass, since there are less available choices when not holding an item. Equation (3) assumes that picking up an item does not increase available choices, though in practice when an item is picked up, the next choice will follow Equation (2) instead. Both the lower bound and upper bound on the password space of 3DPass is well in excess of the standard alphanumeric approach.
In our user study, 2 participants made 3Dpasswords using only navigation, with no actions. Though the theoretical password space of a navigation-only password is still quite large, as plotted in Figure 3, in practice the password may
Figure 3. Number of possible passwords using: (1) Eqn 1; (2) Eqn 3; (3) Navigation-only, (Lnavigable)T; (4) A traditional case sensitive alphanumeric password (62T).
be vulnerable to hotspot analysis. In a full implementation, we would recommend enforcing at least 1 object grab or interaction minimum per password, resulting in the password space indicated by the lower bound calculation instead.
6. User Study
We conducted our experiment using a standard 24-inch widescreen monitor with 1920 × 1080 resolution and an Oculus Rift HMD. Interactions with the environment are recorded by the scheme directly and by video screen recording of the sessions.
We recruited 20 participants to test the memorability and usability of 3DPass. The participants were 25% female, mean age 23 (stdev = 4.5, range 17 - 32). Most participants (60%) answered yes when asked if they play 3D video games at all, and 20% of participants answered yes when asked if they had ever used VR before. On a scale from 1 (Strongly Disagree) to 5 (Strongly Agree), participants responded to the statement “I am skilled at using an Xbox controller or similar” with an average rating of 3.89.
Participants were grouped into one of two conditions:
VR: Participants in this condition used the Oculus Rift HMD for the entire experiment.
Monitor: Participants in this condition used the monitor for the entire experiment.
The grouping was done to measure the impact of stereo vision, head tracking, and motion parallax on presence, entry times, and usability ratings.
Three participants with large glasses requested to be placed in the Monitor condition due to potential discomfort wearing the HMD. Two participants requested to be placed into the Monitor condition because of concern over nausea associated with VR. Otherwise, participants were grouped at random. In total, there were 11 participants in the VR condition and 9 in the Monitor condition.
A significance level of .05 was used for hypothesis testing in this paper. Omnibus and pairwise comparisons on categorical data such as memorability are done with Chi-squared. Likert scale data and other quantitative data such as timing was analyzed with Mann Whitney Wilcoxon.
6.1. Procedure
Participants were recruited via fliers posted around the university campus. A 10 dollar cash incentive was offered for completing the experiment, and a 50 dollar prize was also raffed among participants who remembered all of their passwords as a memory incentive.
The experiment was conducted in a controlled laboratory environment. The experiment is split into two sessions, one week apart, requiring about 20 minutes and 10 minutes to complete respectively.
In the first session, participants first fill out demographic information and practice the 3DPass scheme briefly to learn the environment and the controls. The environment is reset after practice, and participants set a 3D Password, followed by a traditional alphanumeric password. The alphanumeric password is case-insensitive, must be at least 8 characters long, and does not have to relate to the 3D password. Participants then fill out a questionnaire about their 3D password, and write down the 3D password step-by-step. The environment is reset again and participants generate an additional 3D Password and an additional alphanumeric password, for a total of two of each. Before concluding the first session, participants recall the four passwords they just set in the same order that they set them.
In the second session, participants returned to the laboratory environment after one week to recall their passwords. Passwords could be recalled in any order, and users could practice in the environment beforehand to relearn the controls if they chose to.
After recalling the 3D passwords correctly, participants were asked to re-enter each 3D password an additional 3 times. Timing data was based off these attempts only. This was done in order to filter out time spent thinking and remembering from entry time.
6.2. Memorability Results
Recall rates for the two 3DPass conditions and standard alphanumeric passwords are presented in Table 1. Contrary to our expectation, there was no significant difference in memorability between the VR and Monitor conditions (χ2 = 0.839, p = 0.360). We believe a larger sample size is needed. However, as expected, 3Dpasswords are significantly more memorable than alphanumeric passwords (χ2 = 5.00, p = 0.025). We note that all 7 forgotten alphanumeric passwords belonged to the VR group. We hypothesize that going from memorizing a VR environment to memorizing a traditional alphanumeric password had some impact on user memory, and plan to investigate the effect on our future work.
6.3. Usability Results
Presence was evaluated using 14 questions from the Igroup Presence Questionnaire (IPQ) [24]. Contrary to our expectation, Mann-Whitney analysis of the scores showed no significant different in presence between the VR and Monitor conditions. Surprisingly, the mean scores for both groups were nearly identical, so we omit the score results in this paper.
Though many works have established the link between stereoscopic displays or HMDs and reported level of presence [18], other works have failed to find a
Table 1. Recall rates of 3D passwords and alphanumeric passwords (one week after initial setup).
relationship or found that traditional monoscopic displays can evoke more presence than HMD counterparts [10] [11]. Banos et al. [11] demonstrated that older models of head-mounted displays (HMDs) actually elicited a lower feeling of presence in some contexts than large 2D displays, possibly due to user discomfort with HMDs. Our results are similar. We speculate that due to the high resolution and larger size available on modern monitors, even standard displays are roughly on-par with HMDs. The large screen used in Banos’ work had a resolution of 1024 × 768, but the monitor in our experiment has a resolution of 1920 × 1080.
Timing data was collected by the application and confirmed by reviewing video screen recordings of the sessions. Time begins counting when the user first moves and ends when the user performs the last action or navigation that makes up the 3D password.
The average entry time for the VR and Monitor conditions was 20.96 and 25.93 seconds respectively. A Mann-Whitney test indicates there was a significant difference between the conditions (Z = −2.05, p = 0.040). The fastest users in each condition required 8.67 and 11.00 seconds respectively.
Four participants (two in each condition) were not included in timing results because they had never used a game controller before and were still training to use the controller as an input device during the experiment. The average entry time for these participants in the VR and Monitor conditions was 56.08 and 63.25 seconds respectively.
The results of the Likert survey are presented in Table 2. Contrary to our expectation, Mann-Whitney comparisons between the two conditions found no significant difference between the two conditions for any survey response. About half of users agreed that the 3DPass scheme was faster than a traditional alphanumeric password, and about 70% prefer 3DPass to conventional passwords. Almost all users agreed that 3DPass was fun.
6.4. Hotspots
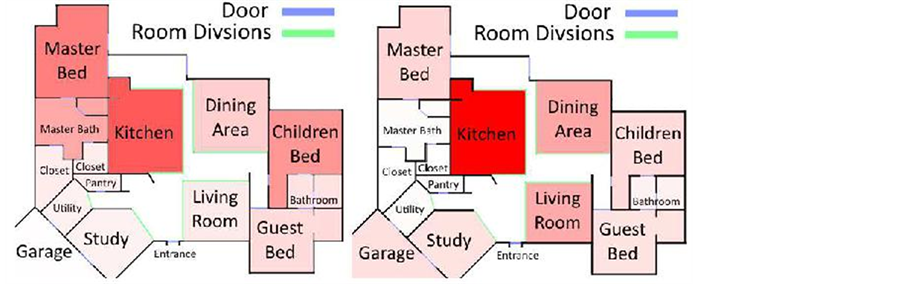
Figure 4 shows the distribution of objects in the environment and the distribution of objects and locations utilized by participants in the user study. As expected,
Table 2. Usability survey results of 3DPass (Statements scored on a Likert scale from 1-strongly disagree to 10-strongly agree. Some statements shortened for length).
Figure 4. Heat maps of the distribution of objects in the 3DPass environment (left) and the actual usage of the environment by participants in the user study (right). One use was counted if an object was picked up, dropped, thrown, or interacted with at that location, or if the user specifies navigation to that location.
the 3DPass environment itself has several areas of clustered objects, for example the kitchen, where it was natural to expect more objects than other rooms in the house. Participants were more likely to use objects near the entrance to the home, but locations all over the environment were utilized. Despite the garage having no interactable objects, simply decor, many participants chose to use this room in their 3D passwords. An attacker attempting of 3DPass may have difficulty determining which areas are most popular. The kitchen was used over twice as much as the next most used room, however 74% of participants use 2 rooms or greater, and the second room was less predictable.
7. Discussion
For navigation based portions of 3D passwords with T steps, the user must specify somehow when they reached the desired location, otherwise the attacker can simply travel the entire area of Lnavigable for T times to crack any password, which is quite trivial. The authentication attempt should also fail if a certain number of wrong locations are specified in a row, or if a specified location is very far from the correct location.
We plan to study a method for further securing navigation in our future work.
We hypothesize that several technological and cultural changes will make 3DPass entry times even more favorable. Hand/body tracking and naked-eye 3D technologies may simplify user input and allow users to navigate the environment faster and more intuitively. Presence and entry time will likely improve when users can pick up an object using a gesture rather than pressing a button, though current technologies may not have enough precision.
Eye tracking inside VR, provided by some manufacturers such as Tobii or FOVE, may improve aim speed even further, allowing users to target objects without even moving their heads. Since it is very difficult for users to refrain from moving their eyes, we hypothesize that eye tracking will be more used by novice users than head tracking. In our future work, we plan to see if eye tracking inside VR can further improve performance.
Very few VR participants used head tracking at all, opting instead to keep their heads in roughly one place for the entire experiment. Greater utilization of head tracking can lead to improved entry times (via improved aiming due to head tracking), and improved depth perception (via motion parallax). We suspect that as users become more familiar with HMDs, entry times and presence scores will improve. We plan to repeat the experiment with experienced HMD owners to test our hypothesis.
Participants created 3D passwords with an average of 1.85 objects grabbed, 3.89 interactions (including drop/throw), and 3.11 locations which were part of the 3Dpassword. Thus the average password length is about 9 choices, the equivalent of a 15 character alphanumeric password using Figure 3.
8. Conclusion
In this paper, we proposed the concept of the 3D authentication scheme, founded in various physical and psychological phenomena to improve memorability and usability. We implemented 3DPass as an example of a 3D authentication scheme. We demonstrate using 3Dpass that a 3D authentication scheme can have more robust security than a traditional alphanumeric password. We conducted a user study to determine the memorability and usability of 3DPass. Our user study shows that while presence is not improved when using an HMD in 3DPass, the 3DPass scheme when used with either an HMD or a monitor has a higher memorability than alphanumeric passwords, low entry times, favorable reviews from users, and limited hotspots.
Cite this paper
Gurary, J., Zhu, Y. and Fu, H.R. (2017) Leveraging 3D Benefits for Authentication. Int. J. Communications, Network and System Sciences, 10, 324-338. https://doi.org/10.4236/ijcns.2017.108B035
References
- 1. Li, Z.G., Han, W.L. and Xu, W.Y. (2014) A Large-Scale Empirical Analysis of Chinese Web Passwords. 23rd USENIX Security Symposium (USENIX Security 14), San Diego, 20-22 August 2014, 559-574.
- 2. Andrew, S. Patrick, A. Long, C. and Flinn, S. (2003) Hci and Security Systems. Proceedings of CHI’03 Extended Abstracts on Human Factors in Computing Systems, Florida, 05-10 April 2003, 1056-1057.
- 3. Blonder, G.E. (1996) Graphical Password. US Patent No. 5559961.
- 4. Defetyer, M., Russo, R. and McPartlin, P. (2009) The Picture Superiority Effect in Recognition Memory: A Developmental Study Using the Response Signal Procedure. Cognitive Development, 24, 265-273. https://doi.org/10.1016/j.cogdev.2009.05.002
- 5. von Zezschwitz, E., De Luca, A., Brunkow, B. and Hussmann, H. (2015) Swipin: Fast and Secure Pin-Entry on Smartphones. Proceedings of the 33rd Annual ACM Conference on Human Factors in Computing Systems, Seoul, 18-23 April 2015, 1403-1406. https://doi.org/10.1145/2702123.2702212
- 6. Bianchi, A., Oakley, I., Kostakos, V. and Kwon, D.S. (2011) The Phone Lock: Audio and Haptic Shoulder-Surfing Resistant Pin Entry Methods for Mobile Devices. Proceedings of the Fifth Interna-tional Conference on Tangible, Embedded, and Embodied Interaction, Funchal, 22-26 January 2011, 197-200. https://doi.org/10.1145/1935701.1935740
- 7. De Luca, A., Hertzschuch, K. and Hussmann, H. (2010) Colorpin: Se-curing Pin Entry through Indirect Input. Proceedings of the SIGCHI Conference on Human Factors in Computing Systems, Atlanta, 10-15 April 2010, 1103-1106. https://doi.org/10.1145/1753326.1753490
- 8. Alsulaiman, F.A. and El Saddik, A. (2008) Three-Dimensional Password for More Secure Au-Thentication. IEEE Transactions on Instrumentation and Measurement, 57, 1929-1938. https://doi.org/10.1109/TIM.2008.919905
- 9. Yu, Z., Olade, I., Liang, H.-N. and Fleming, C. (2016) Usable Authentica-tion Mechanisms for Mobile Devices: An Exploration of 3D Graphical Passwords. 2016 International Conference on Platform Technology and Service (PlatCon), Jeju, 15-17 February 2016, 1-3. https://doi.org/10.1109/PlatCon.2016.7456837
- 10. Baños, R.M., Botella, C., Rubió, I., Quero, S., Garcia-Palacios, A. and Alcañiz, M. (2008) Presence and Emotions in Virtual Environments: The Influence of Stereoscopy. CyberPsychology & Be-havior, 11, 1-8. https://doi.org/10.1089/cpb.2007.9936
- 11. Baños, R.M., Botella, C., Alcañiz, M., Liaño, V., Guerrero, B. and Rey, B. (2004) Immersion and Emotion: Their Impact on the Sense of Presence. CyberPsychology & Behavior, 7, 734-741. https://doi.org/10.1089/cpb.2004.7.734
- 12. Slater, M., Linakis, V., Usoh, M., Kooper, R. and Street, G. (1996) Immersion, Presence, and Performance in Virtual Environments: An Experiment with Tri-Dimensional Chess. In: ACM Vir-tual Reality Software and Technology (VRST). ACM Press, New York, 163-172.
- 13. Smith, E.E. Jonides, J., Koeppe, R.A., Awh, E., Schumacher, E.H. and Minoshima, S. (1995) Spatial Versus Object Working Memory: Pet Investigations. Journal of Cognitive Neuroscience, 7, 337-356. https://doi.org/10.1162/jocn.1995.7.3.337
- 14. Attree, E.A., Brooks, B.M., Rose, F.D., Andrews, T.K., Leadbetter, A.G. and Cliford, B.R. (1996) Memory Processes and Virtual Environments: I Can’t Re-member What Was There, But I Can Remember How I Got There. Implications for People with Disabilities. Proceedings of the First European Conference on Disability, Virtual Reality and Associated Technologies, Maidenhead, 08-10 July 1996, 117-120.
- 15. Tulving, E. (1972) Episodic and Semantic Memory 1. Organization of Memory. London: Academic, 381, 382-404.
- 16. Smith, S.M. (1979) Remembering in and out of Context. Journal of Experimental Psychology: Human Learning and Memory, 5, 460. https://doi.org/10.1037/0278-7393.5.5.460
- 17. IJsselsteijn, W., de Ridder, H., Freeman, J., Avons, S.E. and Bouwhuis, D. (2001) Effects of Stereoscopic Presentation, Image Motion, and Screen Size on Subjective and Objective Corroborative Measures of Presence. Presence, 10, 298-311. https://doi.org/10.1162/105474601300343621
- 18. Hendrix, C. and Barfield, W. (1996) Presence within Virtual Envi-ronments as a Function of Visual Display Parameters. Presence: Teleoperators & Virtual Environments, 5, 274-289. https://doi.org/10.1162/pres.1996.5.3.274
- 19. Barfield, W., Hendrix, C. and Bystrom, K.-E. (1999) Effects of Stereopsis and Head Tracking on Performance Using Desktop Virtual Environment Displays. Presence: Teleoperators and Virtual Envi-ronments, 8, 237-240. https://doi.org/10.1162/105474699566198
- 20. Tavanti, M. and Lind, M. (2001) 2D vs 3D, Implications on Spatial Memory. Proceedings of the IEEE Symposium on Information Visualization 2001 (INFOVIS’01), Washington DC, 22-23 Oc-tober 2001, 139-145. https://doi.org/10.1109/INFVIS.2001.963291
- 21. Isokoski, P. and Martin, B. (2006) Eye Tracker Input in First Person Shooter Games. Proceedings of the 2nd Conference on Communication by Gaze Interaction—COGAIN 2006: Gazing into the Future, Turin, 4-5 September 2006, 78-81.
- 22. Davidson, A. (2012) An Evaluation of Visual Gesture Based Controls for Exploring Three Dimensional Environments. PhD Thesis, University of Dublin, Dublin.
- 23. Coelho, J.C. and Verbeek, F.J. (2014) Pointing Task Evaluation of Leap Motion Controller in 3D Virtual Environment. Proceedings of the Chi Sparks 2014 Conference, Den Haag, 3 April 2014, 78-85.
- 24. Schubert, T., Friedmann, F. and Regenbrecht, H. (2001) The Experience of Presence: Factor Analytic Insights. Presence, 10, 266-281. https://doi.org/10.1162/105474601300343603